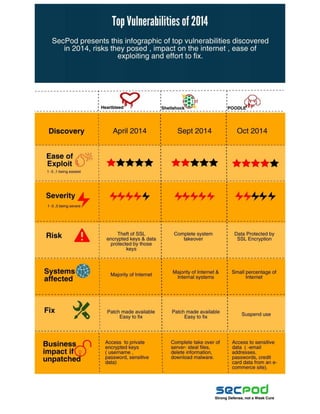
Top Vulnerabilities Of 2014
•
0 likes•144 views
Take a look at the top vulnerabilities of 2014, risks posed by them, their impact on internet and the ease of exploiting and fixing them.
Report
Share
Report
Share
Download to read offline
Recommended
How BlueHat Cyber Uses SanerNow to Automate Patch Management and Beyond

It’s widely known that patch management is a major pain point for most businesses. IT teams struggle to keep systems patched and secure. Cyber-attacks are continuous and anti-virus protection alone isn’t effective.
Cyber hygiene best practices need to be followed to keep organizations secure and to prevent security breaches.
In this webinar, Chandrashekhar - SecPod’s Founder & CEO, Douglas Smith - BlueHat Cyber’s Senior Sales Director, and Greg Pottebaum - SecPod’s VP OEM & Strategic Alliances, demonstrate:
- How to efficiently reduce the cyber-attack surface of your business
- Simple strategies to improve your security management
- How Blue Hat Cyber uses SanerNow to automate patch management and secure their customer’s endpoints
Request a FREE Demo of SanerNow platform at:
www.secpod.com
About SecPod
SecPod is an endpoint security and management technology company. SecPod (Security Podium, incarnated as SecPod)
was founded in the year 2008. SecPod’s SanerNow platform and tools are used by MSPs and enterprises worldwide.
SecPod also licenses security technology to top security vendors through its SCAP Content Professional Feed.
Facebook: https://www.facebook.com/secpod/
LinkedIn: https://www.linkedin.com/company/secp...
Twitter: https://twitter.com/SecPod
Email us at info@secpod.com to get more details on how to secure your organisation from cyber attacks.
8 Types of Cyber Attacks That Can Bother CISOs in 2020

What are cyber attacks?
In simple terms, cyber attacks are attempts of disabling or stealing information from other computers, by gaining access to admin privileges to them.
Why should businesses be worried?
An average ransomware attack costs a company $5 million. Attackers target all types of businesses, small and large, healthcare, banking & finance, manufacturing, education, even government. The internet has made life a lot easier for business owners, at the same time it has made them easier to get hacked.
Security threats

Human threats pose the greatest risk to organizations, costing over $100 billion annually worldwide through hacking and social engineering. Network security threats like malware, viruses, and phishing attacks are common, with over 45% requiring user interaction via email. Physical security is often overlooked despite threats from theft, sabotage, and terrorism. Software threats can attack through logic bombs, trojans, worms and viruses.
Hacking Internet of Things (IoT)

The document discusses vulnerabilities in IoT devices and provides examples of potential threats, including hacking a Jeep remotely and changing the target of a smart sniper rifle. It then summarizes challenges in securing IoT devices like limited resources, difficulty upgrading firmware, and lack of security software. Guidelines are provided for vendors, developers, and users to improve IoT security, such as using encryption, patching vulnerabilities, and educating users. Finally, the document demonstrates hacking a DTH set-top box by disturbing service, recording shows without permission, and stealing recordings.
WHY MSSPs LOVE OUR SOLUTION

Managed security service providers (MSSPs) value the Saner Business endpoint security solution for its ability to:
1) Find and eliminate vulnerabilities across networks in an automated and simple way.
2) Offer discrete security services and support regulatory compliance standards through continual assessment and remediation.
3) Provide continuous monitoring and detection of advanced threats that other solutions may overlook.
Many products-no-security (1)

The document discusses the challenges of managing IT security with many individual point products that have overlapping functionality and features. It introduces the SecPod SanerNow platform as a single platform approach for provisioning various security and endpoint management tools on demand to address specific tasks in a simpler and more cost-effective manner. Key benefits highlighted include reducing costs by up to 60%, easing management and improving security through continuous monitoring, vulnerability assessment, and threat detection and response capabilities.
SanerNow Endpoint Management

