Confident Technologies Overview
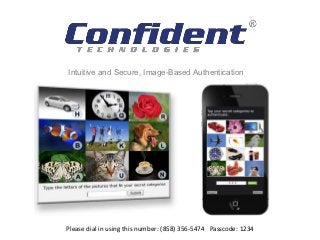
- 1. Intuitive and Secure, Image-Based Authentication Please dial in using this number: (858) 356-5474 Passcode: 1234
- 2. Who We Are Image-based authentication and verification solutions for web & mobile. • Image-based authentication for websites, mobile apps, or enterprise systems • Image-based multifactor authentication • Image-based CAPTCHA Strong patent portfolio • 17 independent patent filings • 5 patents already granted for image-based authentication, image-based password management and using authentication for advertising images • Main U.S. Patent: #8,117,458 "Methods and Systems for Graphical Image Authentication" Experienced executive team • Former executive leadership team from Websense, Inc. • Recently closed first tranche of $4 million Series B funding Company Confidential Information
- 3. Image-Based Authentication Confident ImageShield ™ Image-based authentication that generates one-time passwords by having users identify secret categories. 1. The first time a user registers with your website or app, they select a few categories of things they can easily remember Such as: dogs, flowers and cars 2. Whenever authentication is needed, the user is presented with a randomly-generated grid of images: the Confident ImageShield. ™ 3. Each image is randomly paired with an alphanumeric character. *** 4. The user looks for pictures that fit their secret categories – in this case, dogs, flowers and cars. The images, their location on the grid, and the alphanumeric By identifying the pictures, the user assembles characters are different every time – forming a one-time and submits a one-time password. password Company Confidential Information
- 4. Image-Based Authentication Confident ImageShield ™ Image-based authentication that generates one-time passwords by having users identify secret categories. Benefits: • Forms a temporary, one-time password (OTP) every time • More secure than static, text passwords of the user’s choice • Easy for people to remember & use Uses: • Replace text passwords • Add as a second layer of authentication • User authentication for password resets The images and letters are different every time, but the user • Replace security challenge questions will always look for their same • Anti-Phishing categories Company Confidential Information
- 5. Image-Based Authentication for Mobile Ideally suited for use on mobile devices, including smartphones and tablets. Users simply tap a few images on the touchscreen to form a one-time password (OTP) for authentication. Uses: • A fast, easy & secure login method for mobile apps • Protect sensitive data stored on mobile devices • Persistent login – simply tap a few images to quickly log back in after device/app has gone to sleep • Mobile transaction authorization • Securely enable BYOD Download Confident Notes in the App Store to see an example of how image-based authentication can be used in mobile apps. Company Confidential Information
- 6. Out-of-Band, Multifactor Authentication Confident Multifactor Authentication™ Out-of-band, multifactor verification using images 1. When multifactor authentication is needed, an image- based challenge is sent to the user’s mobile phone via an SMS hyperlink. 2. The user follows instructions to tap a series of specific images. 3. If the user correctly verifies, the web page on the PC proceeds automatically Benefits: • Fast and easy verification on a second factor • Remains entirely out-of-band • No need to type a code into the web page • No need to remember image categories Company Confidential Information
- 7. Out-of-Band, Multifactor Authentication Confident Multifactor Authentication™ -- Secure Second Factor Out-of-band, multi-layered, multifactor authentication using images 1. During enrollment, users choose a few secret categories, which they memorize 2. When multifactor authentication is needed, the organization sends an image-based challenge to the user’s mobile phone (via encrypted SMS or WAP push). Behind the scenes, each image is paired with alphanumeric characters. 3. To authenticate, the user taps the pictures that fit their secret authentication categories. By doing so, they are reassembling a one-time authentication code. 4. The one-time authentication code is sent to our servers for verification. The process remains completely out-of-band from the web session. Benefits: • Multi-layered, multi factor authentication that remains out-of-band • Generates a one-time authentication code • Easy to use • Not susceptible to typical SMS re-routing (Zeus in the Mobile Attacks) Company Confidential Information
