PAMaaS- Powered by CyberArk
•
0 likes•8 views
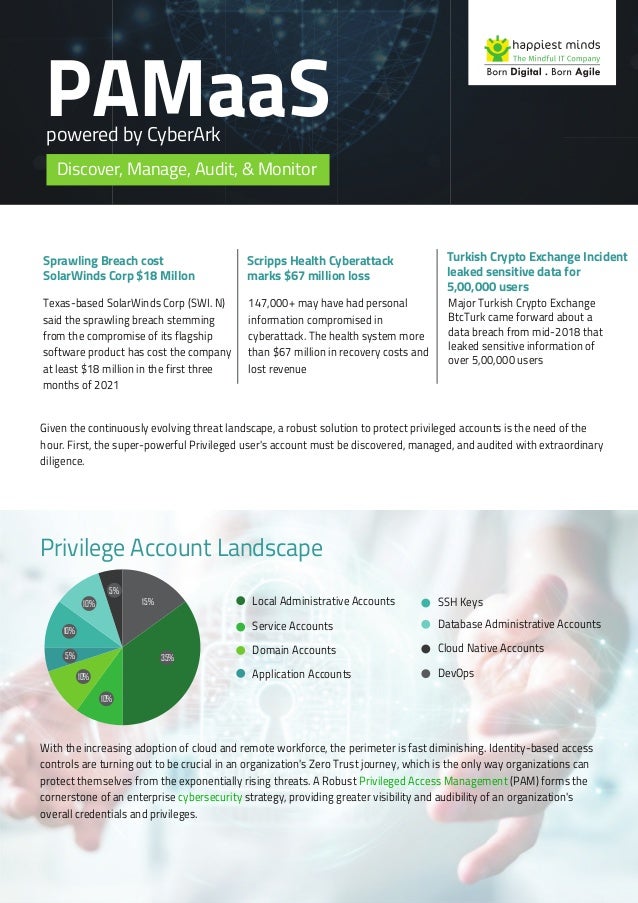
A Robust Privileged Access Management (PAM) forms the cornerstone of an enterprise cybersecurity strategy, providing greater visibility and audibility of an organization's overall credentials and privileges.
Report
Share
Report
Share
Download to read offline
Recommended
Through “Authentication Solution Providers 2019” issue, Insights Success takes an initiative in addressing some of the finest organizations who stand forth in delivering best authentication solutions at one’s door.
The 10 most trusted authentication solution providers 2018

The 10 most trusted authentication solution providers 2018Insights success media and technology pvt ltd
Recommended
Through “Authentication Solution Providers 2019” issue, Insights Success takes an initiative in addressing some of the finest organizations who stand forth in delivering best authentication solutions at one’s door.
The 10 most trusted authentication solution providers 2018

The 10 most trusted authentication solution providers 2018Insights success media and technology pvt ltd
Whether you are already utilizing Office 365 or are planning to move, it's important to understand the ever-changing security threat landscape and how you can protect your digital estate.
Don't miss our webinar to learn how to proactively safeguard your company against threats with the help of Microsoft 365.
Int his webinar we address the security challenges we are seeing in 2020 and show you areas of Microsoft 365 that can help you:
- Protect and govern data where it lives
- Identify and remediate critical insider risks
- Investigate and respond with relevant data
Webinar: Microsoft 365 - Your Gateway to Data Loss Prevention

Webinar: Microsoft 365 - Your Gateway to Data Loss PreventionWithumSmith+Brown, formerly Portal Solutions
More Related Content
Similar to PAMaaS- Powered by CyberArk
Whether you are already utilizing Office 365 or are planning to move, it's important to understand the ever-changing security threat landscape and how you can protect your digital estate.
Don't miss our webinar to learn how to proactively safeguard your company against threats with the help of Microsoft 365.
Int his webinar we address the security challenges we are seeing in 2020 and show you areas of Microsoft 365 that can help you:
- Protect and govern data where it lives
- Identify and remediate critical insider risks
- Investigate and respond with relevant data
Webinar: Microsoft 365 - Your Gateway to Data Loss Prevention

Webinar: Microsoft 365 - Your Gateway to Data Loss PreventionWithumSmith+Brown, formerly Portal Solutions
Similar to PAMaaS- Powered by CyberArk (20)
Case Study - Digital HRMS a customizable & modular HR platform to drive your ...

Case Study - Digital HRMS a customizable & modular HR platform to drive your ...
Presentación Dell, Omega Peripherals e Intel: El centro de datos eficiente (1...

Presentación Dell, Omega Peripherals e Intel: El centro de datos eficiente (1...
Best Software Development Company |Salesforce Consulting Services in Singapor...

