The 10 most trusted erm solution providers 2019
- 4. E ith the new era of emerging technologies comes the wave of change and disruption. While businesses are focusing Won these technologies in order to transform their business, chances of risk and uncertainty are also growing along with them. Adopting new technologies in business processes could also bring some inevitable risks with them. New competitors, regulatory complexity, natural hazards, supply chain failure, mechanical breakdown, cyber-attacks are some risks that can occur without any prior notice. Unmanaged risks can create a huge impact on decisions related to investment, product development, sustainability, safety, etc. Thus, assessing such risks and responding them accordingly becomes mandatory as they can destroy sources of value creation for the business. This is where the need for an integrated approach, Enterprise Risk Management (ERM), generates. As business risks are continually increasing, corporations are finding it mandatory to implement some sort of risk management framework. An effective ERM program can not only help organizations to manage their risks and maximize opportunities, but also can streamline their business processes so as to achieve their organization’s goals. After the emergence of the fourth wave of industrial revolution, businesses have come through many repercussions. The changes comprising cost structures, outdated business platform and practices, market evolution, client perception, and pricing pressures occurred have implied a certain degree of unknown risks for many businesses. Though risks can have detrimental effects on businesses, they also act as an opportunity to instigate the change, as by taking a risk centric approach businesses can formulate a strategy for success. Hence, by incorporating an integrated approach, Enterprise Risk Management (ERM), businesses are achieving their goals and objectives, even when they encounter obstacles. Yet, many businesses are still finding it difficult to deal with changes driven by fourth Industrial Revolution. Framing a Sound Risk Management Approach
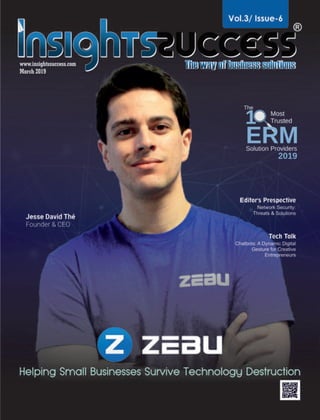
- 5. The present risk management practices are lacking suitability to interpret risks sooner. Hence, in order to enhance the ability to see and understand risky waves, many companies have developed new tools and techniques. By undertaking a new management discipline, these new tools and techniques are enabling businesses to easily predict and respond to the waves of disruption. Businesses are able to continuously monitor the changes in the environment to determine which could be truly disruptive. In order to portray the significance of an innovative approach and framework in identifying risks, Insights Success has enlisted “The 10 Most Trusted ERM Solution Providers, 2019”, which have built and are delivering agile and flexible risk management frameworks that enable businesses to anticipate and prepare for the shifts that bring long-term success. Our cover story features Zebu, a company based out of Waterloo, Ontario, known to be the second fastest growing startup community in the world. Zebu is creating a secure cloud-based platform for all business management needs. The company strives for businesses of all sizes to have the best management and productivity tools available to them, with security being the top priority. Also, make sure to scroll through the articles written by our editorial team and CXO standpoints of some of the leading industry experts to have a brief taste of the sector. Let’s start reading! Though risk is an uncertain phenomenon, it can be used to fuel innovation. “ “ Hitesh Dhamani
- 6. Helping Small Businesses Survive Technology Destruction 08 COVER STORY
- 7. CyberSaint Security: Bringing Automation and Visibility to Compliance and Risk Management Programs CoalFire: Empowering Organizations to Manage Risks Effectively CONTENTS What GDPR Forgets: The Physical Security Expert’s Thoughts Top 5 Email Security Threats Maestro’s Insights 32 22 18 30 Editor’s Pick Data Center Security: Controlling Possible Threats 16 Tech Talk Chatbots: A Dynamic Digital Gesture for Creative Entrepreneurs 36 Editor’s Prespective Network Security: Threats & Solutions 26 ARTICLES
- 9. sales@insightssuccess.com March, 2019 Editor-in-Chief Co-designerSenior Sales Manager Business Development Manager Marketing Manager Technical Head Technical Specialist Digital Marketing Manager Research Analyst Database Management Technology Consultant Pooja M. Bansal Managing Editor Anish Miller Executive Editor Kaustav Roy Assistant Editors Jenny Fernandes Hitesh Dhamani Visualizer David King Art & Design Director Amol Kamble Associate Designer Tejas Kulkarni Passi D. Peter Collins John Matthew Sales Executives David, Kevin, Mark, Manish Business Development Executives Steve, Joe, Alan, BinayJacob Smile Aditya Marry D’Souza SME-SMO Executive Prashant Chevale Patrick James Circulation Manager Robert Brown Stella Andrew David Stokes Asha Bange Co-designer Copyright © 2019 Insights Success, All rights reserved. The content and images used in this magazine should not be reproduced or transmitted in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, without prior permission from Insights Success. Reprint rights remain solely with Insights Success. Follow us on : www.facebook.com/insightssuccess/ www.twitter.com/insightssuccess We are also available on : Insights Success Media Tech LLC 555 Metro Place North, Suite 100, Dublin, OH 43017, United States Phone - (614)-602-1754 Email: info@insightssuccess.com For Subscription: www.insightssuccess.com Insights Success Media and Technology Pvt. Ltd. Off. No. 513 & 510, 5th Flr., Rainbow Plaza, Shivar Chowk, Pimple Saudagar, Pune, Maharashtra 411017 Phone - India: +91 7410079881/ 82/ 83/ 84/ 85 Email: info@insightssuccess.in For Subscription: www.insightssuccess.in
- 12. Running a business is a complicated task. There are numerous functions working at the same time and each and every function is interdependent. Which means, delay in one aspect of a business will directly affect the pace at which another aspect is functioning. With the weight of such activities already put on its shoulders, it becomes very difficult for an enterprise to manage day to day tasks. Small and medium businesses are especially affected by this, as they don’t have the resources to implement heavy software to manage everything. owners to spend less time managing their businesses, allowing them to get back to their passions. It offers a platform to help Small and Medium Enterprises (SMEs) manage their entire business, including an all-in- one solution for messaging, storage and scheduling - all of which are encrypted to protect their data. The services offered by Zebu make running the company easier so that owners can focus on what they do best while growing their business. The company believes that many small businesses are under siege from large, global businesses using To meet the requirements of small and medium enterprises, Zebu came forward with its comprehensive services, resolving all the issues with its all-in-one approach. With the vision to help create a world that’s full of vibrant, diverse and prosperous local businesses, Zebu, a start-up in Waterloo, Canada was created. It is focused on helping local businesses thrive by providing them with tools to improve team collaboration and productivity. Zebu exists to help small businesses succeed in their local communities. It builds tools that allow small business
