More Related Content
Similar to HPE-FireEye_Infographic_CrisisCommunication_Final
Similar to HPE-FireEye_Infographic_CrisisCommunication_Final (20)
HPE-FireEye_Infographic_CrisisCommunication_Final
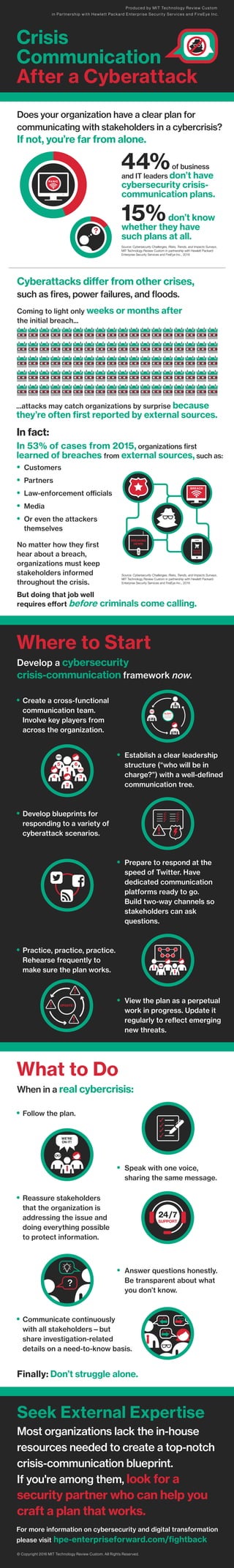
- 1. Seek External Expertise
Most organizations lack the in-house
resources needed to create a top-notch
crisis-communication blueprint.
If you're among them, look for a
security partner who can help you
craft a plan that works.
• Follow the plan.
• Speak with one voice,
sharing the same message.
• Reassure stakeholders
that the organization is
addressing the issue and
doing everything possible
to protect information.
• Answer questions honestly.
Be transparent about what
you don’t know.
• Communicate continuously
with all stakeholders—but
share investigation-related
details on a need-to-know basis.
Crisis
Communication
After a Cyberattack
Produced by MIT Technology Review Custom
in Partnership with Hewlett Packard Enterprise Security Services and FireEye Inc.
44%of business
and IT leaders don’t have
cybersecurity crisis-
communication plans.
15%don’t know
whether they have
such plans at all.
Source: Cybersecurity Challenges, Risks, Trends, and Impacts Surveys,
MIT Technology Review Custom in partnership with Hewlett Packard
Enterprise Security Services and FireEye Inc., 2016
Does your organization have a clear plan for
communicating with stakeholders in a cybercrisis?
If not, you’re far from alone.
• Create a cross-functional
communication team.
Involve key players from
across the organization.
• Establish a clear leadership
structure (“who will be in
charge?”) with a well-defined
communication tree.
• Develop blueprints for
responding to a variety of
cyberattack scenarios.
• Prepare to respond at the
speed of Twitter. Have
dedicated communication
platforms ready to go.
Build two-way channels so
stakeholders can ask
questions.
• Practice, practice, practice.
Rehearse frequently to
make sure the plan works.
• View the plan as a perpetual
work in progress. Update it
regularly to reflect emerging
new threats.
Where to Start
Cyberattacks differ from other crises,
such as fires, power failures, and floods.
Coming to light only weeks or months after
the initial breach...
...attacks may catch organizations by surprise because
they’re often first reported by external sources.
In fact:
In 53% of cases from 2015, organizations first
learned of breaches from external sources, such as:
• Customers
• Partners
• Law-enforcement officials
• Media
• Or even the attackers
themselves
No matter how they first
hear about a breach,
organizations must keep
stakeholders informed
throughout the crisis.
PANIC
Source: Cybersecurity Challenges, Risks, Trends, and Impacts Surveys,
MIT Technology Review Custom in partnership with Hewlett Packard
Enterprise Security Services and FireEye Inc., 2016
Finally: Don’t struggle alone.
UPDATE!
24/7
SUPPORT
WE’RE
ON IT!
What to Do
When in a real cybercrisis:
2
34
5 6
ALERT!
LEGAL
HR
IT
BREAKING
NEWS!
BREAKING
NEWS!
For more information on cybersecurity and digital transformation
please visit hpe-enterpriseforward.com/fightback
© Copyright 2016 MIT Technology Review Custom. All Rights Reserved.