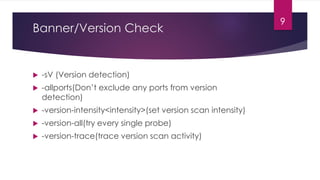
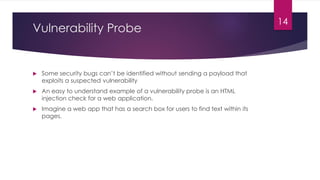
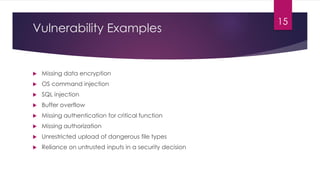
The document provides an overview of systems vulnerability scanning, defining vulnerabilities and discussing methods for scanning networks, systems, and applications to identify potential security risks. It highlights the importance of understanding open ports and services, conducting banner/version checks, and utilizing vulnerability probes to detect flaws. The conclusion emphasizes the need for caution and legal clearance before performing any network scans to avoid risks such as crashing servers.