- 13. advanced technology to gain efficiencies. These technologies are often too complicated or too expensive for local businesses to embrace. For this purpose, Zebu built an all-in-one productivity suite geared specifically to local businesses, aimed at helping them improve collaboration and productivity across their team, so that business owners can focus on what they do best. Visionary Child Prodigy Jesse David Thé is the Founder and CEO of Zebu. He came up with the idea behind Zebu while in high school. He spent some time looking into ways to help local businesses get equipped with modern technology so that they could better operate and thrive. He found a glaring gap in the solutions offered. The ERP solutions to help manage businesses were incredibly complex, hard to use, and cumbersome to set up. There were single solution apps that could help manage a single aspect of the business, but this approach of covering all their needs quickly became too overwhelming to manage when so many apps were required to manage the business. What these SMEs needed was an all-in-one solution that was as easy to use as the single solution apps. That’s where the idea for Zebu came along. Speaking about coming up with new ideas, Jesse believes that most of the owners of small or medium sized businesses spend the vast majority of their time just trying to make sure things are running. This takes away from the time they can spend coming up with new ideas to expand their business. He states, “If we can help reduce the amount of time owners need to spend managing everything, they can get back to focusing on growing their companies.” Products that Compliment Efficiency According to Zebu, many of the tools that local businesses use today are isolated from each other. Messaging is done at one place, while scheduling is done at another. This forces business owners to change the way they work in order to adapt to the technology. As an all-in-one platform, Zebu brings together the tools that local business
- 14. owners rely on to keep their business running smoothly. One great example is that its security and encryption just happen automatically in the background, without any specific actions required by the user. Encrypting a file like a customer order or financial spreadsheet is as simple as dragging and dropping it into Zebu. On that note Jesse asserts, “When it comes to your company’s communication, financials, intellectual property, human resources, and related activities, confidentiality is critical. Zebu gives them a transparent layer of security. Also, while most software companies that create business tools have built their business models around scanning and selling user information, Zebu uses encryption that means we have no way to read a customers’ messages or access their information.” Zebu offers various other services including Secure Team Messaging, allowing clients to have instant communication and long form discussions from anywhere in the world; Cloud Storage for the entire team, providing all members access to a secure cloud storage system allowing them to pull the files they need from anywhere in the world. Every team member has access to a personal calendar that can be shared with others, making it easy to plan around people’s schedules. They can also set events as private to ensure that sensitive meetings and event information is kept with only certain individuals. Comprehending Gradually Zebu’s initial tool was a dispatch and service request system to help local taxi companies compete with Uber, and also help other delivery companies manage their fleet. Its transport app had the flexibility to be
- 15. a taxi hailing app and an “object” delivery system. While creating this tool, and working with these companies, Zebu perceived that one of the biggest issues they had was a lack of proper communication and scheduling tools. Hence the company decided to add those features to the initial platform in order to help the companies communicate and schedule orders and rides. Once it became clear that the needs for these services was far greater and existing platforms could not deliver a compelling solution, Zebu shifted its focus entirely to those tools with the addition of cloud storage and file management. Zebu’s competition is composed of dozens of single, point-solution apps that only help with one thing. It integrates all business aspects into a single easy- to-use application, making single-function business apps irrelevant. Additional Functionality Zebu is continuously building up its Cloud platform that intelligently connects all aspects of business in a streamlined modular ERP system. Zebu provides small to medium sized enterprises across numerous goods and services industries access to the highest quality tools available to them. This enables them to thrive in the 21st century. Zebu has ambitious plans for the future of its platform. It will re-shape the way local businesses around the world operate. It started with communication, storage, and scheduling, but will soon add additional functionality to support businesses across all their needs. Cliental Assessment “We were looking for an application that would do a better job than just messaging. We had issues with the previous message app, where we had to manually take care of simple task requests in the message. For example, messages would request meeting dates, and we would have to exchange dozens of text messages to define common availability. Zebu just automatically creates polls. We would receive dozens of files, which were hard to find later when we really needed them. Zebu has a clever organization of files, where we always find them. We also love the fact that everything is encrypted to guarantee our intellectual properties are protected.” – Eduardo Pereira, President, Redesa. ZEBU Team
- 16. Address : Country :City : State : Zip : Global Subscription Date :Name : Telephone : Email : READ IT FIRST Never Miss an Issue Yes I would like to subscribe to Insights uccess Magazine., S SUBSCRIBE T O D A Y Che should be drawn in favor of:ck INSIGHTS SUCCESS MEDIA TECH LLC Insights Success Media Tech LLC 555 Metro Place North, Suite 100, Dublin, OH 43017, United States Phone (614)-602-1754,(302)-319-9947: Email: info@insightssuccess.com For Subscription: www.insightssuccess.com CORPORATE OFFICE
- 18. Data Center Security: The rise in cyber-crimes is one of the main causes of Data center outages. As per the recent survey conducted by industry insiders, cyber-crime caused 22 percent data center outages in 2015 opposed to 2 percent outages in 2010. Adding to all these, now most of the data centers are re-evaluating their security policies after the recent WannaCry ransomware attack. Data center outages cause companies to loss revenue in many ways. However, the costliest loss is service interruption and loss of IT productivity. So, the organizations are now realizing that traditional security is no longer secure enough to secure any data center. A recent study has found that 83 percent of traffic travels east/west within the data center, which stays undetected by the perimeter security. In this environment, when an attacker infiltrates the perimeter firewall, then can jump across the system with ease, extract information and compromise valuable data. Additionally, data centers can fail due to trespassers or a terrorist attack or by natural calamities. So, how can one secure a data center in the best way possible from any kind of cyber threat? Don’t worry we’ve got you covered, with the points below. As the first step, one should Map the Data Center and flag the hackers within the virtual and physical