SanerNow Endpoint Management (EM) is a cloud-delivered
service that allows complete control over all your endpoint
systems. It provides visibility into the status of endpoints and
equips you with hundreds of built-in checks. SanerNow
Endpoint Management provides necessary features for
managing endpoints.
SanerNow Asset Management

SanerNow Asset Management (AM) is a cloud-delivered
service that tracks assets installed on hosts, the open
vulnerabilities in the OS and applications, their patch or update
levels, and prioritizes remediation tasks - all critical to the
deep visibility required to prevent attacks and data breaches.
Recommended
How BlueHat Cyber Uses SanerNow to Automate Patch Management and Beyond

It’s widely known that patch management is a major pain point for most businesses. IT teams struggle to keep systems patched and secure. Cyber-attacks are continuous and anti-virus protection alone isn’t effective.
Cyber hygiene best practices need to be followed to keep organizations secure and to prevent security breaches.
In this webinar, Chandrashekhar - SecPod’s Founder & CEO, Douglas Smith - BlueHat Cyber’s Senior Sales Director, and Greg Pottebaum - SecPod’s VP OEM & Strategic Alliances, demonstrate:
- How to efficiently reduce the cyber-attack surface of your business
- Simple strategies to improve your security management
- How Blue Hat Cyber uses SanerNow to automate patch management and secure their customer’s endpoints
Request a FREE Demo of SanerNow platform at:
www.secpod.com
About SecPod
SecPod is an endpoint security and management technology company. SecPod (Security Podium, incarnated as SecPod)
was founded in the year 2008. SecPod’s SanerNow platform and tools are used by MSPs and enterprises worldwide.
SecPod also licenses security technology to top security vendors through its SCAP Content Professional Feed.
Facebook: https://www.facebook.com/secpod/
LinkedIn: https://www.linkedin.com/company/secp...
Twitter: https://twitter.com/SecPod
Email us at info@secpod.com to get more details on how to secure your organisation from cyber attacks.
8 Types of Cyber Attacks That Can Bother CISOs in 2020

What are cyber attacks?
In simple terms, cyber attacks are attempts of disabling or stealing information from other computers, by gaining access to admin privileges to them.
Why should businesses be worried?
An average ransomware attack costs a company $5 million. Attackers target all types of businesses, small and large, healthcare, banking & finance, manufacturing, education, even government. The internet has made life a lot easier for business owners, at the same time it has made them easier to get hacked.
Security threats

Human threats pose the greatest risk to organizations, costing over $100 billion annually worldwide through hacking and social engineering. Network security threats like malware, viruses, and phishing attacks are common, with over 45% requiring user interaction via email. Physical security is often overlooked despite threats from theft, sabotage, and terrorism. Software threats can attack through logic bombs, trojans, worms and viruses.
Hacking Internet of Things (IoT)

The document discusses vulnerabilities in IoT devices and provides examples of potential threats, including hacking a Jeep remotely and changing the target of a smart sniper rifle. It then summarizes challenges in securing IoT devices like limited resources, difficulty upgrading firmware, and lack of security software. Guidelines are provided for vendors, developers, and users to improve IoT security, such as using encryption, patching vulnerabilities, and educating users. Finally, the document demonstrates hacking a DTH set-top box by disturbing service, recording shows without permission, and stealing recordings.
WHY MSSPs LOVE OUR SOLUTION

Managed security service providers (MSSPs) value the Saner Business endpoint security solution for its ability to:
1) Find and eliminate vulnerabilities across networks in an automated and simple way.
2) Offer discrete security services and support regulatory compliance standards through continual assessment and remediation.
3) Provide continuous monitoring and detection of advanced threats that other solutions may overlook.
Many products-no-security (1)

The document discusses the challenges of managing IT security with many individual point products that have overlapping functionality and features. It introduces the SecPod SanerNow platform as a single platform approach for provisioning various security and endpoint management tools on demand to address specific tasks in a simpler and more cost-effective manner. Key benefits highlighted include reducing costs by up to 60%, easing management and improving security through continuous monitoring, vulnerability assessment, and threat detection and response capabilities.
SanerNow Endpoint Management

