Report
Share
Recommended
Vim

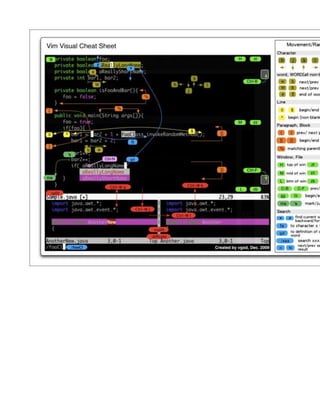
The document discusses a presentation given by Alkesh Vaghmaria on January 10th, 2012 to IPRUG about using the Vim text editor. It introduces Vim and its modes, combinations of operators and motions, and provides demos. It also lists ways Vim can be used in other applications and IDEs like Sublime Text and Cloud9 as well as browsers and email clients. Finally, it recommends resources for learning more about Vim configuration, tutorials, and a graphical cheat sheet.
Linux basics (part 2)

This document provides an overview of various Linux basics including the VIM text editor, networking commands, SSH secure shell, SSH keys, package management, package dependencies, services, Apache web server configuration, MySQL database server, caching, and configuration management tools like Puppet, CFEngine, and Chef. It discusses installing and using the popular Wordpress content management system on a Linux server.
Installation of Subversion on Ubuntu,...

The document provides instructions for installing Subversion on Ubuntu with Apache, SSL, and BasicAuth to allow hosting SVN repositories on a web server, including installing necessary packages, configuring Apache with a SSL certificate and virtual host, creating repositories under /var/svn, setting up authentication using htpasswd, and enabling WebDAV and SVN support in Apache.
Recommended
Vim

The document discusses a presentation given by Alkesh Vaghmaria on January 10th, 2012 to IPRUG about using the Vim text editor. It introduces Vim and its modes, combinations of operators and motions, and provides demos. It also lists ways Vim can be used in other applications and IDEs like Sublime Text and Cloud9 as well as browsers and email clients. Finally, it recommends resources for learning more about Vim configuration, tutorials, and a graphical cheat sheet.
Linux basics (part 2)

This document provides an overview of various Linux basics including the VIM text editor, networking commands, SSH secure shell, SSH keys, package management, package dependencies, services, Apache web server configuration, MySQL database server, caching, and configuration management tools like Puppet, CFEngine, and Chef. It discusses installing and using the popular Wordpress content management system on a Linux server.
Installation of Subversion on Ubuntu,...

The document provides instructions for installing Subversion on Ubuntu with Apache, SSL, and BasicAuth to allow hosting SVN repositories on a web server, including installing necessary packages, configuring Apache with a SSL certificate and virtual host, creating repositories under /var/svn, setting up authentication using htpasswd, and enabling WebDAV and SVN support in Apache.
Happiness is a Journey

Happiness is a journey, not a destination. The document discusses how people often tell themselves they will be happy once they achieve certain life goals or milestones, like getting married, having children, or retiring. However, challenges will always remain. True happiness is about finding contentment in the present moment and not waiting for the future to enjoy life. We must embrace each day as it comes and appreciate the time we have.
Linux Shortcuts and Commands:

This document provides shortcuts and commands for Linux. It begins with essential shortcuts for switching between terminals and GUI screens. It then provides summaries of commands for getting system information, basic file operations, and networking. Examples are given for most commands.
Linux Security Quick Reference Guide

This document provides a quick reference guide for Linux security that includes definitions of common security terms, general security tips, and Linux security resources. It defines terms like buffer overflow, cryptography, denial of service, and port scanning. It offers tips such as using automatic package managers to update software, configuring firewalls and intrusion detection, and enforcing strong password policies. The document also lists various security-related websites, books, and open source tools that can aid in hardening Linux systems.
issue35 zh-CN

The document describes a podcast called "Ubuntu UK Podcast" which is produced by members of the Ubuntu Linux community in the United Kingdom. The podcast aims to provide current information about Ubuntu Linux and free software to users around the world, covering all aspects from the command line to the latest GUI. As it is produced by the Ubuntu UK community, the podcast follows the Ubuntu Code of Conduct and is suitable for all ages.
ubunturef

