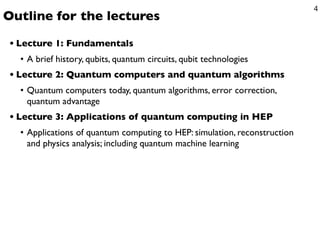
Introduction to Quantum Computing Lecture 1: Fundamentals
•
0 likes•121 views
A brief history, qubits, quantum circuits, qubit technologies
Report
Share
Report
Share
Recommended
A programming language is a notation designed to connect instructions to a machine or a computer.
Programming languages are mainly used to control the performance of a machine or to express algorithms.
At present, thousands of programming languages have been implemented.
In the computer field, many languages need to be stated in an imperative form, while other programming languages utilize declarative form.
The program can be divided into two forms such as syntax and semantics. Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi 

Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi Professor Lili Saghafi
Recommended
A programming language is a notation designed to connect instructions to a machine or a computer.
Programming languages are mainly used to control the performance of a machine or to express algorithms.
At present, thousands of programming languages have been implemented.
In the computer field, many languages need to be stated in an imperative form, while other programming languages utilize declarative form.
The program can be divided into two forms such as syntax and semantics. Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi 

Programming Languages Categories / Programming Paradigm By: Prof. Lili Saghafi Professor Lili Saghafi
A confusion matrix is a matrix (table) that can be used to measure the performance of an machine learning algorithm, usually a supervised learning one.
Each row of the confusion matrix represents the instances of an actual class and each column represents the instances of a predicted class.
This is the way we keep it like this but it can be the other way around as well, i.e. rows for predicted classes and columns for actual classes. Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...

Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...Professor Lili Saghafi
When we say "Neural Networks", we mean artificial Neural Networks (ANN). The idea of ANN is based on biological neural networks like the brain.
The basic structure of a neural network is the neuron. A neuron in biology consists of three major parts: the soma (cell body), the dendrites, and the axon.
The dendrites branch of from the soma in a tree-like way and getting thinner with every branch. They receive signals (impulses) from other neurons at synapses. The axon - there is always only one - also leaves the soma and usually tend to extend for longer distances than the dentrites. The axon is used for sending the output of the neuron to other neurons or better to the synapsis of other neurons.
Machine learning by using python lesson 2 Neural Networks By Professor Lili S...

Machine learning by using python lesson 2 Neural Networks By Professor Lili S...Professor Lili Saghafi
The experimental implementation of Quantum Computers and Improved quantum error correction could enable universal quantum computing. In a way that can change the world .Quantum Computers_Superposition Interference Entanglement and Quantum Error C...

Quantum Computers_Superposition Interference Entanglement and Quantum Error C...Professor Lili Saghafi
More Related Content
More from Professor Lili Saghafi
A confusion matrix is a matrix (table) that can be used to measure the performance of an machine learning algorithm, usually a supervised learning one.
Each row of the confusion matrix represents the instances of an actual class and each column represents the instances of a predicted class.
This is the way we keep it like this but it can be the other way around as well, i.e. rows for predicted classes and columns for actual classes. Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...

Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...Professor Lili Saghafi
When we say "Neural Networks", we mean artificial Neural Networks (ANN). The idea of ANN is based on biological neural networks like the brain.
The basic structure of a neural network is the neuron. A neuron in biology consists of three major parts: the soma (cell body), the dendrites, and the axon.
The dendrites branch of from the soma in a tree-like way and getting thinner with every branch. They receive signals (impulses) from other neurons at synapses. The axon - there is always only one - also leaves the soma and usually tend to extend for longer distances than the dentrites. The axon is used for sending the output of the neuron to other neurons or better to the synapsis of other neurons.
Machine learning by using python lesson 2 Neural Networks By Professor Lili S...

Machine learning by using python lesson 2 Neural Networks By Professor Lili S...Professor Lili Saghafi
The experimental implementation of Quantum Computers and Improved quantum error correction could enable universal quantum computing. In a way that can change the world .Quantum Computers_Superposition Interference Entanglement and Quantum Error C...

Quantum Computers_Superposition Interference Entanglement and Quantum Error C...Professor Lili Saghafi
More from Professor Lili Saghafi (20)
Cyber Security and Post Quantum Cryptography By: Professor Lili Saghafi

Cyber Security and Post Quantum Cryptography By: Professor Lili Saghafi
Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...

Machine learning by using python lesson 3 Confusion Matrix By : Professor Lil...
Machine learning by using python lesson 2 Neural Networks By Professor Lili S...

Machine learning by using python lesson 2 Neural Networks By Professor Lili S...
Machine learning by using python Lesson One Part 2 By Professor Lili Saghafi

Machine learning by using python Lesson One Part 2 By Professor Lili Saghafi
Machine learning by using python By: Professor Lili Saghafi

Machine learning by using python By: Professor Lili Saghafi
What is digital humanities ,By: Professor Lili Saghafi

What is digital humanities ,By: Professor Lili Saghafi
Effective Algorithm for n Fibonacci Number By: Professor Lili Saghafi

Effective Algorithm for n Fibonacci Number By: Professor Lili Saghafi
Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili Saghafi

Computer Security Cyber Security DOS_DDOS Attacks By: Professor Lili Saghafi
New Assessments in Higher Education with Computers by: Prof Lili Saghafi 

New Assessments in Higher Education with Computers by: Prof Lili Saghafi
Quantum Computers_Superposition Interference Entanglement and Quantum Error C...

Quantum Computers_Superposition Interference Entanglement and Quantum Error C...
Advanced Programming _Abstract Classes vs Interfaces (Java)

Advanced Programming _Abstract Classes vs Interfaces (Java)
Writing a Research Essay or Literature Review Paper

Writing a Research Essay or Literature Review Paper
Quantum computers new generation of computers part10 New Qubits Type

Quantum computers new generation of computers part10 New Qubits Type
Recently uploaded
TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J. Tortora, Verified Chapters 1 - 29, Complete Newest Version.TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....

TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....rightmanforbloodline
Recently uploaded (20)
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Less Is More: Utilizing Ballerina to Architect a Cloud Data Platform

Less Is More: Utilizing Ballerina to Architect a Cloud Data Platform
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....

TEST BANK For Principles of Anatomy and Physiology, 16th Edition by Gerard J....
Introduction to Multilingual Retrieval Augmented Generation (RAG)

Introduction to Multilingual Retrieval Augmented Generation (RAG)
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
JavaScript Usage Statistics 2024 - The Ultimate Guide

JavaScript Usage Statistics 2024 - The Ultimate Guide
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
ChatGPT and Beyond - Elevating DevOps Productivity

ChatGPT and Beyond - Elevating DevOps Productivity
How to Check CNIC Information Online with Pakdata cf

How to Check CNIC Information Online with Pakdata cf
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf

Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf
Elevate Developer Efficiency & build GenAI Application with Amazon Q

Elevate Developer Efficiency & build GenAI Application with Amazon Q