infrastructure. The CSOs and CIOs with a system map of their systems can react to any suspicious activity and take steps to stop data breaches. Being able to visualize different traffic patterns within a network helps to understand threats, that eventually elevates the level of security. Understanding and measurement of traffic flow within the data center boundary are very important. In the case of any interruption in traffic across east/west vs north/south, protected vs unprotected one can get to know about a threat. Additionally, vulnerable zones and unprotected traffic need to be monitored for a better result. Firewall rules need to be defined and implemented as per requirements. Additionally, one should allow traffic only after thorough verification and selectively allow communication to ensure maximum protection. The key is to identify, what is legal and secured and what can be blocked to enhance security. One needs to Build a Team with executives who understand how traffic flows within the premises and can access & secure information, take necessary measures to secure important assets along with the implementation of roadblocks for the attackers. Security must move as fast as a data center’s technology adoption and integration. Security Strategy Should Change Alongside the Technology and it should not be treated as an add-on option. Additionally, businesses also should ensure that their virus protection, signatures other protection features are up to date for better protection. Businesses should Identify and Place Controls over high- value assets, which will help to reduce risk. However, older security solutions are completely blind to new threats, new security companies have produced latest solutions that protect data in the virtual world. Access Restriction also needs to be imposed. Every business should thoroughly check a person’s background before giving the access to a prized possession. Access to the main site and the loading bay must be limited, Controlling Possible Threats March 2019|16 Editor’s Pick
- 19. additionally, two-factor authentications and fortified interiors with security guards and roving patrols would help to safeguard the employees and the data center. Installing Surveillance Cameras around the data center, alongside removing signs which may provide clues to its function helps to locate an intruder. A buffer zone between the data center and all the entry points will limit unlawful trespassing to a great extent. Additionally, the data center needs to be far away from the main road and it should not have any windows other than administrative purposes for better security. A data center should Check Test Back-Up Systems regularly as prescribed by the manufacturer. It should also ensure to make a list and of Do’s and Don’ts in the event of an attack. Recovery plans and security plans also need to be checked thoroughly. Data centers are always a Soft Target for The Terrorists, as an attack on them can disrupt and damage major business and communication infrastructure. So, security needs to be taken seriously and to do that proactive steps should be taken to limit the impact of a terrorist attack. Trained Security Guards needs to be posted inside a data center and they should be well trained. Security officers must undergo strict site-specific training to monitor surveillance footage. Depending on the size of data center and the number of security cameras multiple security officers may be required on duty. Security officers dedicated to inspecting surveillance footage helps when it comes to securing a data center. Disaster Recovery is very much important, that must be in place. If the data center stops functioning after an attack or natural calamity, it must have a way to restore operations as soon as possible. To be ready for a disaster and to evaluate the disaster recovery plan, it’s necessary to train staffs well and experience simulated disasters. To avoid these obstacles, one needs a fair bit of knowledge of new security systems, solid plans, and comprehensive visibility. The more work a data center can do up front in the above-mentioned areas the better the chances of success with lesser outages. 17|March 2019
- 20. Empowering Organizations to Manage Risks Effectively With increased usage of the World Wide Web, security breaches are becoming a more common occurrence nowadays. The past couple of years have witnessed detrimental security breaches to the common public, multinational organizations and small companies alike. Enter the Colorado-based cybersecurity advisory firm Coalfire, which helps private and public-sector organizations avert threats, close gaps and effectively manage risk. The organization helps its clients develop scalable programs that improve their security posture, achieve their business objectives and fuel their continued success by providing independent and tailored advice, assessments, technical testing and cyber engineering services. It’s All about Quality Coalfire employs a process-driven quality management system that ensures effective and repeatable project, staffing and contract management activities based on Capability Maturity Model Integration, Project Management Body of Knowledge, and ISO standards as well as industry best practices. Through an emphasis on efficiency and quality, Coalfire strives to improve its clients’ experience, refine project metrics and deliver unparalleled results. The company prefers to keep its focus on a consistent approach to delivery and continually improve all Coalfire services through evaluation, internal audit and internal corrective and preventive measures. Identifying Risks Coalfire advocates for creating a risk register where each risk is described, its severity is determined, ownership for risk mitigation is defined and risk mitigation tactics are clearly articulated. This risk register should be updated at least monthly, including progress reports on all existing risks along with any new risks that must be considered. A risk committee should then review the register monthly to track status on the existing and newly identified risks. According to Coalfire, the primary categories of risk organizations should consider include: Ÿ Strategic: Does a risk pose a threat to the success of key strategic initiatives? Ÿ Financial: The unplanned costs or reduction of revenue a risk could present if realized Ÿ Operational: Does a risk pose a threat to how work gets done? Ÿ People: Aging workforce, talent gap for needed skills, health and safety, risk culture not well established Ÿ Reputation: Will the organization suffer damage to its credibility with the public or other stakeholders; will it impact customer loyalty/retention? Ÿ Technology: Exposes key infrastructure/data to theft/loss, cyber threats, impact of use of new technology such as cloud, AI/machine learning, big data analytics Ÿ Legal: Risk triggers litigation, contractual risks Ÿ Regulatory/Compliance/Privacy: Failure to comply can result in large fines. Examples include HIPAA, PCI, GDPR and the new California Consumer Privacy Act Ÿ Regulatory overreach: Too much (overlapping/competing) regulation leads to confusion, overspending and lack of ability to keep up and comply. A Leader with the Mission of Reducing Enterprise Security Risk Tom McAndrew, the CEO of Coalfire, has over 15 years of leadership experience in information security The 10Most Trusted Solution Providers 2019 ERM March 2019|18
