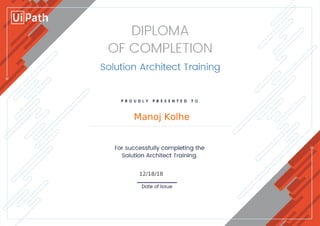
UiPath_RPA Solution Architect - Completion Diploma
•
0 likes•5 views
UIPath RPA
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
More from Manoj Kolhe
More from Manoj Kolhe (6)
Manoj Kolhe - Setup GitHub with Jenkins on Amazon Cloud - End-to-end Automation

Manoj Kolhe - Setup GitHub with Jenkins on Amazon Cloud - End-to-end Automation
Recently uploaded
Recently uploaded (20)
Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx

Harnessing Passkeys in the Battle Against AI-Powered Cyber Threats.pptx
ChatGPT and Beyond - Elevating DevOps Productivity

ChatGPT and Beyond - Elevating DevOps Productivity
“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf

“Iamnobody89757” Understanding the Mysterious of Digital Identity.pdf
AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)

AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)
Cyber Insurance - RalphGilot - Embry-Riddle Aeronautical University.pptx

Cyber Insurance - RalphGilot - Embry-Riddle Aeronautical University.pptx
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
Tales from a Passkey Provider Progress from Awareness to Implementation.pptx

Tales from a Passkey Provider Progress from Awareness to Implementation.pptx
Human Expert Website Manual WCAG 2.0 2.1 2.2 Audit - Digital Accessibility Au...

Human Expert Website Manual WCAG 2.0 2.1 2.2 Audit - Digital Accessibility Au...
How to Check CNIC Information Online with Pakdata cf

How to Check CNIC Information Online with Pakdata cf
TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...

TrustArc Webinar - Unified Trust Center for Privacy, Security, Compliance, an...
Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)

Observability Concepts EVERY Developer Should Know (DevOpsDays Seattle)
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
UiPath_RPA Solution Architect - Completion Diploma
- 1. Manoj Kolhe 12/18/18 Powered by TCPDF (www.tcpdf.org)