Best Software Development Company |Salesforce Consulting Services in Singapor...
Ideaworks Solutions Pvt Ltd- Mobile Application Development

Ideaworks Solutions Pvt Ltd- Mobile Application Development
Indonesia new default short msp client presentation partnership with isv

Indonesia new default short msp client presentation partnership with isv
Case study: Role Based Provisioning - Happiest Minds

Case study: Role Based Provisioning - Happiest Minds
Webinar: Microsoft 365 - Your Gateway to Data Loss Prevention

Webinar: Microsoft 365 - Your Gateway to Data Loss Prevention
More from Happiest Minds Technologies
The banking, financial services, and insurance (BFSI)
sector has been at the forefront of adopting AI and
machine learning technologies. AI has enabled these
industries to automate processes, reduce costs, and
improve the customer experience. With the advent of
digitization and the increasing amount of data available,
banking, financial services, and insurance companies have
been leaders in using AI and machine learning.Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance

Exploring the Potential of ChatGPT in Banking, Financial SERVICES & InsuranceHappiest Minds Technologies
Client is the leader in work orchestration and observability. Software platform helps enterprises more effectively plan, orchestrate and audit the human and automated activities that drive critical events, such as technology releases, resilience testing, operational readiness and major incident recovery.Automating SOC1/2 Compliance- For a leading Software solution company in UK

Automating SOC1/2 Compliance- For a leading Software solution company in UKHappiest Minds Technologies
The global disruption due to the pandemic has massively impacted organizations and the way they function.
Organizations are shifting towards a virtual environment by adopting cloud and automation to support,
monitor, and deploy exceptional service to their end-users. But how to keep the end-users connected to the
digital workplace securely during disruption is a big challengeGUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...

GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...Happiest Minds Technologies
Aure Bastion is a PaaS solution for your remote desktop which is more secure than the
jump server. It comes with web-based login, and never expose VM public IP to the
internet. This service will work seamlessly on your environment using VM’s private IP
address within your Vnet. Highly secure and trustable.Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)

Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)Happiest Minds Technologies
The Retail industry today is dealing with the concerning challenge of rising costs of transportation,
driven by a shortage of trucks and truck drivers, availability of raw material and unprecedented
demand spikes across categories. Retailers like Bed Bath & Beyond have recently warned investors
about the impact of rising freight costs on earnings. As overall freight costs can constitute up to
10% of total expenditure, efficiency in freight invoice management is critical to managing
transportation budgetsREDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDITHappiest Minds Technologies
The Retail industry today is dealing with the concerning challenge of rising costs of transportation,
driven by a shortage of trucks and truck drivers, availability of raw material and unprecedented
demand spikes across categories. Retailers like Bed Bath & Beyond have recently warned investors
about the impact of rising freight costs on earnings. As overall freight costs can constitute up to
10% of total expenditure, efficiency in freight invoice management is critical to managing
transportation budgets.
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDITHappiest Minds Technologies
More from Happiest Minds Technologies (20)
Largest Electricity provider in the US- Case Study

Largest Electricity provider in the US- Case Study
Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance

Exploring the Potential of ChatGPT in Banking, Financial SERVICES & Insurance
AUTOMATING CYBER RISK DETECTION AND PROTECTION WITH SOC 2.0

AUTOMATING CYBER RISK DETECTION AND PROTECTION WITH SOC 2.0
Automating SOC1/2 Compliance- For a leading Software solution company in UK

Automating SOC1/2 Compliance- For a leading Software solution company in UK
GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...

GUIDE TO KEEP YOUR END-USERS CONNECTED TO THE DIGITAL WORKPLACE DURING DISRUP...
Complete Guide to General Data Protection Regulation (GDPR)

Complete Guide to General Data Protection Regulation (GDPR)
Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)

Azure bastion- Remote desktop RDP/SSH in Azure using Bastion Service as (PaaS)
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT
REDUCING TRANSPORTATION COSTS IN CPG THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN CPG THROUGH INTELLIGENT FREIGHT AUDIT
REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT

REDUCING TRANSPORTATION COSTS IN RETAIL THROUGH INTELLIGENT FREIGHT AUDIT
Recently uploaded
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Recently uploaded (20)
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
CNIC Information System with Pakdata Cf In Pakistan

CNIC Information System with Pakdata Cf In Pakistan
Finding Java's Hidden Performance Traps @ DevoxxUK 2024

Finding Java's Hidden Performance Traps @ DevoxxUK 2024
Introduction to Multilingual Retrieval Augmented Generation (RAG)

Introduction to Multilingual Retrieval Augmented Generation (RAG)
WSO2's API Vision: Unifying Control, Empowering Developers

WSO2's API Vision: Unifying Control, Empowering Developers
Choreo: Empowering the Future of Enterprise Software Engineering

Choreo: Empowering the Future of Enterprise Software Engineering
WSO2 Micro Integrator for Enterprise Integration in a Decentralized, Microser...