- 21. “Coalfire not only helps you understand risk, but also empowers you to manage it effectively.” strategies, assessment and audit for both commercial and federal sectors. He joined the organization in 2006, and since then has held key leadership roles spanning Sales, Service Delivery and Technical Testing. Before joining Coalfire, Tom designed information security and weapons systems for Space and Naval Warfare Command, Naval Sea Systems Command and the U.S. Navy. He brings all this expertise to his leadership position, overseeing, in a hands-on manner, how the company helps enterprises identify and manage risks. Coalfire’s mission is exclusively focused on enterprise risk reduction and management; Tom and the entire leadership team are focused on directing the organization toward helping customers achieve these aims efficiently and effectively. He is a highly visible thought leader, presenting frequently in private and public-sector speaking forums and contributing articles and commentary in the media, including the Wall Street Journal, Washington Post, Infosecurity Magazine and many others. Monitoring Cyber Risks During its initial days, Coalfire’s business was formed to help organizations comply with emerging data security regulations, such as those imposed in the heathcare and financial services sectors. Although compliance to the ever-expanding list of data privacy regulations remains vital to Coalfire and its esteemed clients, the industry now recognizes that “compliance does not equal security,” and Coalfire’s services have thus evolved to meet this recognition. As a result, the organization has expanded from a compliance firm to one that offers a full suite of cybersecurity services designed to help its clients identify, mitigate, and respond to cyber risks. Coalfire believes that rapidly changing technologies, such as the cloud, combined with the ever-evolving cyber threat landscape requires organizations to view cyber risks as a critical business issue and not just a concern related to IT. As technologies and threats continue to change, Coalfire sees a continuous need to monitor cyber risks, leveraging tools and key business partners where practical, in lieu of just adding cybersecurity professionals, who are increasingly in short supply. Developing a Culture of Security Coalfire believes adequately identifying and prioritizing risks should begin with the development of a governance structure, which should be a risk committee and needs to be chaired by CISO or equivalent. According to the company, it is important to develop a culture of security where employees are all encouraged to report issues they see that pose potential risk to the organization without any fear of reprisal, but rather with the blessing and encouragement of senior leadership. The support of the board and/or executive management is critical; they need to clearly articulate the importance of security and reporting risks throughout the organization. 19|March 2019
- 25. The Physical Security Gisle M. Eckhoff joined DigiPlex in August 2014 as Chief Executive Officer. He brings nearly thirty years’ experience in senior positions in the IT industry in the US, Sweden, UK and Denmark as well as at home in Norway. Gisle is the former Senior Vice President and Managing Director of CGI’s operation in Norway, and has also held a number of senior management roles at both country and regional levels in CSC Computer Sciences Corporation. The experience and knowledge gained from heading up the Financial Services vertical in the Nordic region, before becoming Vice President and Managing Director of CSC in both Norway and Sweden, is of great value when implementing DigiPlex’ growth strategy in the Nordic markets. he EU’s GDPR legislature will have consequences for every company doing business in TEurope, including American companies. The new directive promises sizeable fines to anyone that does not take personal data seriously. Meanwhile, the data centre company DigiPlex urges companies to focus on another important aspect: physical security. The General Data Protection Regulation’s (GDPR) purpose is to harmonize legislation related to personal information across the EU’s member states. It does however also create radical challenges for American businesses holding information on EU customers. Come May 2018, when the legislation enters into force, companies will have publicly disclosed how the data is used, in addition to offering transparency for individuals seeking access to their data. The GDPR includes a sanction mechanism, and the fines for non-compliance can reach 4 percent of a company’s annual revenue. • Business will obviously change for everyone not taking personal information seriously. This will clearly raise awareness regarding how the data is secured, but it’s also vital not to forget where the information is located, says DigiPlex CEO, Gisle M. Eckhoff. About the Author 23|March 2019
- 26. Moving data to safety American computer security company, McAfee, published a study of over 800 company leaders from different sectors. The report reveals that 50 percent of the respondents state that they would like to move their data to a more secure location. A motivating factor is the new EU legislation. The report also reveals that 74 percent of the business leaders specified that they thought protecting the data correctly would attract new customers. • Data security is not just about protecting yourself against hacking and other digital threats. The overall security critically depends on where your data is stored. Companies who actively select a secure data centre to host their data will gain a competitive advantage in the market as the management of personal information is in the spotlight, says Eckhoff. Physical security is forgotten While EU-based companies are in the process of adapting to the GDPR, Gartner predicted only 50 percent of American firms will be ready for the strict regulation by the end of 2018. It’s primarily the largest companies and public enterprises that are furthest along in the process of adaptation. According to Eckhoff, they are usually the ones that are the most concerned with data security and where it is stored. Fire and operational safety are two obvious challenges, but physical security also includes securing yourself against theft. • Several smaller businesses and organizations keep their data servers at their o ces, and the physical security in many of the smaller data centers is almost absent. If your data is stored in such a data center, where someone easily could break in and physically remove the hardware containing your information, then you are very vulnerable – both operationally and in relation to GDPR, says Eckho . At DigiPlex’s data centers, several layers of security ensure the safety of the data and the personal information that is stored there. Physical security is one of the most complicated and expensive features when building or updating a data center. That is why newly established data centers have to reach critical mass, allowing them to store enough data to compensate for the large security investment. Adapting to GDPR One consideration to take, as we are getting closer to the implementation date of GDPR, is where your data center should be located. Several US based companies are already relocating their centers to the EU in order to comply. Multiple database providers are helping non-EU companies organize and segregate EU data from other personal information. The data center industry is well established in Europe, and some of the most cost and climate efficient centers are located in the Nordic countries. In the Nordics, the cool climate helps chill down vast amounts of hardware that otherwise would have been cooled down solely by electricity. Additionally, the electricity that is required by data centers to run their operations is supplied through easy access to affordable renewable energy. • In recent years, we have seen political turbulence in larger parts of the world, Europe included. The stabile political environment in the Nordic countries is also a climate to consider, as the establishment of data centers is a long-term investment, says Eckhoff. March 2019|24
