What are the important objectives of Cybersecurity.pdf
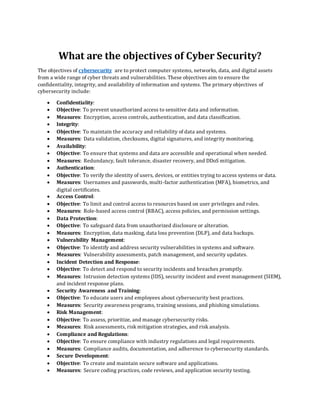
- 1. What are the objectives of Cyber Security? The objectives of cybersecurity are to protect computer systems, networks, data, and digital assets from a wide range of cyber threats and vulnerabilities. These objectives aim to ensure the confidentiality, integrity, and availability of information and systems. The primary objectives of cybersecurity include: • Confidentiality: • Objective: To prevent unauthorized access to sensitive data and information. • Measures: Encryption, access controls, authentication, and data classification. • Integrity: • Objective: To maintain the accuracy and reliability of data and systems. • Measures: Data validation, checksums, digital signatures, and integrity monitoring. • Availability: • Objective: To ensure that systems and data are accessible and operational when needed. • Measures: Redundancy, fault tolerance, disaster recovery, and DDoS mitigation. • Authentication: • Objective: To verify the identity of users, devices, or entities trying to access systems or data. • Measures: Usernames and passwords, multi-factor authentication (MFA), biometrics, and digital certificates. • Access Control: • Objective: To limit and control access to resources based on user privileges and roles. • Measures: Role-based access control (RBAC), access policies, and permission settings. • Data Protection: • Objective: To safeguard data from unauthorized disclosure or alteration. • Measures: Encryption, data masking, data loss prevention (DLP), and data backups. • Vulnerability Management: • Objective: To identify and address security vulnerabilities in systems and software. • Measures: Vulnerability assessments, patch management, and security updates. • Incident Detection and Response: • Objective: To detect and respond to security incidents and breaches promptly. • Measures: Intrusion detection systems (IDS), security incident and event management (SIEM), and incident response plans. • Security Awareness and Training: • Objective: To educate users and employees about cybersecurity best practices. • Measures: Security awareness programs, training sessions, and phishing simulations. • Risk Management: • Objective: To assess, prioritize, and manage cybersecurity risks. • Measures: Risk assessments, risk mitigation strategies, and risk analysis. • Compliance and Regulations: • Objective: To ensure compliance with industry regulations and legal requirements. • Measures: Compliance audits, documentation, and adherence to cybersecurity standards. • Secure Development: • Objective: To create and maintain secure software and applications. • Measures: Secure coding practices, code reviews, and application security testing.
- 2. • Ethical Hacking and Penetration Testing: • Objective: To proactively identify and address security weaknesses. • Measures: Penetration testing, vulnerability scanning, and red teaming exercises. • Security Policies and Procedures: • Objective: To establish and enforce security policies and guidelines. • Measures: Security policies, procedures, and security incident response plans. • Business Continuity and Disaster Recovery: • Objective: To ensure business operations can continue in the event of a cyber incident. • Measures: Disaster recovery plans, backup systems, and failover mechanisms. • User Privacy Protection: • Objective: To safeguard the privacy of users' personal information and data. • Measures: Privacy policies, data anonymization, and compliance with data protection regulations. These cybersecurity objectives collectively contribute to creating a robust and resilient cybersecurity posture for organizations and individuals, protecting them from the ever-evolving landscape of cyber threats and attacks Bytecode security offers 1 year diploma course in cybersecurity . IF you want to make your career in cybersecurity field, you can enroll now +91 9513805401 and visit our website : www.bytec0de.com
