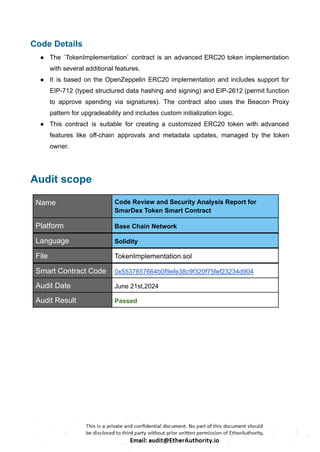
- SmarDex is a leading innovation for liquidity providers and traders who want to stay ahead of the game. Launch the app and start trading today.
- Smardex is a decentralized finance (DeFi) platform that aims to revolutionize trading and liquidity provision. It offers innovative solutions for users to engage in secure and efficient DeFi activities, including trading, staking, and liquidity management.
- The platform focuses on providing transparent and robust financial tools to enhance the DeFi experience.