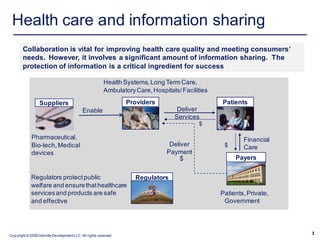
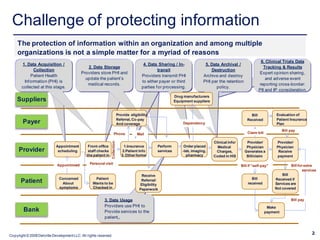
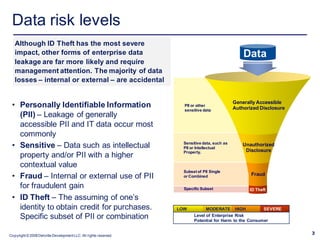
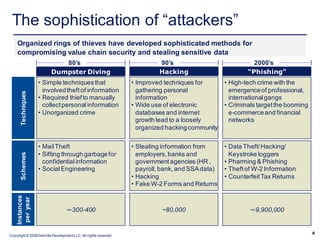
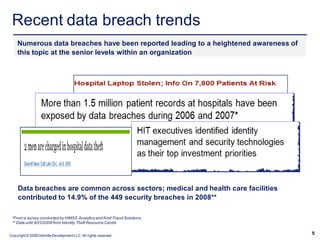
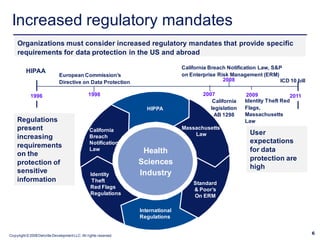
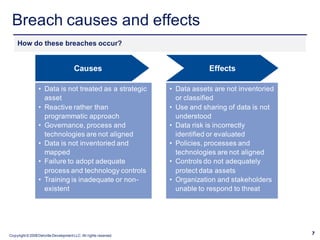
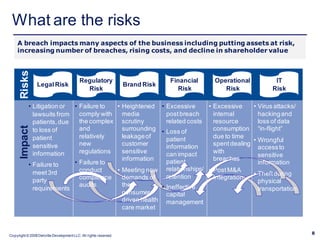
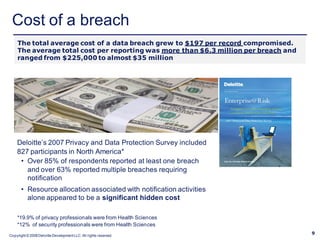
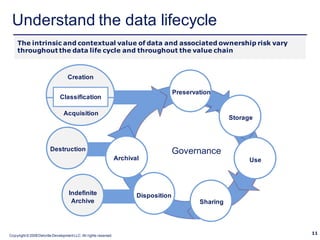
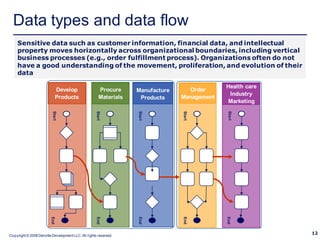
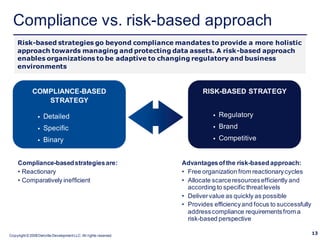
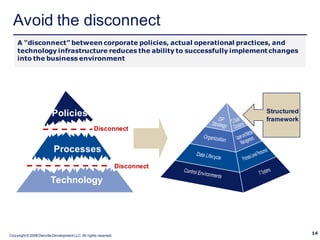
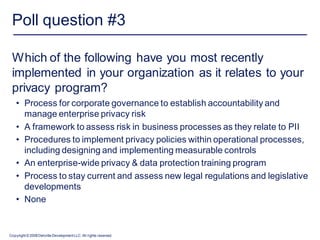
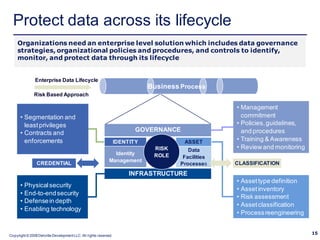
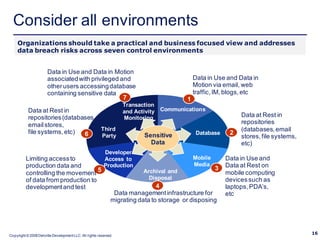
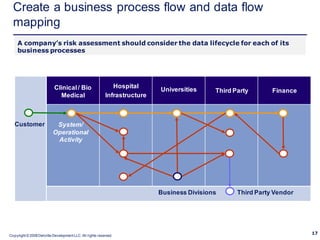
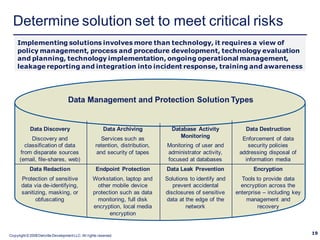
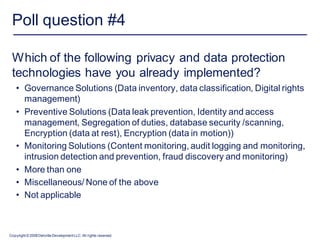
The document discusses the challenges and strategies involved in protecting sensitive patient health and personal data amidst increasing collaboration in healthcare. It highlights causes of data breaches, their impacts, and emphasizes the importance of adopting a risk-based approach to data protection and governance. Various regulatory mandates and the need for organizations to improve their data protection capabilities throughout the data lifecycle are also addressed.