Redesigning Security Operations Term Paper
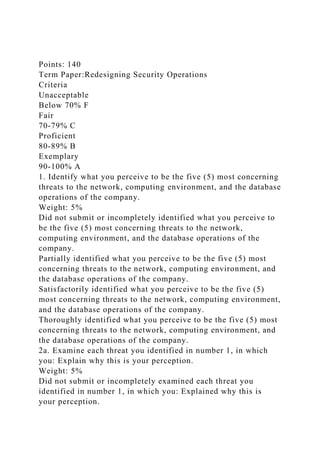
- 1. Points: 140 Term Paper:Redesigning Security Operations Criteria Unacceptable Below 70% F Fair 70-79% C Proficient 80-89% B Exemplary 90-100% A 1. Identify what you perceive to be the five (5) most concerning threats to the network, computing environment, and the database operations of the company. Weight: 5% Did not submit or incompletely identified what you perceive to be the five (5) most concerning threats to the network, computing environment, and the database operations of the company. Partially identified what you perceive to be the five (5) most concerning threats to the network, computing environment, and the database operations of the company. Satisfactorily identified what you perceive to be the five (5) most concerning threats to the network, computing environment, and the database operations of the company. Thoroughly identified what you perceive to be the five (5) most concerning threats to the network, computing environment, and the database operations of the company. 2a. Examine each threat you identified in number 1, in which you: Explain why this is your perception. Weight: 5% Did not submit or incompletely examined each threat you identified in number 1, in which you: Explained why this is your perception.
- 2. Partially examined each threat you identified in number 1, in which you: Explained why this is your perception. Satisfactorily examined each threat you identified in number 1, in which you: Explained why this is your perception. Thoroughly examined each threat you identified in number 1, in which you: Explained why this is your perception. 2b. Examine each threat you identified in number 1, in which you: Identify what is at risk from these threats. Weight: 5% Did not submit or incompletely examined each threat you identified in number 1, in which you: Identified what is at risk from these threats. Partially examined each threat you identified in number 1, in which you: Identified what is at risk from these threats. Satisfactorily examined each threat you identified in number 1, in which you: Identified what is at risk from these threats. Thoroughly examined each threat you identified in number 1, in which you: Identified what is at risk from these threats. 2c. Examine each threat you identified in number 1, in which you: Determine how you would design the security controls to mitigate the risks involved. Weight: 5% Did not submit or incompletely examined each threat you identified in number 1, in which you: Determined how you would design the security controls to mitigate the risks involved. Partially examined each threat you identified in number 1, in which you: Determined how you would design the security controls to mitigate the risks involved. Satisfactorily examined each threat you identified in number 1, in which you: Determined how you would design the security controls to mitigate the risks involved. Thoroughly examined each threat you identified in number 1, in which you: Determined how you would design the security controls to mitigate the risks involved. 3. Determine the security defense mechanisms that you would
- 3. utilize in order to secure communications from floor to floor in the office space, including equipment and physical controls. Weight: 5% Did not submit or incompletely determined the security defense mechanisms that you would utilize in order to secure communications from floor to floor in the office space, including equipment and physical controls. Partially determined the security defense mechanisms that you would utilize in order to secure communications from floor to floor in the office space, including equipment and physical controls. Satisfactorily determined the security defense mechanisms that you would utilize in order to secure communications from floor to floor in the office space, including equipment and physical controls. Thoroughly determined the security defense mechanisms that you would utilize in order to secure communications from floor to floor in the office space, including equipment and physical controls. 4. Create an office space diagram detailing the security defense tools, equipment and controls utilized, using a diagramming application such as Visio or Dia. Weight: 15% Did not submit or incompletely created an office space diagram detailing the security defense tools, equipment and controls utilized, using a diagramming application such as Visio or Dia. Partially created an office space diagram detailing the security defense tools, equipment and controls utilized, using a diagramming application such as Visio or Dia. Satisfactorily created an office space diagram detailing the security defense tools, equipment and controls utilized, using a diagramming application such as Visio or Dia. Thoroughly created an office space diagram detailing the security defense tools, equipment and controls utilized, using a diagramming application such as Visio or Dia. 5. Explain in detail the defensive mechanisms that you would
- 4. implement to secure the corporate wireless network, including encryption, authentication methods, and at least two (2) WLAN security tools you would utilize on a regular basis. Weight: 5% Did not submit or incompletely explained in detail the defensive mechanisms that you would implement to secure the corporate wireless network, including encryption, authentication methods, and at least two (2) WLAN security tools you would utilize on a regular basis. Partially explained in detail the defensive mechanisms that you would implement to secure the corporate wireless network, including encryption, authentication methods, and at least two (2) WLAN security tools you would utilize on a regular basis. Satisfactorily explained in detail the defensive mechanisms that you would implement to secure the corporate wireless network, including encryption, authentication methods, and at least two (2) WLAN security tools you would utilize on a regular basis. Thoroughly explained in detail the defensive mechanisms that you would implement to secure the corporate wireless network, including encryption, authentication methods, and at least two (2) WLAN security tools you would utilize on a regular basis. 6. Create a wireless network diagram, using a diagramming application such as Visio or Dia based on your explanation in number 5. Weight: 15% Did not submit or incompletely created a wireless network diagram, using a diagramming application such as Visio or Dia based on your explanation in number 5. Partially created a wireless network diagram, using a diagramming application such as Visio or Dia based on your explanation in number 5. Satisfactorily created a wireless network diagram, using a diagramming application such as Visio or Dia based on your