- 8. Confident CAPTCHA An easy to use, image verification test that stops spam and bots on websites. Instead of deciphering illegible text, users simply click on a few pictures to prove they are human. Features: • Highly customizable – Determine the size of the image grid & the number of images users must click • International languages available • Audio option • Website administrators can upload their own logo and billboards for branding & online advertising Benefits: • More secure than text-based CAPTCHAs & easier to use • End user frustration & increase conversion rates • Engaging online advertising platform Company Confidential Information
- 9. Intuitive and Secure, Image-Based Authentication Thank You! www.ConfidentTechnologies.com
Editor's Notes
- The management team: Curt Staker CEO, Bill Goldbach EVP & Roman Yudkin CTO are all experienced security industry veterans who were responsible for the success and hyper growth at Websense circa 2001-2006 where revenues grew from $20 to $200 mil and a market cap of $1.3 billion. Please see the website for more detail on our experience. Curt went on to be CEO of GFI, Bill went onto VP of ScanSafe which was purchased by Cisco.Confident Technologies’ IP is very well protected with the core patent recently granted
- The images and their location on the ImageShield are different every time. Behind the scenes, each image is randomly paired with a series of alphanumeric characters. Therefore, when the user identifies their secret authentication categories by tapping the corresponding images, they are actually assembling a one-time password or one-time authentication code. Because the images are different every time and in a different location every time, it is not susceptible to keystroke or click logging malware, and the user’s fingerprints/smudges on the touchscreen will not give away their secret either.
- Forms a temporary, one-time password every time, which is more secure than a static, text-based password of the user’s choice. Much research has demonstrated that the human brain is better at recognizing images and remembering categories or common things, than remembering a long string of 12 upper and lowercase letters, numbers and symbols. Image-based authentication can be a stand alone strong authentication solution, or a layer of authentication inserted at any point.
- Our image-based authentication solutions are ideally suited for use on mobile devices. Our mobile SDK makes it very easy for mobile developers or businesses to integrate our authentication method into their mobile applications or devices.
- Some companies we’ve spoken with requested a multifactor authentication approach that does not require users to memorize categories. This version delivers an out-of-band verification to the user’s mobile phone. The user does not need to memorize any authentication categories. When multifactor authentication is needed, an image-based verification challenge is sent to the user’s mobile phone (typically via a hyperlink in an encrypted SMS message, which opens the image-based verification in their mobile browser). The user follows the instructions to click on a series of specific pictures. After the user follows the instructions to tap the appropriate pictures, their selection is sent back to our server which checks to see that they completed the verification process correctly. This version is not as secure as our Secure Second Factor shown on the previous slide, but it is still is a multifactor authentication solution that requires the user’s verification on a separate factor (the mobile phone) and remains completely out of band from the web session on the PC. It’s similar to the common approach used today of sending a one-time authentication code to the user in a text message but it remains out of band and it’s easier on the user because they don’t have to type a code into the web page.
- We provide two versions of our multifactor authentication solution. This version, (Secure Second Factor) is a multi-layer, multifactor authentication solution that remains entirely out of band. During enrollment with the website or application, the user chooses a few secret categories. When authentication is needed, we trigger an ImageShield to appear on the user’s mobile phone (typically through a WAP push). Behind the scenes, each image on the ImageShield has a series of alphanumeric characters randomly paired with it. To authenticate, the user must identify their secret categories by tapping the appropriate images. By doing so, they are essentially reassembling a one-time authentication code, which is sent back to our servers for verification. It is a multi-layered, multi-factor authentication solution because the user must apply something they know (their secret categories) on something they have (their mobile phone). It verifies that it is truly the legitimate user/account owner in possession of the mobile device (not a thief or a Zeus-in-the-mobile attack) The entire process remains completely out-of-band from the web session on the PC.