WSO2 Micro Integrator for Enterprise Integration in a Decentralized, Microser...
AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)

AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)
"I see eyes in my soup": How Delivery Hero implemented the safety system for ...

"I see eyes in my soup": How Delivery Hero implemented the safety system for ...
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model

Mcleodganj Call Girls 🥰 8617370543 Service Offer VIP Hot Model
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
PAMaaS- Powered by CyberArk
- 1. PAMaaS Texas-based SolarWinds Corp (SWI. N) said the sprawling breach stemming from the compromise of its flagship software product has cost the company at least $18 million in the first three months of 2021 Given the continuously evolving threat landscape, a robust solution to protect privileged accounts is the need of the hour. First, the super-powerful Privileged user's account must be discovered, managed, and audited with extraordinary diligence. With the increasing adoption of cloud and remote workforce, the perimeter is fast diminishing. Identity-based access controls are turning out to be crucial in an organization's Zero Trust journey, which is the only way organizations can protect themselves from the exponentially rising threats. A Robust Privileged Access Management (PAM) forms the cornerstone of an enterprise cybersecurity strategy, providing greater visibility and audibility of an organization's overall credentials and privileges. powered by CyberArk Discover, Manage, Audit, & Monitor Sprawling Breach cost SolarWinds Corp $18 Millon 147,000+ may have had personal information compromised in cyberattack. The health system more than $67 million in recovery costs and lost revenue Scripps Health Cyberattack marks $67 million loss Major Turkish Crypto Exchange BtcTurk came forward about a data breach from mid-2018 that leaked sensitive information of over 5,00,000 users Turkish Crypto Exchange Incident leaked sensitive data for 5,00,000 users Privilege Account Landscape Local Administrative Accounts Service Accounts Domain Accounts Application Accounts SSH Keys Database Administrative Accounts Cloud Native Accounts DevOps 10% 10% 5% 10% 10% 5% 15% 35%
- 2. However, many enterprises struggle with privileged access management (PAM) for several reasons Why to choose Happiest Minds PAMaaS? 01 Human Error & Exploitation 02 Complex IT architecture and technology 03 Lack of qualified workers 04 Ever-changing regulatory requirements 07 Lack of comprehensive threat analysis tools 05 Lack of Automation/dependent on the manual process 06 No central monitor and control Happiest Minds Privileged Access Management as a Service (PAMaaS)- powered by CyberArk provides organizations with one stop solution to address their privilege account management requirements end to end. Happiestminds PAMaaS leverages the strong security controls provided by CyberArk and presents our customers with flexible deployment options, lower TCO, faster ROI, easier adoption of industry best practices and is heralded by certified professionals and Cybersecurity Leaders. Business Contact About Happiest Minds Technologies Happiest Minds Technologies Limited (NSE: HAPPSTMNDS), a Mindful IT Company, enables digital transformation for enterprises and technology providers by delivering seamless customer experiences, business efficiency and actionable insights. We do this by leveraging a spectrum of disruptive technologies such as: artificial intelligence, blockchain, cloud, digital process automation, internet of things, robotics / drones, security, virtual/augmented reality, etc. Positioned as ‘Born Digital. Born Agile’, our capabilities span digital solutions, infrastructure, product engineering and security. We deliver these services across industry sectors such as automotive, BFSI, consumer packaged goods, e- commerce, edutech, engineering R&D, hi-tech, manufacturing, retail and travel/transportation/hospitality. A Great Place to Work-Certified™ Company, Happiest Minds is headquartered in Bangalore, India with operations in the U.S., UK, Canada, Australia and Middle East. www.happiestminds.com All in one Pricing • End to End accountability • Product Licensing • Strategic planning and Solution Design • Deployment & Maintenance. • Robust Governance Framework and clear communication Design, Implement & Integrate • Built-in redundancy with High Availability and Disaster Recovery on distributed geo-locations • Multiple Deployment methodology – SaaS, cloud or on-premise Assess & Enhance Operate & Support • Highly Scalable and extendable design approach for agility • Certified consultants with referenceable credentials and domain expertise • Virtual CTO consulting for PAM advisory and best practice recommendation • Flexible BAU Support options: • 8X5 ; 24X7 ; 24X5 • On call support • L1/L2 ; L3 only or L1/L2/L3 support 01 02 03 04 PAM Managed Services (PAMaaS) Powered by Hardened and Encrypted Vault Credential Protection & Management Isolate, Monitor and Record Sessions Least Privilege Access RPA & Bot Management Privilege Threat Analytics DevOps Password Mgmt. Third Party Access End-point Privilege Access OPTIONAL ADD - ONs CORE FEATURES Disclaimer: All logos are the property of their respective owners