- 5. explanation in number 5. Thoroughly created a wireless network diagram, using a diagramming application such as Visio or Dia based on your explanation in number 5. 7. Determine whether or not you would utilize encryption technologies on the network and / or computing equipment. Justify your response. Weight: 5% Did not submit or incompletely determined whether or not you would utilize encryption technologies on the network and / or computing equipment; did not submit or incompletely justified your response. Partially determined whether or not you would utilize encryption technologies on the network and / or computing equipment; partially justified your response. Satisfactorily determined whether or not you would utilize encryption technologies on the network and / or computing equipment; satisfactorily justified your response. Thoroughly determined whether or not you would utilize encryption technologies on the network and / or computing equipment; thoroughly justified your response. 8. Consider the use of a cloud-based solution for storing the company’s data. Determine the benefits and / or risks that would result using this kind of data storage, and decide whether or not you would utilize this storage option. Justify your decision. Weight: 5% Did not submit or incompletely considered the use of a cloud- based solution for storing the company’s data; did not submit or incompletely determined the benefits and / or risks that would result using this kind of data storage, and did not submit or incompletely decided whether or not you would utilize this storage option; did not submit or incompletely justified your decision. Partially considered the use of a cloud-based solution for storing the company’s data; partially determined the benefits
- 6. and / or risks that would result using this kind of data storage, and partially decided whether or not you would utilize this storage option; partially justified your decision. Satisfactorily considered the use of a cloud-based solution for storing the company’s data; satisfactorily determined the benefits and / or risks that would result using this kind of data storage, and satisfactorily decided whether or not you would utilize this storage option; satisfactorily justified your decision. Thoroughly considered the use of a cloud-based solution for storing the company’s data; thoroughly determined the benefits and / or risks that would result using this kind of data storage, and thoroughly decided whether or not you would utilize this storage option; thoroughly justified your decision. 9. Select a minimum of five (5) security tools that you would implement on the network as security auditing and / or defense countermeasures. Weight: 5% Did not submit or incompletely selected a minimum of five (5) security tools that you would implement on the network as security auditing and / or defense countermeasures. Partially selected a minimum of five (5) security tools that you would implement on the network as security auditing and / or defense countermeasures. Satisfactorily selected a minimum of five (5) security tools that you would implement on the network as security auditing and / or defense countermeasures. Thoroughly selected a minimum of five (5) security tools that you would implement on the network as security auditing and / or defense countermeasures. 10. Analyze each security tool you selected in number 8, and determine why / how you would use them as part of your security operations. Weight: 5% Did not submit or incompletely analyzed each security tool you selected in number 8; did not submit or incompletely determined why / how you would use them as part of your
- 7. security operations. Partially analyzed each security tool you selected in number 8; partially determined why / how you would use them as part of your security operations. Satisfactorily analyzed each security tool you selected in number 8; satisfactorily determined why / how you would use them as part of your security operations. Thoroughly analyzed each security tool you selected in number 8; thoroughly determined why / how you would use them as part of your security operations. 11. Provide an overview of the recovery and continuity plans you would develop to ensure the company could survive a temporary or prolonged disruption. Explain why each plan is needed based on the benefits it provides to the company. Weight: 5% Did not submit or incompletely provided an overview of the recovery and continuity plans you would develop to ensure the company could survive a temporary or prolonged disruption; did not submit or incompletely explained why each plan is needed based on the benefits it provides to the company. Partially provided an overview of the recovery and continuity plans you would develop to ensure the company could survive a temporary or prolonged disruption; partially explained why each plan is needed based on the benefits it provides to the company. Satisfactorily provided an overview of the recovery and continuity plans you would develop to ensure the company could survive a temporary or prolonged disruption; satisfactorily explained why each plan is needed based on the benefits it provides to the company. Thoroughly provided an overview of the recovery and continuity plans you would develop to ensure the company could survive a temporary or prolonged disruption; thoroughly explained why each plan is needed based on the benefits it provides to the company. 12. 5 references Weight: 5%
- 8. No references provided Does not meet the required number of references; some or all references poor quality choices. Meets number of required references; all references high quality choices. Exceeds number of required references; all references high quality choices. 13. Clarity, writing mechanics, and formatting requirements Weight: 10% More than 6 errors present 5-6 errors present 3-4 errors present 0-2 errors present 1. Use the ANES 2016 data set to set out where you expect public opinion to stand on three key policy issues that you intend to stress in your campaign. At least one of these issues should be different from the three you analyzed for Project 1. Include frequency tables (charts) and graphs outlining the results for each of these three issues.
