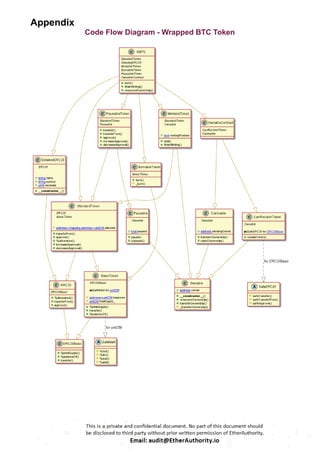
The BTC smart contract, when wrapped, inherits multiple contracts with varying functions:
CanReclaimToken: The contract is expected to be capable of recovering tokens.
Claimable: This enables the new owner to accept the transfer.
BurnableToken: A token that can be permanently destroyed.
MintableToken: The ERC20 token is a simple and mintable option for generating digital currency.
PausableToken: The StandardToken has been modified with the ability to make pausable transfers.
StandardToken: The implementation of the basic standard token.
BasicToken: The StandardToken is a basic version of the cryptocurrency, without any allowances.
Overall, this contract allows for the creation of Theta tokens with additional features for controlling token transfers, minting new tokens, and managing pre-circulation before a specified unlock time.