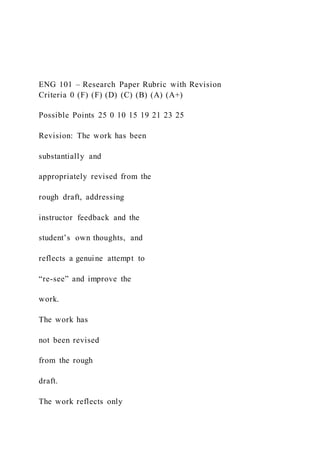
ENG 101 – Research Paper Rubric with Revision Criteria 0 (F)
- 1. ENG 101 – Research Paper Rubric with Revision Criteria 0 (F) (F) (D) (C) (B) (A) (A+) Possible Points 25 0 10 15 19 21 23 25 Revision: The work has been substantially and appropriately revised from the rough draft, addressing instructor feedback and the student’s own thoughts, and reflects a genuine attempt to “re-see” and improve the work. The work has not been revised from the rough draft. The work reflects only
- 2. minimal efforts at revision. Most significant problems have not been addressed. The work reflects minimal efforts at revision. Many significant problems have not been addressed. The work reflects some efforts at revision. The most pressing problems from the rough draft have been addressed in some
- 3. form but may remain problematic. Revision may be limited to corrections pointed out by the instructor in rough draft feedback. The work reflects significant efforts at revision. The most pressing problems from the rough draft have been addressed, and many have been resolved. Revision reflects a genuine
- 4. effort to “re-see” the work and goes beyond corrections noted on the rough draft by the instructor. The work reflects considerable efforts at revision. The most pressing problems in the rough draft have been addressed, and most have been resolved. Revision reflects a genuine effort to “re-see” the
- 5. work and goes beyond corrections noted on the rough draft by the instructor. The work reflects thorough and consistent efforts at revision. The most pressing problems in the rough draft have been addressed, and most have been resolved successfully. Revision reflects a genuine effort to “re- see” the work and goes well beyond corrections noted on
- 6. the rough draft by the instructor. Possible Points 10 0 4 6 7 8 9 10 Thesis: The work contains an appropriate, original, and coherent thesis statement which is reinforced throughout the paper. No submission. The work has no theme/thesis statement. The work’s theme/thesis statement is difficult to identify, unoriginal, and/or is not reinforced throughout the paper. The work’s
- 7. theme/thesis statement is acceptable, but elementary, occasionally used in the rest of the work. The work’s theme/thesis statement is original and mostly developed, consistently used throughout the work. The work’s theme/thesis statement is original, thoroughly
- 8. developed, and reinforced throughout the paper. The work’s theme/thesis statement is original, completely developed, clearly articulated, and coherently unites the content. Possible Points 15 0 6 9 11 13 14 15 Analysis, argument, evaluation, or methods: The work demonstrates original and effective analysis, argumentation, evaluation, critical thinking,
- 9. and/or the use of appropriate research methods, as applicable to the assignment. No submission. The work demonstrates a complete lack of any analysis, argument construction, evaluation, and/or methodology as applicable to the assignment, and/or the ideas are not original. The work demonstrates a basic, simplistic attempt at original analysis,
- 10. argument construction, evaluation, and/or methodology as applicable to the assignment. The work inconsistently demonstrates some efforts at original analysis, argument construction, evaluation, and/or methodology as applicable to the assignment. The work demonstrates the
- 11. consistent use of original analysis, argument construction, evaluation, and/or methodology as applicable to the assignment at an acceptable level. The work demonstrates application of analysis, argument construction, evaluation, and/or methodology as applicable to the assignment, in a
- 12. thorough, original, and well-reasoned presentation. The work is built around an original, well-constructed analysis, argument, evaluation, and/or methodology as applicable to the assignment, meeting all expectations. Possible Points 15 0 6 9 11 13 14 15 Criteria 0 (F) (F) (D) (C) (B) (A) (A+) Structure/organization: The work has a well-crafted
- 13. structure and organization, including an introduction, body, and discussion/conclusion, as appropriate to the assignment. The work contains effective transitions and/or topic sentences that build upon the central theme or thesis. No submission. The work shows no obvious organization, lacking a clear introduction, body, and conclusion. The work shows a basic attempt to organize the material,
- 14. struggling to differentiate the introduction, body, and conclusion. Transitions often show little or no relationship to the theme/thesis. The work shows an acceptable structure and organization, with an identifiable introduction, body, and conclusion. Transitions are somewhat related to the theme/thesis. The work is well structured and
- 15. organized, with an adequate introduction, body, and conclusion. Transitions often link to the theme/thesis. The work follows an easily identifiable structure and organization, with a clearly articulated introduction, body, and conclusion. Transitions are appropriate and all link to the theme/thesis.
