Malware analysis and forensic analysis of images
•Download as DOCX, PDF•
1 like•851 views
Flowchart for Tier I and Tier II Malware Analysis
Report
Share
Report
Share
Recommended
Understand folder watching as part of a batch scanning environment. Use ImageRamp with or without Windows Services to automatically split, name, route, and index your scans and files. Folder Watching For Automated Document Capture, Batch Scanning

Folder Watching For Automated Document Capture, Batch ScanningDocuFi, offering HAI and Infection Prevention Analytics
Advanced malware analysis training session 7 malware memory forensicsAdvanced malware analysis training session 7 malware memory forensics

Advanced malware analysis training session 7 malware memory forensicsCysinfo Cyber Security Community
More Related Content
What's hot
What's hot (9)
Advanced malwareanalysis training session2 botnet analysis part1

Advanced malwareanalysis training session2 botnet analysis part1
Similar to Malware analysis and forensic analysis of images
Understand folder watching as part of a batch scanning environment. Use ImageRamp with or without Windows Services to automatically split, name, route, and index your scans and files. Folder Watching For Automated Document Capture, Batch Scanning

Folder Watching For Automated Document Capture, Batch ScanningDocuFi, offering HAI and Infection Prevention Analytics
Advanced malware analysis training session 7 malware memory forensicsAdvanced malware analysis training session 7 malware memory forensics

Advanced malware analysis training session 7 malware memory forensicsCysinfo Cyber Security Community
Similar to Malware analysis and forensic analysis of images (20)
Folder Watching For Automated Document Capture, Batch Scanning

Folder Watching For Automated Document Capture, Batch Scanning
[CONFidence 2016] Jacek Grymuza - From a life of SOC Analyst ![[CONFidence 2016] Jacek Grymuza - From a life of SOC Analyst](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[CONFidence 2016] Jacek Grymuza - From a life of SOC Analyst](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[CONFidence 2016] Jacek Grymuza - From a life of SOC Analyst
Advanced malware analysis training session 7 malware memory forensics

Advanced malware analysis training session 7 malware memory forensics
Cyber Defense Forensic Analyst - Real World Hands-on Examples

Cyber Defense Forensic Analyst - Real World Hands-on Examples
MacOS forensics and anti-forensics (DC Lviv 2019) presentation

MacOS forensics and anti-forensics (DC Lviv 2019) presentation
Recently uploaded
Saudi Arabia [ Abortion pills) Jeddah/riaydh/dammam/+966572737505☎️] cytotec tablets uses abortion pills 💊💊
How effective is the abortion pill? 💊💊 +966572737505) "Abortion pills in Jeddah" how to get cytotec tablets in Riyadh " Abortion pills in dammam*💊💊
The abortion pill is very effective. If you’re taking mifepristone and misoprostol, it depends on how far along the pregnancy is, and how many doses of medicine you take:💊💊 +966572737505) how to buy cytotec pills
At 8 weeks pregnant or less, it works about 94-98% of the time. +966572737505[ 💊💊💊
At 8-9 weeks pregnant, it works about 94-96% of the time. +966572737505)
At 9-10 weeks pregnant, it works about 91-93% of the time. +966572737505)💊💊
If you take an extra dose of misoprostol, it works about 99% of the time.
At 10-11 weeks pregnant, it works about 87% of the time. +966572737505)
If you take an extra dose of misoprostol, it works about 98% of the time.
In general, taking both mifepristone and+966572737505 misoprostol works a bit better than taking misoprostol only.
+966572737505
Taking misoprostol alone works to end the+966572737505 pregnancy about 85-95% of the time — depending on how far along the+966572737505 pregnancy is and how you take the medicine.
+966572737505
The abortion pill usually works, but if it doesn’t, you can take more medicine or have an in-clinic abortion.
+966572737505
When can I take the abortion pill?+966572737505
In general, you can have a medication abortion up to 77 days (11 weeks)+966572737505 after the first day of your last period. If it’s been 78 days or more since the first day of your last+966572737505 period, you can have an in-clinic abortion to end your pregnancy.+966572737505
Why do people choose the abortion pill?
Which kind of abortion you choose all depends on your personal+966572737505 preference and situation. With+966572737505 medication+966572737505 abortion, some people like that you don’t need to have a procedure in a doctor’s office. You can have your medication abortion on your own+966572737505 schedule, at home or in another comfortable place that you choose.+966572737505 You get to decide who you want to be with during your abortion, or you can go it alone. Because+966572737505 medication abortion is similar to a miscarriage, many people feel like it’s more “natural” and less invasive. And some+966572737505 people may not have an in-clinic abortion provider close by, so abortion pills are more available to+966572737505 them.
+966572737505
Your doctor, nurse, or health center staff can help you decide which kind of abortion is best for you.
+966572737505
More questions from patients:
Saudi Arabia+966572737505
CYTOTEC Misoprostol Tablets. Misoprostol is a medication that can prevent stomach ulcers if you also take NSAID medications. It reduces the amount of acid in your stomach, which protects your stomach lining. The brand name of this medication is Cytotec®.+966573737505)
Unwanted Kit is a combination of two mediciAbortion pills in Doha Qatar (+966572737505 ! Get Cytotec