- 28. ovember 3, 1988, is considered as a turning point Nin the world of Internet. 25 Years ago a Cornell University graduate student created first computer worm on the Internet, “Morris Worm.” The Morris worm was not a destructive worm, but it permanently changed the culture of the Internet. Before Morris unleashed his worm, the Internet was like a small town where people thought little of leaving their doors unlocked. Internet security was seen as a mostly theoretical problem, and software vendors treated security flaws as a low priority. Today, there is a paradigm shift, Morris worm was motivated more by intellectual curiosity than malice, but it is not the case today. According to a 2015 Report, 71% of represented organizations experienced, at least, one successful cyber attack in the preceding 12 months (up from 62% the year prior). According to survey report, discloses that, among 5500 companies in 26 countries around the world, 90% of businesses admitted a security incident. Additionally, 46% of the firms lost sensitive data due to an internal or external security threat. On average enterprises pay US$551,000 to recover from a security breach. Small and Medium business spend 38K. Incidents involving the security failure of a third-party contractor, fraud by employees, cyber espionage, and network intrusion appear to be the most damaging for large enterprises, with average total losses significantly above other types of the security incident. Let’s Take a Look at Recurrent Security Threats Types- Denial of Service Attacks A denial of service (DoS) attack is an incident in which a user or organization is deprived of the services of a resource they would normally expect to have. These attacks are very common, accounting for more than one-third of all network attacks reviewed in the report. A standard approach is to overload the resource with illegitimate requests for service. Brute Force Attacks Brute force attack tries to kick down the front door. It’s a trial-and-error attempt to guess a system’s password. The Brute Force Attack password cracker software simply uses all possible combinations to figure out passwords for a computer or a network server. It is simple and does not employ any inventive techniques. Identity Spoofing IP spoofing, also known as IP address forgery. The hijacker obtains the IP address of a legitimate host and alters packet headers so that the regular host appears to be the source. An attacker might also use special programs to construct IP packets that seem to originate from valid addresses inside the corporate intranet. Browser Attacks Browser-based attacks target end users who are browsing Threats NETWORK SECURITY Threats & SolutionsSolutions Editor’s Prespectives March 2019|26
- 29. the internet which in turn can spread in the whole enterprise network. The attacks may encourage them to unwittingly download malware disguised as a fake software update or application. Malicious and compromised websites can also force malware onto visitors’ systems. SSL/TLS Attacks Transport layer security (TLS) ensures the integrity of data transmitted between two parties (server and client) and also provides strong authentication for both sides. SSL/TLS attacks aim to intercept data that is sent over an encrypted connection. A successful attack enables access to the unencrypted information. Secure Sockets Layer (SSL) attacks were more widespread in late 2014, but they remain prominent today, accounting for 6% of all network attacks analyzed. Network Security is an essential element in any organization’s network infrastructure. Companies are boosting their investments in proactive control and threat intelligence services, along with better wireless security, next-generation firewalls and increasingly advanced malware detection. The U.S. Federal Government has spent $100 billion on cyber security over the past decade, $14 billion budgeted for 2016. Increased use of technology helps enterprises to maintain the competitive edge, most businesses are required to employ IT security personnel full-time to ensure networks are shielded from the rapidly growing industry of cyber crime. Following are the methods used by security specialists to full proof enterprise network system- Penetration Testing Penetration testing is a form of hacking which network security professionals use as a tool to test a network for any vulnerabilities. During penetration testing IT professionals use the same methods that hackers use to exploit a network to identify network security breaches. Intrusion Detection Intrusion detection systems are capable of identifying suspicious activities or acts of unauthorized access over an enterprise network. The examination includes a malware scan, review of general network activity, system vulnerability check, illegal program check, file settings monitoring, and any other activities that are out of the ordinary. Network Access Control Network Access Controls are delivered using different methods to control network access by the end user. NACs offer a defined security policy which is supported by a network access server that provides the necessary access authentication and authorization. Network Security is a race against threats, and many organizations are a part of this race to help enterprises to 27|March 2019
- 30. secure their network systems. Organizations like IBM, Symantec, Microsoft have created solutions to counter the global problem of network security threat. These cutting-edge products show genuine promise and are already being used by enlightened companies. Good Network Security Solutions Traits A real security solution should have four major characteristics; Detect Threats Targeted attacks are multi-faceted and specially designed to evade many point technologies attempting to identify and block them. Once they are inside, the only way to find these cyber threats is to understand the behavior of the individual attack components and use analytics to understand their relationships. Respond Continuously Today it is not important that an organization will be attacked, but important and more crucial is to identify when and how much they can limit the impact and contain their exposure. This means having the capability to respond quickly once the initial incident has been discovered. Prevent Attacks Malware is gettings quick-witted day by day. They utilize heuristics to change their code dynamically. A capable solution should have an adaptive architecture that evolves with the changing environment, and threats today’s business faces. Integration Today’s threats have multiple facets, and a single software or solution is not sufficient. Protection system should have the capability to integrate with other security tools from different vendors to work together as a single protection system, acting as connective tissue for today’s disjointed cyber security infrastructure. Solutions In Market Like infectious diseases, cyber threats will never be eradicated entirely, but they can be better contained and understood, and their effects minimized. How can this be achieved? IBM has built an enterprise-level “immune system,” an