- 10. 2. Perform a crosstabulation of each of these three issues by a demographic variable. You can use a different demographic variable for each issues, and at least one of these demographic variables should be different from those you used in Project 1. Include frequency tables (charts) and graphs outlining the crosstabulation for each of these three issues. Project 2 (15 points—15% of final grade) Getting Elected President in 2020
- 11. PROJECT # 2 Getting elected in 2020. Imagine you are intending to run for President in 2020. To have a realistic chance of election, you must run either as a Democrat or a Republican, and you should say which you are running as. Your two main goals are (i) to win the 2020 Presidential election, which also involves winning your chosen party’s primary election in order to get the party’s nomination (ii) to campaign on issues, and policies related to those issues, that you believe in and that you would actually like to implement. You will certainly need to make some compromises here in balancing these two goals (e.g. your preferred policy stance on a particular issue might make you unelectable, in which case you probably should not advocate for it). You should, in your written project, explain these considerations. 1. Use the ANES 2016 data set to set out where you expect public opinion to stand on three key policy issues that you intend to stress in your campaign to be elected President in 2020. At least one of these issues should be different from the three you analyzed for Project 1. Include in your written project a chart outlining the results for each of these three issues. 1. Perform a crosstabulation of each of these three issues by a demographic variable (can be a different demographic variable for each issue or the same one for each issue), and at least one of these demographic variables should be different from those you used in Project 1. Include in your written project a chart outlining the crosstabulation for each of these three issues. 1. Go online and search one or more of the LA Times, New York Times, Washington Post or Wall Street Journal, or any other major source of current polls, and look in them for recent (preferably last six months) survey data. Use these polls to supplement your analysis for at least one of your policy variables.. Examples of Key Issues (you may select different issues than these): economic issues especially the state of the economy; financial reform in the light of the recent financial/economic
- 12. crisis; health care/health care reform; key foreign policy issues including the wars in Iraq, Afghanistan and Syria, upheavals in the Middle East, the associated refugee crises, attitudes to China and Russia; the issue of North Korea’s missile capabilities, and the US-Mexico relationship; terrorism; social issues (e.g. abortion, gay rights, women’s rights); government (how corrupt, whom it serves etc); religion; attitudes to minorities. Write a campaign memo addressed to your election staff (i.e. this is your written project), explaining to your staff what stance you and the campaign should take on these three issues in order to maximize a favorable electoral outcome in 2020. Base your views on the survey data you have researched, and refer to the survey data/charts. As written above, remember that your two main goals are (i) to win the 2020 Presidential election, which also involves winning your chosen party’s primary election in order to get the party’s nomination (ii) to campaign on issues, and policies related to those issues, that you believe in and that you would actually like to implement. You will certainly need to make some compromises here in balancing these two goals (e.g. your preferred policy stance on a particular issue might make you unelectable, in which case you probably should not advocate for it). You should, in your written project, explain these considerations. Maximum length of text for Project 2 should be 2 single spaced pages, plus any graphs or tables.. Campaign video (optional) For an extra 3 bonus points students can produce a campaign video (2 mins max). You should base the video on your campaign memo, but instead of a memo the video should be a campaign speech. At the very start of the video you should state the intended audience for your video (e.g. primary party voters in a particular state e.g. national tv audience e.g. factory workers e.g. students etc). Upload the video to youtube, and then include the link in a word
- 13. doc that you submit in the assigned place.