Abortion pills in Doha Qatar (+966572737505 ! Get CytotecAbortion pills in Riyadh +966572737505 get cytotec
(NEHA) Call Girls Katra Call Now: 8617697112 Katra Escorts Booking Contact Details WhatsApp Chat: +91-8617697112 Katra Escort Service includes providing maximum physical satisfaction to their clients as well as engaging conversation that keeps your time enjoyable and entertaining. Plus, they look fabulously elegant, making an impression. Independent Escorts Katra understands the value of confidentiality and discretion; they will go the extra mile to meet your needs. Simply contact them via text messaging or through their online profiles; they'd be more than delighted to accommodate any request or arrange a romantic date or fun-filled night together. We provide: (NEHA) Call Girls Katra Call Now 8617697112 Katra Escorts 24x7

(NEHA) Call Girls Katra Call Now 8617697112 Katra Escorts 24x7Call Girls in Nagpur High Profile Call Girls
Ashok Vihar Call Girls in Delhi (–9953330565) Escort Service In Delhi NCR PROVIDE 100% REAL GIRLS ALL ARE GIRLS LOOKING MODELS AND RAM MODELS ALL GIRLS” INDIAN , RUSSIAN ,KASMARI ,PUNJABI HOT GIRLS AND MATURED HOUSE WIFE BOOKING ONLY DECENT GUYS AND GENTLEMAN NO FAKE PERSON FREE HOME SERVICE IN CALL FULL AC ROOM SERVICE IN SOUTH DELHI Ultimate Destination for finding a High Profile Independent Escorts in Delhi.Gurgaon.Noida..!.Like You Feel 100% Real Girl Friend Experience. We are High Class Delhi Escort Agency offering quality services with discretion. We only offer services to gentlemen people. We have lots of girls working with us like students, Russian, models, house wife, and much More We Provide Short Time and Full Night Service Call ☎☎+91–9953330565 ❤꧂ • In Call and Out Call Service in Delhi NCR • 3* 5* 7* Hotels Service in Delhi NCR • 24 Hours Available in Delhi NCR • Indian, Russian, Punjabi, Kashmiri Escorts • Real Models, College Girls, House Wife, Also Available • Short Time and Full Time Service Available • Hygienic Full AC Neat and Clean Rooms Avail. In Hotel 24 hours • Daily New Escorts Staff Available • Minimum to Maximum Range Available. Location;- Delhi, Gurgaon, NCR, Noida, and All Over in Delhi Hotel and Home Services HOTEL SERVICE AVAILABLE :-REDDISSON BLU,ITC WELCOM DWARKA,HOTEL-JW MERRIOTT,HOLIDAY INN MAHIPALPUR AIROCTY,CROWNE PLAZA OKHALA,EROSH NEHRU PLACE,SURYAA KALKAJI,CROWEN PLAZA ROHINI,SHERATON PAHARGANJ,THE AMBIENC,VIVANTA,SURAJKUND,ASHOKA CONTINENTAL , LEELA CHANKYAPURI,_ALL 3* 5* 7* STARTS HOTEL SERVICE BOOKING CALL Call WHATSAPP Call ☎+91–9953330565❤꧂ NIGHT SHORT TIME BOTH ARE AVAILABLE
Call Girls In Shalimar Bagh ( Delhi) 9953330565 Escorts Service