adaptive security architecture to battle today’s cyber pathogens. IBM has developed a vast fleet of products, QRadar, X-Force Threat Intelligence, Trusteer Pinpoint Malware Detection, IBM Threat Protection System a dynamic, integrated system to meddle the lifecycle of advanced attacks and prevent loss. The IBM Threat Protection System integrates with 450 security tools from over 100 vendors acting as connective tissue for today’s disjointed cyber security infrastructure. Symantec is another major player in catering enterprise network security systems with Symantec Advanced Threat Protection. Symantec ATP operates via a single console and works across endpoints, networks, and emails, integrating with Symantec Endpoint Protection (SEP), and Symantec Email Security cloud, which means organizations do not need to deploy any new endpoint agents. Symantec says, ATP is the only threat protection appliance that can work with all three sensors without requiring additional endpoint agents. With ATP, Symantec’s goal is to deliver end-to-end threat protection, prevention, detection, and response in a single pane of glass, offering more value to businesses than individual point products can provide. Symantec Advanced Threat Protection combines multiple layers of prevention, detection, and response. March 2019|28
- 32. Bringing Automation and Visibility to Compliance and Risk Management Programs The complexities that come with today’s increased digitization are ever-apparent, and the risk of cyber- attacks is growing exponentially. Recognizing this, Boston based CyberSaint Security, a leading cybersecurity software firm, helps organizations manage cybersecurity risks through its flagship CyberStrong integrated risk management (IRM) platform. The platform was built by a team whose intellectual DNA winds deeply through the academic, tech and investment communities in Boston, the White House, RSA, IBM, EMC, KPMG, MIT, Harvard and others. CyberSaint’s mission is to empower organizations to manage cybersecurity as a business function through the adoption of powerful technology that enables measurement, enhances communication and improves cybersecurity resiliency. The CyberStrong Platform is an integrated risk management solution powering automated, intelligent cybersecurity compliance and risk management. Built on the gold-standard foundation of the NIST Cybersecurity Framework, CyberStrong’s capabilities streamline GRC activities and provide a single pane of glass through which CISOs and their security teams can measure, report, and mitigate risk. CyberStrong’s unparalleled time-to-value, breakthrough Artificial Intelligence and Machine Learning automation eliminate manual effort and help organizations make informed decisions that reduce risk while driving overall business value. Fortune 500 CSO turned CEO George Wrenn is the Founder and CEO of CyberSaint Security, exhibiting over 20+ years of comprehensive experience. Prior to his current role, he was the CSO and VP of Cybersecurity for Schneider Electric, a Fortune 500 global power company. Prior, George was a senior managing consultant with IBM, helping cross-industry Fortune 1000 customers reach compliance to NIST, FISMA, ISO/IEC, HIPAA, PCI, NERC/CIP, and other key regulatory frameworks, developing cyber security strategy, roadmaps, and global cyber security programs. Till date, he has collaborated, reviewed, and added value in the development of frameworks and standards such as the NIST Cybersecurity Framework and others. George is a graduate from Harvard University and has attended executive programs at Harvard Business School and the Harvard Kennedy School. As a Graduate Fellow at MIT for over a decade, he conducts research and advanced coursework at the MIT Media Lab, the Sloan School of Management, the School of Engineering, the School of Architecture and most recently the MIT Security Studies program working on Cyber Warfare frameworks. He is also an Affiliate and Researcher at MIT’s Executive Development program specializing in the NIST Cybersecurity Framework. George is a seasoned keynote speaker, and has spoken at the inaugural NIST Cybersecurity Risk Management Conference on IoT Security and Digital Risk Management. He has also had an NSA sponsored ISSEP credential, a Certified Ethical Hacker and CISSP for more than 12 years. George has experience working with the complex Cloud, Government, IT, ICS, audit and national regulatory frameworks. He was also a mission oriented Operations Officer and SAR/DR Pilot (Officer 1st Lt. USAF/Aux) where he served as 1st lieutenant, and has received a National Commander’s Commendation Award for outstanding duty performance with the Hanscom Composite Squadron (HCS-MA-043) based at Hanscom Air Force Base. Automating GRC to Fuel an Integrated Approach The CyberStrong platform automates the manual assessment processes that deter organizations from rapid adoption of gold standards such as the NIST CSF. The platform supports ISO27001/2, GDPR, COBIT, IEC62443, The 10Most Trusted Solution Providers 2019 ERM March 2019|30
- 33. and any other framework- including custom controls and hybrid frameworks. CyberStrong’s proprietary control optimization uses patented machine learning and artificial intelligence for faster risk management decision making and automated risk mitigation action planning. CyberStrong ingests its client’s assessment data to provide risk quantification and analytics that identify their current gaps, and maps this data across people, process, technology, risk, and cost to provide an optimization that identifies low- hanging-fruit opportunities to mitigate risk for the lowest cost and highest impact on their posture. This patented optimization encourages ‘always-on’ continuous improvement, and is completely automated in real-time, requiring zero manual effort to produce fully customized mitigation plans. In addition, CyberStrong’s integrated threat feed automates the prioritization of controls for remediation based on real-time detection of threats that appear active at any time, for any assessment. CyberSaint believes that by 2020, 100% of large enterprises will be asked to report to their Board of Directors on cybersecurity and technology risk at least annually, which is an increase from today’s 40%. According to Gartner, as enterprise stakeholders take an increasing interest and concern about the security posture, the CISO needs to be able to convey their activities and success as effectively as a CFO can with a balance sheet and statement of cash flows. This approach will ensure that all leaders, in every department regardless of security expertise, can understand the enterprise’s risk posture, what affects it, and what to be aware of. There are four recommended reports necessary to help you align your activities as a CISO with the goals and objectives of the enterprise: Executive Risk Report, Trend Report, GDPR Report, and Global Report - all which are automated from within the CyberStrong interface with no human effort required. CyberStrong allows CISOs to effectively communicate their strategies in a way that is universally understood. Client Feedback “CyberStrong provides me with a means to effectively measure and communicate our overall compliance posture, AI to model my security investments for the best ROI, and information on risk exposure using an industry standard model paired with innovative technology. Bright Horizons management can now evaluate clear gaps and work with my team to manage risk across the enterprise.” Javed Ikbal, CISO and VP of Information Security, Risk Management & Compliance at Bright Horizons Family Solutions (NYSE: BFAM) “CyberStrong provides an easy-to-use platform for us to maintain our compliance with the new DoD DFARS regulation. The team from CyberSaint got us up and running very quickly and now we manage our DoD compliance on our own.” Anthony Santagati, CFO at Senior (Senior Plc- LSE: SNR) Aerospace Metal Bellows. “The CyberStrong Platform's breakthrough technology augments and enhances every element of your cybersecurity program strategy, posture and potential.” 31|March 2019