- 16. The work is built around a clearly identifiable structure and organization, which brings a better understanding for the reader with a fully articulated introduction, body, and conclusion. Transitions are smooth and fully support the theme/thesis. Possible Points 15 0 6 9 11 13 14 15 Sources/evidence: The work demonstrates the selection and use of an appropriate quantity and
- 17. quality of sources, evidence, and/or information as appropriate to the assignment. No submission. The work contains no sources/evidence or sources/evidence does not meet the quality and/or quantity requirements for the assignment, and do not support the theme/thesis. The work exhibits limited success in selecting supporting evidence. It struggles to meet the assignment specifications in either
- 18. quantity and/or quality and rarely supports the theme/thesis. The work uses a selection of supporting evidence that meets some expectations for the assignment in either quantity and/or quality. The work uses a selection of supporting evidence that is appropriate to the assignment in both quantity and quality.
- 19. The work uses a thoughtful selection of evidence that fully support the assignment in both quantity and quality. The work uses an excellent selection of evidence from quality sources that fully support all the parameters of the assignment in both quantity and quality. Possible Points 10 0 4 6 7 8 9 10 Writing Mechanics & Formatting: Grammar, spelling and syntax are
- 20. correct. Length meets requirements for the assignment. Sources & references are cited per specifications in the assignment. No submission. Significant number of errors in grammar, spelling and/or syntax per page. Does not adhere to length requirements. Does not use the required formatting style for citations and/or references. Errors in grammar, spelling and/or syntax
- 21. on most pages. Does not adhere to length requirements. Does not use the required formatting style for citations and/or references. Some errors in grammar, spelling and/or syntax; meets length requirements. Contains some errors in formatting style for all citations and/or references. No extensive errors in grammar,
- 22. spelling and/or syntax; meets length requirements. Uses the required formatting style correctly for most citations and references. Essentially, no significant errors in grammar, spelling or syntax throughout the entire document; meets length requirements. Uses the required formatting style for
- 23. all citations and references. No errors in grammar, spelling or syntax throughout the entire document; meets length requirements. Uses the required formatting style for all citations and provides accurate and complete references. Possible Points 10 0 4 6 7 8 9 10 Context and audience: The work is written in a way that is appropriate to the target audience, the purpose of the assignment, and addresses all
- 24. elements of the assignment with a tone that is appropriate to the assignment. No submission. The work lacks any focus on an audience and/or purpose; tone is inappropriate to the type of assignment. The work struggles to focus on an audience and/or purpose; primarily contains inappropriate tone. The work sporadically attempts to focus on an appropriate audience and/or
- 25. purpose; often contains inappropriate tone. The work remains focused on an appropriate audience and/or purpose most the time; usually contains appropriate tone. The work is focused on an appropriate audience and/or purpose; the tone is primarily appropriate to the assignment.
