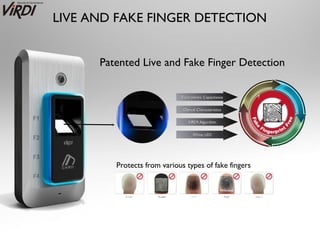
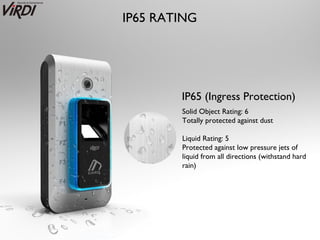
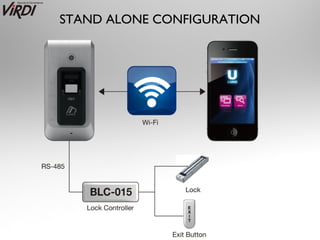
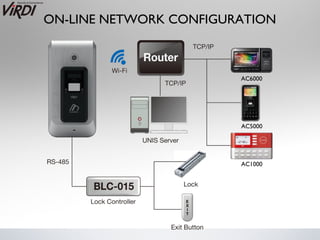
Smart-i is an advanced biometric access control system that integrates smartphone technology, featuring a fingerprint sensor with live and fake finger detection, and a 1.3 megapixel camera for verification. It supports up to 1,000 users and can log up to 1,000,000 entries, with robust IP65 rated housing for durability. The device offers multiple communication options and is compatible with various application platforms for enhanced functionality.