- 34. Top 5EmailSecurity Threats Nearly 95 percent of all successful attacks on enterprise networks targeted organization’s users through email. With the industry of cybersecurity evolving so rapidly, hackers are consistently changing their tactics, keeping it almost impossible to keep up with. With today’s growing security landscape, email threats are one of the most common strategies utilized by cyber criminals. What started off with spam emails sent to your junk folder, has evolved to a more robust tactic to deliver destructive content straight to your inbox. Here are the top five email security threats that we’ve seen so far this year: Emotet Banking Trojan Emotet is an advanced, modular banking Trojan that primarily focuses as a downloader or dropper of other banking Trojans and continues to be among the most costly and destructive malware affecting governments, private and public sectors. Emotet can evade most signature-based detections, and because it is Virtual Machine aware, it generates false indicators when ran in a sandbox. Additionally, Emotet has several methods for maintaining persistence, including auto-start registry keys and services as well as Dynamic Link Libraries to continuously update and evolve its capabilities. Initial infection of this malware occurs when a user opens or clicks a malicious download link, PDF, or macro-enabled Microsoft Word document included in the malspam. Once downloaded, Emotet establishes persistence and attempts to propagate local networks through one of its incorporated spreader modules. The negative consequences from an Emotet infection can be temporary or permanent loss of sensitive proprietary information, disruption of regular operations, financial losses incurred to restore systems and files, and potential harm to an organizations reputation. Ursnif Banking Malware A new version of the infamous banking Trojan Ursnif made its appearance again earlier this year in June. This malware is well known in the cyber security community and was the most active malware code in the financial sector from the end of 2016 into early 2017. This malware is capable of stealing users’ credentials, credentials for local webmail, cloud storage, cryptocurrency exchange platforms and e-commerce sites. Once Ursnif infects a new machine it will attempt to spread to other users in the address book of the compromised email accounts. It tricks the victim into opening the malicious email because the message is presented as the reply to an existing conversation conducted by the victim in the past. For example, if you receive an email that was a replay to a previous conversation from a while back, you can look at the “To:” field in the email and see if it’s replied to a large number of unsuspecting users. Another feature about this malware is its ability to keep track of company names and title the malicious document “VICTIM_COMPANY_.doc” in order to look legitimate. Once the victim clicks enable macros, the second step of the infection process begins, which launches a malicious March 2019|32 Maestro’s Insights
- 35. ABOUT THE AUTHOR Shawn Pope is the Cyber Security Engineer of Nuspire Networks, a state-of-the-science managed network security provider for some of the largest and most distinctive companies around the world. script that downloads and executes a payload from a server controlled by the attackers. Once installed, Ursnif can operate without being noticed by both the user and the operating system. Extortion Campaign Extortion campaigns have been around for quite some time but there was one that was in full swing across the globe that used a clever twist to trick unsuspecting users into paying a ransom. The attacker for this extortion campaign claims to have installed malware on your system and has also used your webcam to record you watching porn. The attacker then goes on to threaten the release of this video to everyone in your contacts unless you pay the Bitcoin ransom. The basic premise of this type of extortion attempt has been around for quite some time, but the addition of the Username/Password combination in the subject line has unsuspecting users worried. While researching this campaign, Nuspire’s Security Analytics Team (SAT) came across multiple different counts of affected users claiming the Username/Password combination was something they had used eight years ago. In this case, the attacker has somewhat automated the attack to create a script that pulls directly from usernames and passwords of a given data breach that happened eight years ago. Therefore, every victim who had their password compromised as part of that breach, is now getting this same email at the address they used to sign up for the hacked website. Hopefully, if you were affected by that data breach you updated your username/password combination. Granted, the people who didn’t bother changing this information, this attack directly affects them, but rest assured this attacker doesn’t have a recording of you that they plan to send out to your contacts. It is merely scare tactics to make some easy money, and upon investigation of multiple Bitcoin addresses associated with this campaign, the attacker was indeed making easy money. This attack could evolve in the future and use more up to date data breaches which in turn could scare more users into paying the ransom, so be on the lookout. GandCrab Ransomware GandCrab holds the top spot in ransomware, partly because it’s used by the Magnitude botnet. Although GandCrab is usually spread via spam email, it has recently been distributed via compromised websites and is now Shawn Pope Cyber Security Engineer 33|March 2019
- 36. appending the .KRAB extension to the encrypted files. Towards the end of April 2018 a campaign with the subject line “Your Order #{Random Digits}” was circulating. There is limited content in the body of the email and has an attached ZIP file which includes a Word document that contains malicious macros that download and execute GandCrab ransomware. GandCrab is under constant development where new versions are consistently being released at an aggressive pace. Its basic functionality is well document and does the same typical things ransomware does, including encrypting files with the. KRAB extension, changing the user’s background, and leveraging Tor for communications. One of the interesting elements of Gandcrab is its use of namecoin domains for Command and Control (C2) communication. These are easily identified by the .bit top level domain (TLD). Since attackers rely heavily on Tor and namecoin domains to help evade identification, it is a no brainer for them to use a decentralized DNS service that does not rely on central authority. This also increases the difficulty of having domains shut down and identifying those that are potentially behind them. Phishing By the end of Q2 2018 Microsoft had taken over the top spot from Facebook for the number one target of corporate phishing attacks. Reason being, it’s highly profitable for hackers to compromise an Office 365 account. Hackers see email-based attacks as an easy entry point into data, files, and contacts from other Office 365 apps, including SharePoint, OneDrive, Skype, Excel, and CRM. We see all different types of Phishing attempts from quite possibly the worst attempts to exact replicas of a legitimate Office 365 login page. Unfortunately, Phishing will always exist and can slip through the gaps in email filtering due to the fact that new domains/URLs are popping up every day to host fake login pages. This is where user awareness training is extremely important. Educate your users, roll out training exercises where employees with fake Phishing emails and see who clicks on them and who doesn’t. Because Phishing has become so popular, education will pay off in the long run. Solutions Aside from training and educating employees on malware, and ransomware that might come in through a user’s email, there are a few other solutions to take into consideration that can prevent these attacks from entering your network. 