This document provides a summary of common commands and configuration files used in Ubuntu systems for privileges, networking, display, package management, applications, services, and system recovery. It includes commands for sudo access, configuring networking and wireless settings, starting and stopping services, installing and removing packages, checking the system version, and rebooting the system through keyboard shortcuts. Configuration files like /etc/network/interfaces and /etc/X11/xorg.conf are also listed.
LINUX Admin Quick Reference

This document provides a summary of Linux system administration files and commands. It lists important configuration files such as /etc/passwd for user accounts, /etc/group for groups, and /etc/fstab for mounted filesystems. It also outlines commands for common system tasks like user management, networking, printing, and sendmail configuration.
Cool Object Building With PHP

This document proposes a solution for mapping database records to PHP objects using data access objects (DAOs) and builder classes. The DAO contains SQL queries to retrieve data from the database and calls a builder class to assemble the returned records into PHP objects. This allows returning objects instead of arrays and enables object caching. Examples of a base DAO class and a BlogComment builder class are provided to demonstrate how this works.
100 Essential Web Development Tools

This document provides a list of 100 essential web development tools organized into categories such as functions and classes, CAPTCHAs, date manipulation, image manipulation, form validation, Ajax and JavaScript tools, APIs, IP locations, charts and graphs, maps, audio players, video players, video conversion, and WYSIWYG editors. It introduces each category and provides 3-4 examples of tools for each to help developers find the right third-party solutions for their needs and save time in the development process. The author is Neil Skirrow, a professional web developer and director of a UK software company.
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
More Related Content
More from wensheng wei
Happiness is a Journey

Happiness is a journey, not a destination. The document discusses how people often tell themselves they will be happy once they achieve certain life goals or milestones, like getting married, having children, or retiring. However, challenges will always remain. True happiness is about finding contentment in the present moment and not waiting for the future to enjoy life. We must embrace each day as it comes and appreciate the time we have.
Linux Shortcuts and Commands:

This document provides shortcuts and commands for Linux. It begins with essential shortcuts for switching between terminals and GUI screens. It then provides summaries of commands for getting system information, basic file operations, and networking. Examples are given for most commands.
Linux Security Quick Reference Guide

This document provides a quick reference guide for Linux security that includes definitions of common security terms, general security tips, and Linux security resources. It defines terms like buffer overflow, cryptography, denial of service, and port scanning. It offers tips such as using automatic package managers to update software, configuring firewalls and intrusion detection, and enforcing strong password policies. The document also lists various security-related websites, books, and open source tools that can aid in hardening Linux systems.
issue35 zh-CN

The document describes a podcast called "Ubuntu UK Podcast" which is produced by members of the Ubuntu Linux community in the United Kingdom. The podcast aims to provide current information about Ubuntu Linux and free software to users around the world, covering all aspects from the command line to the latest GUI. As it is produced by the Ubuntu UK community, the podcast follows the Ubuntu Code of Conduct and is suitable for all ages.
ubunturef

This document provides a summary of common commands and configuration files used in Ubuntu systems for privileges, networking, display, package management, applications, services, and system recovery. It includes commands for sudo access, configuring networking and wireless settings, starting and stopping services, installing and removing packages, checking the system version, and rebooting the system through keyboard shortcuts. Configuration files like /etc/network/interfaces and /etc/X11/xorg.conf are also listed.
LINUX Admin Quick Reference

This document provides a summary of Linux system administration files and commands. It lists important configuration files such as /etc/passwd for user accounts, /etc/group for groups, and /etc/fstab for mounted filesystems. It also outlines commands for common system tasks like user management, networking, printing, and sendmail configuration.
Cool Object Building With PHP

This document proposes a solution for mapping database records to PHP objects using data access objects (DAOs) and builder classes. The DAO contains SQL queries to retrieve data from the database and calls a builder class to assemble the returned records into PHP objects. This allows returning objects instead of arrays and enables object caching. Examples of a base DAO class and a BlogComment builder class are provided to demonstrate how this works.
100 Essential Web Development Tools

