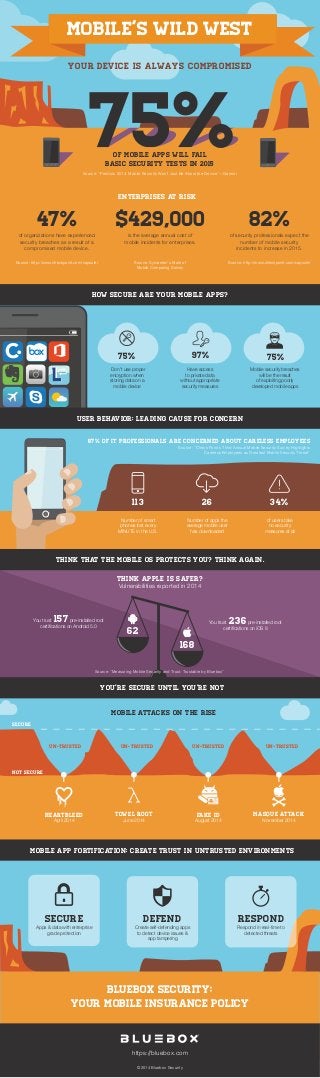
The Wild West of Mobile Security – What to look for in 2015
- 1. Bluebox Security: Your mobile insurance policy Think Apple is safer? Vulnerabilities reported in 2014 You trust 157pre-installed root certifications on Android 5.0 You trust 236pre-installed root certifications on iOS 8 Your DEVICE IS ALWAYS COMPROMISED MOBILE’s WILD WEST 97% Have access to private data without appropriate security measures 75% Don’t use proper encryption when storing data on a mobile device 113 Number of smart phones lost every MINUTE in the U.S. 26 Number of apps the average mobile user has downloaded 34% of users take no security measures at all Source: “Predicts 2014: Mobile Security Won't Just Be About the Device”—Gartner enterprises at risk MOBILE APP FORTIFICATION: CREATE TRUST IN UNTRUSTED ENVIRONMENTS 87% of IT professionals are concerned about careless employees Mobile attacks on the rise NOT SECURE UN-trusted UN-trusted UN-trusted UN-trusted SECURE Source: “Check Point’s Third Annual Mobile Security Survey Highlights Careless Employees as Greatest Mobile Security Threat” 75% Mobile security breaches will be the result of exploiting poorly developed mobile apps 62 168 HeaRTBLEED April 2014 FAKE ID August 2014 Towel ROOT June 2014 MaSQUE ATTACK November 2014 SECURE Apps & data with enterprise grade protection DEFEND Create self-defending apps to detect device issues & app tampering RESPOND Respond in real-time to detected threats ©2014 Bluebox Security https://bluebox.com Source: “Measuring Mobile Security and Trust: Trustable by Bluebox” of mobile apps will fail basic security tests in 2015 of organizations have experienced security breaches as a result of a compromised mobile device. Source: http://www.checkpoint.com/capsule/ is the average annual cost of mobile incidents for enterprises. Source: Symantec's State of Mobile Computing Survey HOW SECURE ARE YOUR MOBILE APPS? User Behavior: Leading Cause for Concern Think that the mobile OS protects you? Think again. of security professionals expect the number of mobile security incidents to increase in 2015. Source: http://www.checkpoint.com/capsule/ you’re secure until you’re not
