Omer FarukARIK-CCNA-20-11-2021-certificate.pdf
•
0 likes•45 views
CCNA Certification
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
What's hot
What's hot (20)
Cybersecurity Tools | Popular Tools for Cybersecurity Threats | Cybersecurity...

Cybersecurity Tools | Popular Tools for Cybersecurity Threats | Cybersecurity...
Block Armour Zero Trust Solution for Hybrid and Distributed IT environments

Block Armour Zero Trust Solution for Hybrid and Distributed IT environments
Introduction to Android Application Security Testing - 2nd Sep 2017

Introduction to Android Application Security Testing - 2nd Sep 2017
The Ultimate Security Checklist Before Launching Your Android App

The Ultimate Security Checklist Before Launching Your Android App
CAPABILITIES STATEMENT KOUNTERACTIONS LLC_just ken and denise

CAPABILITIES STATEMENT KOUNTERACTIONS LLC_just ken and denise
Case Study on supply chain attack-how an rce in jenkins leads to data breache...

Case Study on supply chain attack-how an rce in jenkins leads to data breache...
Recently uploaded
Recently uploaded (20)
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
Easier, Faster, and More Powerful – Alles Neu macht der Mai -Wir durchleuchte...

Easier, Faster, and More Powerful – Alles Neu macht der Mai -Wir durchleuchte...
(Explainable) Data-Centric AI: what are you explaininhg, and to whom?

(Explainable) Data-Centric AI: what are you explaininhg, and to whom?
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...

Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...
How to Check CNIC Information Online with Pakdata cf

How to Check CNIC Information Online with Pakdata cf
Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots

Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots
Tales from a Passkey Provider Progress from Awareness to Implementation.pptx

Tales from a Passkey Provider Progress from Awareness to Implementation.pptx
Six Myths about Ontologies: The Basics of Formal Ontology

Six Myths about Ontologies: The Basics of Formal Ontology
Design and Development of a Provenance Capture Platform for Data Science

Design and Development of a Provenance Capture Platform for Data Science
AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)

AI+A11Y 11MAY2024 HYDERBAD GAAD 2024 - HelloA11Y (11 May 2024)
Introduction to FIDO Authentication and Passkeys.pptx

Introduction to FIDO Authentication and Passkeys.pptx
The Zero-ETL Approach: Enhancing Data Agility and Insight

The Zero-ETL Approach: Enhancing Data Agility and Insight
Omer FarukARIK-CCNA-20-11-2021-certificate.pdf
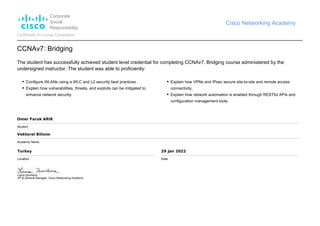
- 1. Corporate Social Responsibility Cisco Networking Academy Certificate of Course Completion CCNAv7: Bridging The student has successfully achieved student level credential for completing CCNAv7: Bridging course administered by the undersigned instructor. The student was able to proficiently: Configure WLANs using a WLC and L2 security best practices. Explain how vulnerabilities, threats, and exploits can be mitigated to enhance network security. Explain how VPNs and IPsec secure site-to-site and remote access connectivity. Explain how network automation is enabled through RESTful APIs and configuration management tools. Omer Faruk ARIK Student Vektorel Bilisim Academy Name Turkey Location 29 Jan 2022 Date Laura Quintana VP & General Manager, Cisco Networking Academy