SanerNow Endpoint Management (EM) is a cloud-delivered
service that allows complete control over all your endpoint
systems. It provides visibility into the status of endpoints and
equips you with hundreds of built-in checks. SanerNow
Endpoint Management provides necessary features for
managing endpoints.
SanerNow Asset Management

SanerNow Asset Management (AM) is a cloud-delivered
service that tracks assets installed on hosts, the open
vulnerabilities in the OS and applications, their patch or update
levels, and prioritizes remediation tasks - all critical to the
deep visibility required to prevent attacks and data breaches.
SanerNow Patch Management

SanerNow Patch Management (PM) is a cloud-delivered
service that identifies and automatically rolls out patches
according to rules and jobs defined by the user. If necessary, it
automatically reboots systems after applying patches and can
roll back installed patches. SanerNow’s patch management
process is timely, responsive and systematically managed.
SanerNow Vulnerability Management

SanerNow Vulnerability Management (VM) is a cloud delivered
service that performs an automated daily vulnerability scan. Organizations can discover their threat and vulnerability risk in less than five minutes. SanerNow VM provides continuous visibility into IT systems. Its time-testedSCAP Feed database delivers comprehensive vulnerability coverage.
SanerNow platform-datasheet

Many Products, No Security
So many products: Organizations invest in multiple products, many with overlapping
capabilities. And investments are huge when considering the cost of products,maintenance, professional services, training and vendor management.
Many products-no-security

Expensive products with complicated and
overlapping functionality aren’t meeting today’s
security and system management needs.
SanerNow a platform for Endpoint security and systems Management

Endpoint security can be more effective and less costly by simplifying management through a unified platform rather than multiple point products. Currently, organizations invest heavily in numerous security products yet still struggle with attacks, complexity, and high costs. A single platform called SanerNow provides tools to automate tasks like vulnerability management, patching, and threat detection through continuous monitoring from the cloud. It aims to reduce security costs by up to 60% by addressing issues holistically rather than relying on numerous specialized products with overlapping functionality.
Healthcare's Fight Against Ransomware 

Healthcare industry is becoming a popular victim to ransowmare attacks. The following infographic based on some study and statistics depicts the healthcare industry's fight against ransomware.
Take a sneak peek into Saner 2.0

SecPod Saner is an endpoint security solution that provides continuous visibility and control over endpoints. It proactively remediates risks and detects and responds to threats using vulnerability management, patch management, compliance management, and endpoint threat detection and response. Saner allows administrators to gain wide visibility into endpoint activities, create rules to monitor for deviations and fix issues, manage transient devices to keep them protected and up-to-date, create and enforce security compliance policies, and view real-time status reports.
Msp saner 2.0

This document discusses an endpoint security as a service offering that provides continuous endpoint visibility and control. It allows organizations to offer compelling security services by providing visibility into risks, automatically detecting and fixing vulnerabilities in real-time, and ensuring compliance. This increases client revenue through expanded services and introduces new services while also increasing profit margins by maximizing client value and minimizing technical resource costs. The document then introduces a new proactive approach to endpoint security using Saner, which provides real-time endpoint visibility, automatically fixes vulnerabilities and misconfigurations, and detects and responds to threats in seconds through prevention-first capabilities.
Saner 2.0

Saner is an endpoint security solution that provides continuous visibility and control of endpoints. It takes a proactive approach to security by detecting threats and responding before exploits can occur. Saner collects security posture data from endpoints and correlates it with threat intelligence to detect risks and indicators of compromise in real-time. It then automatically fixes vulnerabilities, misconfigurations, and responds to incidents. The solution aims to simplify and automate endpoint security management while reducing costs and ensuring compliance.
Saner 2.0 product sheet

SecPod Saner provides continuous visibility and control for all endpoints. It proactively remediates risks and detects and responds to threats. Saner combines endpoint vulnerability, patch and compliance management with endpoint threat detection and response into one easy to manage solution.
Ransomware - A look back

Ransomware has evolved since its origins in 1989 when the first known "AIDS" trojan spread via floppy disks. There are two main types - locker ransomware that denies access to devices, and crypto ransomware that encrypts files until ransom is paid. Notable examples like Cryptolocker and CryptoLocker have targeted home users, businesses, and public agencies on computers, servers, and mobile devices. Ransomware infects through malicious advertisements, spam emails, downloaders, botnets, and social engineering. Profits from ransomware have grown substantially, reaching over $18 million in 2015. Ransomware impacts many countries worldwide, with payments typically demanded through vouchers or bitcoins.
Worst security data breaches till 2015 - SecPod

