System Security- Firewalls and ID System
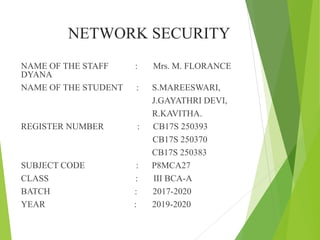
- 1. NETWORK SECURITY NAME OF THE STAFF : Mrs. M. FLORANCE DYANA NAME OF THE STUDENT : S.MAREESWARI, J.GAYATHRI DEVI, R.KAVITHA. REGISTER NUMBER : CB17S 250393 CB17S 250370 CB17S 250383 SUBJECT CODE : P8MCA27 CLASS : III BCA-A BATCH : 2017-2020 YEAR : 2019-2020
- 3. Introduction Intruders Classification of ID system Malicious software Types of virus Firewalls Characteristics of firewalls Firewalls responsibilities
- 4. Introduction The security mechanism of the system are designed so as to praventum authorized access to system resources and data. Intrusion detection (ID) is type of security management system for computers and networks. ID gathers and analyse information from various areas with in computer or a network to identify possible security breaches which include both intrusion and misuse. ID uses vulnerability assessment (scanning), that is software technology developed for assess the security of computer system or network.
- 5. INTRUDERS Intruder is a person who enters in territory that does not belongs to him Types: Masquerader Not authorized to use computer, penetrates system protection by the way of legitimate user account. Misfeasor A legitimate user who can access assets that he is not authorized to. Clandestine user A user who gains supervisory access to the system, can be either inside or outside.
- 6. Unauthorized access is an attempt for Accessing information. Manipulation of information. Render a system unreliable or unusable. Need for Intrusion Detection System To prevent problem behaviours. To detect attack and other security violation. To detect and deal with preambles of attack. To document the existing threats. quality control for security design and administration. To provide useful information about intrusion that is to take place, allowing improved diagnosis , recovery and corrections.
- 7. Intrution detection Monitoring and analysing both user and system activities. analysing system configurations and vulnerabilite. Assessing system and file security. Ability to recognize patterns of attacks. Analysis of abnormal activity patterns. Tracking user policy violation.
- 8. Classification of ID system Attempted break-ins : which are detected by atypical behaviour profiles or violation of security constraints. Masquerade Attacks: which are detected by atypical behaviour profiles. Penetration of security control system, which is detected by monitoring for specific patterns of activity. Leakage, which is detected by atypical use of system resources. Denial of Service, which is detected by atypical use of system resources Malicious.
- 9. Malicious software Is referred as Malware It includes computer viruses, worms, Trojans, spywares, and other programs written specially to spy network traffic, record private communications , executes unauthorized commands, steal and distribute private and confidential information , disable computers , erase files etc.
- 10. Types of viruses Parasitic viruses: Virus that attached self to file in order to propagation Boot Sector Virus. Polymorphic virus . A virus that changes its characteristics with each infections and makes detection more difficult. Virus that hides it stracks after in facting computer.
- 11. Macro virus Hybrids Email Viruses Types of Worms Email Worms Spreading goes through infected email messages Instant messaging worms Spreads via instant messaging applications by sending links to infected websites
- 12. Internet worms Will scan available network resources using local network or operating system service IRC worms Chat channels are the main target of this kind of worm File worms sharing and network Worm copies itself into shared folder
- 13. Trojan Horses Contains hidden code that, when invoked performs some unwanted function Only author of trojan horse program can have an access to source code of useful programs that is attractive to other users and then add code so that the program performs some harmful function in addition to its useful function. Spyware Is a programming that is put in someone’s computer to secretly gather information about the user and rely it to advertiser other interestedparties
- 14. FIREWALL Introduction Is a system designed to prevent unauthorized access to or from private network. It can be effective means of protecting local system or network of systems from unauthorized network users, at the same time affording access to the outside world via WAN and internet. Firewalls is the one of the first line defense in a network. They can be implemented both in hardware and software Firewall are most often configured to be transparent to internal network user and non transparent to outside network users. They are often installed between network of entire organization and internet, but could also be installed in an internet to protect individuals document.
- 15. Characteristics of firewalls All traffic between two network must pass through firewall Only traffic that is authorized by local security policy is permitted to pass The firewall itself is immune to penetration A firewall cannot guarantee protection from outside attack Firewall implementation requires risk analysis to define the level of protection Firewall policy is a competent of local policy
- 16. Firewalls responsibilities Block unwanted traffic Direct incoming traffic to more trustworthy internal system Hide vulnerable internal network system Hide internal network information such as system names, network topology, network device types, internal user id’s etc Provide more robust user authentication Benefits Increased ability to enforce network security standards/ policies Centralization of inter network audit capability
- 17. Limitation of firewalls Firewall does not provide data integrity Firewall do not check traffic not sent through them Firewall protect nothing if they have been compromised Firewall authenticate data packets at the transport and network layer. Firewall provides limited confidentiality Firewall do not protect against insider threats Encrypted traffic cannot ne examined and filtered