1. Use antivirus programs with behavior and heuristic detection capabilities, with automatic updates of signatures and software on clients and servers. 2. Implement a spam filter to filter out known malspam indicators such as malicious subject lines, and block suspicious and blacklisted Ips. 3. Mark external emails with a banner denoting it is from an external source, this will assist users in detecting spoofed emails. 4. Implement a block policy for file attachments that are commonly associated with malware such as .dll, and .exe, and attachments that cannot be scanned by antivirus such a .zip files. 5. Implement Domain-Based Message Authentication, Reporting & Conformance (DMARC), a validation system that minimizes spam email by detecting email spoofing using Domain Name System (DNS) records and digital signatures. 6. Implement a solution that can send the unknown/suspicious files to the sandbox for further investigation and analysis. 7. And most importantly employee training on social engineering and phishing. Urge employees not to open suspicious emails, click links contained in such emails, or post sensitive information online. March 2019|34
- 38. he arrival of Chatbots is considered to be an incredible breakthrough in the realm of business or any kind of Tentrepreneurships. It is one of the smartest innovations by Artificial Intelligence (AI) and Natural Language Processing (NLP) that businesses can count on. The Chatbot is a software that can be programmed to carry out a certain set of actions all by itself, like a wind-up toy, in text or spoken formats. The capability of the bots to learn from the past interactions and grow in itself, makes it more attractive and interesting. Chatbots work in two different ways. Firstly, predefined responses are given from an existing database, based on the keywords searched by customers. The smart machine based bots attract their knowledge from Artificial Intelligence and Cognitive Computing and adapt their behavior based on the customer interactions. Applicability of Chatbots in Business: The applicability of these chatting bots is quite relevant in this era of digital glory. As the new tech-savvy generation of customers is always connected to the social platforms, they definitely expect a seamless and less time consuming customer experience with the brands they love. Econsultancy found in a research that 57% of customers prefer live chat to email or a phone call. There’s no surprise that consumers today are appreciating chatting or texting more than any other forms of communication. To address this priority of the customers and outgrow in this competitive business world, many business giants are adopting these virtual agents. March 2019|36 Tech Talk
- 39. A Dynamic Digital Gesture for Creative Entrepreneurs CHATBOTSCHATBOTS It’s a Smart Trend for Entrepreneurial Venture: With the widespread adoption of the artificial intelligence, the human interaction and connectivity has taken a fascinating turn. This extremely sophisticated and versatile tool can be helpful in crafting any small or big business plan. Apart from being awesome in resolving customer care queries, Chatbots can be a part of an entrepreneurial strategy in many ways. That’s where the appeal of Chatbots lies. There are many different approaches to navigate this connectivity tool throughout the business venture. Let’s have a look at some of these approaches: As every organization has a unique set of customers, the Chatbots must be programmed in accordance with customer journey. Knowing the finer details of the customer journey from A-Z, might be proved as the foundation for success. As AI is enacting a larger role in business reforms, having accurate foresight and experience is the most needed prerequisite to program the bot. After programming the bot, it should be designed in a way that would enhance customer success by advancing them down the sales funnel. A microscopic view of the customer service and sales data always helps in this regard. One should have a good grasp on: 37|March 2019
- 40. Ÿ Which patterns and questions are asked the most? Ÿ How the responses can be programmed to answer all of them? Ÿ And most importantly, in what way all the necessary information can be provided to bring people from awareness stage to a decision? In order to guide the customer seamlessly through the sales funnel with the help of the intelligent bot, an entrepreneur needs to put himself/herself in the shoes of the average customer and develop the bot around their path to success. To build strong relationships with customers, another smarter way is to “humanize” the Chatbot. People generally want to buy something from other people, not from a robot. Therefore, programming responses needs to be done in a way that reflects the character and personality of the brand. The Chatbot need to be designed with a tinge of human empathy with the authentic brand voice. Lastly, with the changing digital landscape, customer mindsets are also always in the verge of change. To stay on the top of the game, one must have to consistently analyze the data and evolve the bot accordingly. Future of Chatbots: Chatbots are currently being utilized as easy and fun ways on websites, social platforms and smartphones to assist customers in their interactions with a brand. Even if the Chatbots are still in rudimentary stage, we can expect a lot more progressions in this trend. With the gradual evolution of Artificial Intelligence and Deep Learning, the Chatbots will become more empowered to edify the conversational interface of businesses. Chatbots are going to get a lot smarter, more intelligent and indistinguishable from a human being with the advancement of AI. However, it will definitely take some trials and errors before the chatting robots master and adopt the delicacies of polite conversation. Also, it’s quite predictable that the cost of Chatbots will eventually get cheaper as the adoption of it increases across multiple domains. An example is Facebook’s decision to let third-party applications build Chatbots in their platform has drastically lowered the price. Conclusion: It really amazes us how far technology has come up in the last several years in the digital marketing arena. However, some things will always remain the same. Even if everything gets automated in the future, nothing will minimize the appeal of optimal user experience. The bots can be used to automate a huge chunk of the marketing process, but without making the process dull and impersonal. Only then these marvels of technology will be able to make wonders. March 2019|38