This document provides a list of 100 essential web development tools organized into categories such as functions and classes, CAPTCHAs, date manipulation, image manipulation, form validation, Ajax and JavaScript tools, APIs, IP locations, charts and graphs, maps, audio players, video players, video conversion, and WYSIWYG editors. It introduces each category and provides 3-4 examples of tools for each to help developers find the right third-party solutions for their needs and save time in the development process. The author is Neil Skirrow, a professional web developer and director of a UK software company.
More from wensheng wei (20)
Recently uploaded
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
Essentials of Automations: Exploring Attributes & Automation Parameters

Building automations in FME Flow can save time, money, and help businesses scale by eliminating data silos and providing data to stakeholders in real-time. One essential component to orchestrating complex automations is the use of attributes & automation parameters (both formerly known as “keys”). In fact, it’s unlikely you’ll ever build an Automation without using these components, but what exactly are they?
Attributes & automation parameters enable the automation author to pass data values from one automation component to the next. During this webinar, our FME Flow Specialists will cover leveraging the three types of these output attributes & parameters in FME Flow: Event, Custom, and Automation. As a bonus, they’ll also be making use of the Split-Merge Block functionality.
You’ll leave this webinar with a better understanding of how to maximize the potential of automations by making use of attributes & automation parameters, with the ultimate goal of setting your enterprise integration workflows up on autopilot.
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Gursev Pirge, PhD
Senior Data Scientist - JohnSnowLabs
Principle of conventional tomography-Bibash Shahi ppt..pptx

before the computed tomography, it had been widely used.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/temporal-event-neural-networks-a-more-efficient-alternative-to-the-transformer-a-presentation-from-brainchip/
Chris Jones, Director of Product Management at BrainChip , presents the “Temporal Event Neural Networks: A More Efficient Alternative to the Transformer” tutorial at the May 2024 Embedded Vision Summit.
The expansion of AI services necessitates enhanced computational capabilities on edge devices. Temporal Event Neural Networks (TENNs), developed by BrainChip, represent a novel and highly efficient state-space network. TENNs demonstrate exceptional proficiency in handling multi-dimensional streaming data, facilitating advancements in object detection, action recognition, speech enhancement and language model/sequence generation. Through the utilization of polynomial-based continuous convolutions, TENNs streamline models, expedite training processes and significantly diminish memory requirements, achieving notable reductions of up to 50x in parameters and 5,000x in energy consumption compared to prevailing methodologies like transformers.
Integration with BrainChip’s Akida neuromorphic hardware IP further enhances TENNs’ capabilities, enabling the realization of highly capable, portable and passively cooled edge devices. This presentation delves into the technical innovations underlying TENNs, presents real-world benchmarks, and elucidates how this cutting-edge approach is positioned to revolutionize edge AI across diverse applications.What is an RPA CoE? Session 1 – CoE Vision

In the first session, we will review the organization's vision and how this has an impact on the COE Structure.
Topics covered:
• The role of a steering committee
• How do the organization’s priorities determine CoE Structure?
Speaker:
Chris Bolin, Senior Intelligent Automation Architect Anika Systems
Astute Business Solutions | Oracle Cloud Partner |

Your goto partner for Oracle Cloud, PeopleSoft, E-Business Suite, and Ellucian Banner. We are a firm specialized in managed services and consulting.
Recently uploaded (20)
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Northern Engraving | Nameplate Manufacturing Process - 2024

Northern Engraving | Nameplate Manufacturing Process - 2024
Dandelion Hashtable: beyond billion requests per second on a commodity server

Dandelion Hashtable: beyond billion requests per second on a commodity server
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency
JavaLand 2024: Application Development Green Masterplan

JavaLand 2024: Application Development Green Masterplan
Essentials of Automations: Exploring Attributes & Automation Parameters

Essentials of Automations: Exploring Attributes & Automation Parameters
Harnessing the Power of NLP and Knowledge Graphs for Opioid Research

Harnessing the Power of NLP and Knowledge Graphs for Opioid Research
Principle of conventional tomography-Bibash Shahi ppt..pptx

Principle of conventional tomography-Bibash Shahi ppt..pptx
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...

“Temporal Event Neural Networks: A More Efficient Alternative to the Transfor...
Astute Business Solutions | Oracle Cloud Partner |

Astute Business Solutions | Oracle Cloud Partner |