The document summarizes major data security breaches from 2006 to 2015. It provides details on the impact and source of each breach. Some key breaches included:
- 2006: Personal information of 26.5 million veterans stolen from a Department of Veterans Affairs database stored on a stolen laptop and hard drive.
- 2007: A Fidelity National Information Services employee stole customer records of 3.2 million people.
- 2013: Hackers gained access to payment card information for up to 110 million Target customers through compromised third-party vendors.
Our talk in Black Hat Asia 2015 Briefing 

In this whitepaper, presented at Black Hat Asia 2015 Briefing session, we highlight how even if the Security Content Automation Protocol (SCAP) federates a number of open standards that are used to enumerate software
flaws and configuration issues related to security, there is a need for having a unique common metadata schema to represent important aspects relevant for designing efficient search engines
Changing L andscape Of Cyber Attacks

Infographic on how landscape of cyber attacks have changed to become more effective and precise.
Cost Of Cyber Crime

Infographic on the increasing cost of cyber crime and how it affects an organisation.
Perception vs reality of cyber security

Infographic on how CISOs and IT Managers perceive their organization’s security and how different it is from reality.
Vulnerabilities By Numbers

Infographic on the increasing number of vulnerabilities,where they reside, OS and the applications they affect
Vulnerabilities: Cause And Effect

Take a look at the main cause for vulnerabilities to exploit endpoints, top industries it affects and how breached occur.
Managing Compliance

For an organization to function efficiently it is important to have security controls to ensure the protection of confidentiality, integrity and availability of information and systems. Compliance is the process of ensuring all systems in an organization met a set of predefined specific rules.
In this article we will address the need for compliance automation and how SecPod’s Saner provides enterprises the ability to automate compliance while minimizing time spent on non-compliant state.
Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf

When it comes to unit testing in the .NET ecosystem, developers have a wide range of options available. Among the most popular choices are NUnit, XUnit, and MSTest. These unit testing frameworks provide essential tools and features to help ensure the quality and reliability of code. However, understanding the differences between these frameworks is crucial for selecting the most suitable one for your projects.
Digital Marketing Trends in 2024 | Guide for Staying Ahead

https://www.wask.co/ebooks/digital-marketing-trends-in-2024
Feeling lost in the digital marketing whirlwind of 2024? Technology is changing, consumer habits are evolving, and staying ahead of the curve feels like a never-ending pursuit. This e-book is your compass. Dive into actionable insights to handle the complexities of modern marketing. From hyper-personalization to the power of user-generated content, learn how to build long-term relationships with your audience and unlock the secrets to success in the ever-shifting digital landscape.
More Related Content
More from SecPod Technologies
SanerNow Patch Management

SanerNow Patch Management (PM) is a cloud-delivered
service that identifies and automatically rolls out patches
according to rules and jobs defined by the user. If necessary, it
automatically reboots systems after applying patches and can
roll back installed patches. SanerNow’s patch management
process is timely, responsive and systematically managed.
SanerNow Vulnerability Management

SanerNow Vulnerability Management (VM) is a cloud delivered
service that performs an automated daily vulnerability scan. Organizations can discover their threat and vulnerability risk in less than five minutes. SanerNow VM provides continuous visibility into IT systems. Its time-testedSCAP Feed database delivers comprehensive vulnerability coverage.
SanerNow platform-datasheet

Many Products, No Security
So many products: Organizations invest in multiple products, many with overlapping
capabilities. And investments are huge when considering the cost of products,maintenance, professional services, training and vendor management.
Many products-no-security

Expensive products with complicated and
overlapping functionality aren’t meeting today’s
security and system management needs.
SanerNow a platform for Endpoint security and systems Management

Endpoint security can be more effective and less costly by simplifying management through a unified platform rather than multiple point products. Currently, organizations invest heavily in numerous security products yet still struggle with attacks, complexity, and high costs. A single platform called SanerNow provides tools to automate tasks like vulnerability management, patching, and threat detection through continuous monitoring from the cloud. It aims to reduce security costs by up to 60% by addressing issues holistically rather than relying on numerous specialized products with overlapping functionality.
Healthcare's Fight Against Ransomware 