Call Girls In Shalimar Bagh ( Delhi) 9953330565 Escorts Service9953056974 Low Rate Call Girls In Saket, Delhi NCR
In the energy sector, the use of temporal data stands as a pivotal topic. At GRDF, we have developed several methods to effectively handle such data. This presentation will specifically delve into our approaches for anomaly detection and data imputation within time series, leveraging transformers and adversarial training techniques.Anomaly detection and data imputation within time series

Anomaly detection and data imputation within time seriesParis Women in Machine Learning and Data Science
Recently uploaded (20)
Junnasandra Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore...

Junnasandra Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore...
Digital Advertising Lecture for Advanced Digital & Social Media Strategy at U...

Digital Advertising Lecture for Advanced Digital & Social Media Strategy at U...
Al Barsha Escorts $#$ O565212860 $#$ Escort Service In Al Barsha

Al Barsha Escorts $#$ O565212860 $#$ Escort Service In Al Barsha
Abortion pills in Doha Qatar (+966572737505 ! Get Cytotec

Abortion pills in Doha Qatar (+966572737505 ! Get Cytotec
(NEHA) Call Girls Katra Call Now 8617697112 Katra Escorts 24x7

(NEHA) Call Girls Katra Call Now 8617697112 Katra Escorts 24x7
Call Girls In Shalimar Bagh ( Delhi) 9953330565 Escorts Service

Call Girls In Shalimar Bagh ( Delhi) 9953330565 Escorts Service
BDSM⚡Call Girls in Mandawali Delhi >༒8448380779 Escort Service

BDSM⚡Call Girls in Mandawali Delhi >༒8448380779 Escort Service
Anomaly detection and data imputation within time series

Anomaly detection and data imputation within time series
Call Girls In Bellandur ☎ 7737669865 🥵 Book Your One night Stand

Call Girls In Bellandur ☎ 7737669865 🥵 Book Your One night Stand
Chintamani Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore ...

Chintamani Call Girls: 🍓 7737669865 🍓 High Profile Model Escorts | Bangalore ...
Call Girls Bommasandra Just Call 👗 7737669865 👗 Top Class Call Girl Service B...

Call Girls Bommasandra Just Call 👗 7737669865 👗 Top Class Call Girl Service B...
Accredited-Transport-Cooperatives-Jan-2021-Web.pdf

Accredited-Transport-Cooperatives-Jan-2021-Web.pdf
Call Girls Begur Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore

Call Girls Begur Just Call 👗 7737669865 👗 Top Class Call Girl Service Bangalore
Call Girls in Sarai Kale Khan Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts S...

Call Girls in Sarai Kale Khan Delhi 💯 Call Us 🔝9205541914 🔝( Delhi) Escorts S...
Cheap Rate Call girls Sarita Vihar Delhi 9205541914 shot 1500 night