- 26. The work built around a strong focus on an audience and/or purpose; the tone is always appropriate. Criteria 0 (F) (F) (D) (C) (B) (A) (A+) COLUMN TOTALS 0 40 60 73 84 92 100 ENG 101 – Research Paper Rubric with Revision CHAPTER 10 ELECTRONIC COMMERCE SECURITY Summary Online businesses today must deal with a wide range of security risks. They often create a formal security policy document that identifies risks and countermeasures that will reduce those risks to an acceptable level. Online security elements include secrecy, integrity, and necessity.These three elements are each enforced in the three components of online business transactions, including client devices, the communication channel, and Web server computers. Client devices can be threatened by active content, viruses, or worms delivered throughWeb browsing activity (by means of cookies or Web bugs), e-mail, or other devices on the same network. Antivirus software is an important element in the protection of client computers. The main communication channel used in online business is the Internet, which is especially vulnerable to
- 27. attacks. Encryption provides secrecy and integrity protection against many of these attacks and can be implemented with private keys, public keys, or a combination of techniques. Digital certificates provide both integrity and user authentication, which can provide non-repudiation in online transactions. Secure Sockets Layer and Secure HTTP protocols can provide secure Web browser connections. Wireless networks are subject to threats of signal interception, but most wireless networks installed in businesses today (and many installed in homes) do use a secure form of wireless encryption.Web servers must be protected from both physical threats and Internet-based attacks on their software. Server protection methods include access control and authentication, which are provided by username and password login procedures and client certificates. Firewalls can be used to separate trusted inside networks and clients from untrusted outside networks, including other divisions of a company’s enterprise network system and the Internet.A number of organizations have been formed to share information about computer security threats and defenses. When large security outbreaks occur, the members of these organizations join together and discuss methods to locate and eliminate the threat. Computer forensics firms that undertake attacks against their clients computers can play an important role in helping to identify security weaknesses. CHAPTER 11 PAYMENT SYSTEMS FOR ELECTRONIC COMMERCE Summary Credit, debit, and charge cards (payment cards) are the most popular forms of payment on the Internet. Processing payment card transactions requires that an online merchant establish a merchant account with an acquiring bank. Merchants can obtain card approval and transaction settlement services using tools included in their electronic commerce software, through a separate payment processing software application, or from a payment process service provider.Digital cash, a form of online
- 28. payment that is portable and anonymous, has been slow to catch on in the United States. Digital cash could be useful for making micropayments because the cost of processing payment cards for small transactions is greater than the profit on such transactions. Digital wallets can store payment card information, digital cash, and personal consumer identification. Software-based digital wallets eliminate the need for consumers to reenter payment card and shipping information at each business’s Web site. Stored-value cards, including smart cards and magnetic stripe cards, are physical devices that hold information, including cash value, for the cardholder. Magnetic stripe cards have limited capacity. Smart cards can store greater amounts of data on a microchip embedded in the card and are intended to replace the collection of plastic cards people now carry, including payment cards, driver’s licenses, and insurance cards. Smart card use in the United States is not widespread; however, smart cards are popular in other parts of the world. Banks still process most monetary transactions, and a large part of the dollar volume of those transactions is still done by writing checks; however, banks often use Internet technologies to process those checks. Phishing expeditions and identity theft pose a significant threat to online financial institutions and their customers. Required Text Schneider, G. P. (2015). Electronic Commerce (11th ed.). Stamford, CT: Cengage Learning. Boston, MA. ISBN: 9781285742298 BUS615 Ecommerce
- 29. Computer security is the protection of assets from unauthorized access, use, alteration or destruction” (Schneider, 2015). Understanding the risks involved with computer security is essential. Figure 10-1 (Schneider, 2015), provides an illustration of the risks an impacts associated with computer security. Security for client computers requires the ability to protect the client “ . . . computer from threats that originate in software and data that are downloaded to the client computer from the Internet” (Schneider, 2015). Cookies are small files that identify returning visitors to particular web sites. The cookies contain private information about the client and the only means of protecting the client’s information completely is to disable the cookies. “The problem with this approach is that the useful cookies are blocked along with the others requiring visitors to enter information each time they visit the website” (Schneider, 2015). Chapter 10 Electronic Commerce Security Communication channel security entails security between communications layers. The Internet is not meant to be secure (Schneider, 2015) and therefore layers of security must be in place to keep Ecommerce transactions secure.
- 30. Threats to secrecy, integrity, necessity, physical communications and wireless communications require encryption as a means of keeping data and information secure. Encryption algorithms transform “ . . . plan text into cipher text (the unintelligible string of character) . . . “ (Schneider, 2015). The encrypted text provides for a mathematical pattern that is very difficult to transcribe and thus, renders the information secure. This form of security is essential for both physical and wireless networks. Chapter 10 Electronic Commerce Security Payment methods require the secure transfer of information. Payment cards make up the majority of online payment methods (Schneider, 2015, figure 11-1). Digital wallets provide means of holding credit card numbers or electronic cash (Schneider, 2015) and making the credit card number or electronic cash securely accessible for online purchases. Stored value cards include Magnetic strip and smart cards. Stored value cards provide a means of storing information related to financial accounts that can produce funds when funds are available. The difference between magnetic strip cards and smart cards is that the information in a smart card is stored in an encrypted microchip, as magnetic strip cards cannot be encrypted making smart cards more secure that magnetic strip
- 31. cards. Banking industries provide technologies for secure storage and transfer of funds and check processing functions. Increased activity from Mobile banking from smart phones and portable electronic devices are requiring banks to add services and security to support these activities. Banks also provide protection from identity theft. Chapter 11 Payment Systems for Ecommerce