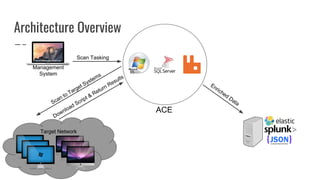
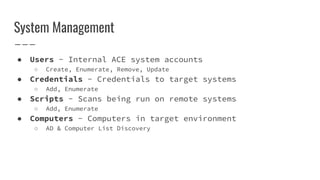
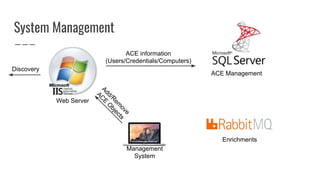
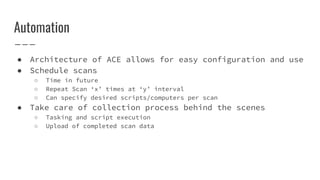
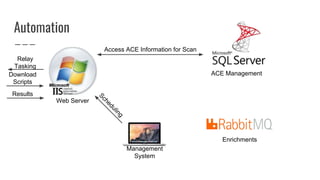
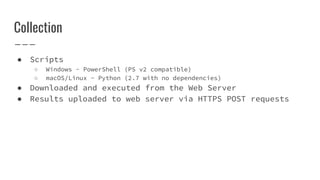
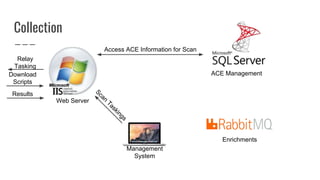
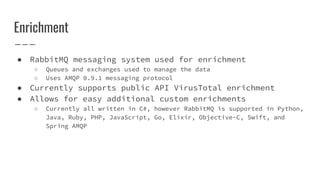
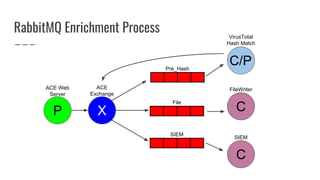
Automated Collection & Enrichment (ACE) is an open-source tool designed for agentless threat hunting across Windows and macOS/Linux systems, requiring only local admin access. It performs scans without writing data to disk, outputs results in JSON for easy integration with SIEMs, and is free to use. Future enhancements include simplified deployment, expanded scanning capabilities, and additional enrichment features.