Cheap Rate Call girls Sarita Vihar Delhi 9205541914 shot 1500 night
Malware analysis and forensic analysis of images
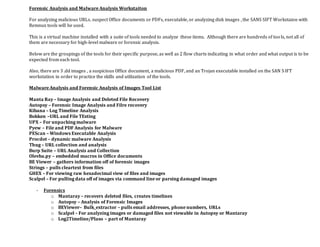
- 1. Forensic Analysis and Malware Analysis Workstaiton For analyzing malicious URLs. suspect Office documents or PDFs, executable, or analyzing disk images , the SANS SIFT Workstaion with Remnux tools will be used. This is a virtual machine installed with a suite of tools needed to analyze these items. Although there are hundreds of too ls, not all of them are necessary for high-level malware or forensic analysis. Below are the groupings of the tools for their specific purpose, as well as 2 flow charts indicating in what order and what output is to be expected from each tool. Also, there are 3 .dd images , a suspicious Office document, a malicious PDF, and an Trojan executable installed on the SAN SIFT workstation in order to practice the skills and utilization of the tools. Malware Analysis and Forensic Analysis of Images Tool List Manta Ray – Image Analysis and Deleted File Recovery Autopsy – Forensic Image Analysis and Filre recovery Kibana – Log Timeline Analysis Bokken –URL and File TEsting UPX – For unpacking malware Pyew – File and PDF Analysis for Malware PEScan – Windows Executable Analysis Procdot – dynamic malware Analysis Thug – URL collection and analysis Burp Suite – URL Analysis and Collection Olevba.py – embedded macros in Office documents BE Viewer – gathers information off of forensic images Strings – pulls cleartext from files GHEX – For viewing raw hexadecimal view of files and images Scalpel – For pulling data off of images via command line or parsing damaged images - Forensics o Mantaray – recovers deleted files, creates timelines o Autopsy – Analysis of Forensic Images o BEViewer– Bulk_extractor – pulls email addresses, phone numbers, URLs o Scalpel – For analyzing images or damaged files not viewable in Autopsy or Mantaray o Log2Timeline/Plaso – part of Mantaray
- 2. o GHEX - Malware analysis o Suspicious URL Thug.py www.yahoo.com - FZM ……output to var/log/thug Burpsuite JSDetox o Static Bokken - GUI Interface that can analyze the following: Websites Executables PDF Files PEScan – Scans executables and provides information PEFrame Pyew Commands o Pyew.imports – more details on malware o Urls – will show URLs inside a piece of malware o Packer – will show if the malware is “packed” o Threat – sends the MD5 has to Virustotal o Pdfview – only for using pyew to analyze PDF Files UPX Ghex o Document Analysis Olevba.py – for Office Document Macros JSDetox – For Obfuscated Java Script PDFxtract – For PDF Peepdf –I – PDF Document Analysis Pyew – PDF and Windows Executable Analysis Swfdump – to pull .swf files out of PDF files o Dynamic - Need a VM to infect - Need to tailor VM so that the malware does not detect this as a VM for analysis
- 3. Static Analysis of Suspicious URLs and Malware Flowchart Is this an executable, URL, Offfice Doc, or PDF? URL Use thug.py -FZM www.xxxxxx.com to pull the website and analyze Executable Use PEFrame and Pyew to Analyze Is it packed? Unpack using UPX or another tool Use" strings" to find Cleartext Use XORSearch or No MoreXOR to find hidden strings Office Document Use olevba.py to find suspicious macros PDF Use"pyew" to analyze Use "pdfview" option to view any suspicious Javascript May need to use JS-Detox to de-obfuscate Javascript
- 4. Forensic Analysis of Workstation Image Obtain Disk Image via ExternalMedia DVD or External USB Determine Format Determine Partion for Analysis mmls command FTK Image type from Forensic Toolkit Imager DD Autopsy GUI Interface, retrieves deleted files GHEX Raw Look at Files and Disk Images Scalpel Command-Line..for damaged or unmountable images Mantaray GUI Interface Supertimeline Pulls all logs and creates a timeline of activity Forefront Recovers deleted files and separates tehm into folders Bulk_Extractor BEViewer - extracts emails, URLs, telephone numberes...etc from images For mounting a .dd image, right-click and chooseDrive Mounter VMDK Virtual Machine Image