Healthcare industry is becoming a popular victim to ransowmare attacks. The following infographic based on some study and statistics depicts the healthcare industry's fight against ransomware.
Take a sneak peek into Saner 2.0

SecPod Saner is an endpoint security solution that provides continuous visibility and control over endpoints. It proactively remediates risks and detects and responds to threats using vulnerability management, patch management, compliance management, and endpoint threat detection and response. Saner allows administrators to gain wide visibility into endpoint activities, create rules to monitor for deviations and fix issues, manage transient devices to keep them protected and up-to-date, create and enforce security compliance policies, and view real-time status reports.
Msp saner 2.0

This document discusses an endpoint security as a service offering that provides continuous endpoint visibility and control. It allows organizations to offer compelling security services by providing visibility into risks, automatically detecting and fixing vulnerabilities in real-time, and ensuring compliance. This increases client revenue through expanded services and introduces new services while also increasing profit margins by maximizing client value and minimizing technical resource costs. The document then introduces a new proactive approach to endpoint security using Saner, which provides real-time endpoint visibility, automatically fixes vulnerabilities and misconfigurations, and detects and responds to threats in seconds through prevention-first capabilities.
Saner 2.0

Saner is an endpoint security solution that provides continuous visibility and control of endpoints. It takes a proactive approach to security by detecting threats and responding before exploits can occur. Saner collects security posture data from endpoints and correlates it with threat intelligence to detect risks and indicators of compromise in real-time. It then automatically fixes vulnerabilities, misconfigurations, and responds to incidents. The solution aims to simplify and automate endpoint security management while reducing costs and ensuring compliance.
Saner 2.0 product sheet

SecPod Saner provides continuous visibility and control for all endpoints. It proactively remediates risks and detects and responds to threats. Saner combines endpoint vulnerability, patch and compliance management with endpoint threat detection and response into one easy to manage solution.
Ransomware - A look back

Ransomware has evolved since its origins in 1989 when the first known "AIDS" trojan spread via floppy disks. There are two main types - locker ransomware that denies access to devices, and crypto ransomware that encrypts files until ransom is paid. Notable examples like Cryptolocker and CryptoLocker have targeted home users, businesses, and public agencies on computers, servers, and mobile devices. Ransomware infects through malicious advertisements, spam emails, downloaders, botnets, and social engineering. Profits from ransomware have grown substantially, reaching over $18 million in 2015. Ransomware impacts many countries worldwide, with payments typically demanded through vouchers or bitcoins.
Worst security data breaches till 2015 - SecPod

The document summarizes major data security breaches from 2006 to 2015. It provides details on the impact and source of each breach. Some key breaches included:
- 2006: Personal information of 26.5 million veterans stolen from a Department of Veterans Affairs database stored on a stolen laptop and hard drive.
- 2007: A Fidelity National Information Services employee stole customer records of 3.2 million people.
- 2013: Hackers gained access to payment card information for up to 110 million Target customers through compromised third-party vendors.
Our talk in Black Hat Asia 2015 Briefing 

In this whitepaper, presented at Black Hat Asia 2015 Briefing session, we highlight how even if the Security Content Automation Protocol (SCAP) federates a number of open standards that are used to enumerate software
flaws and configuration issues related to security, there is a need for having a unique common metadata schema to represent important aspects relevant for designing efficient search engines
Changing L andscape Of Cyber Attacks

Infographic on how landscape of cyber attacks have changed to become more effective and precise.
Cost Of Cyber Crime

Infographic on the increasing cost of cyber crime and how it affects an organisation.
Perception vs reality of cyber security

Infographic on how CISOs and IT Managers perceive their organization’s security and how different it is from reality.
Vulnerabilities By Numbers

Infographic on the increasing number of vulnerabilities,where they reside, OS and the applications they affect
Vulnerabilities: Cause And Effect

Take a look at the main cause for vulnerabilities to exploit endpoints, top industries it affects and how breached occur.
Managing Compliance

For an organization to function efficiently it is important to have security controls to ensure the protection of confidentiality, integrity and availability of information and systems. Compliance is the process of ensuring all systems in an organization met a set of predefined specific rules.
In this article we will address the need for compliance automation and how SecPod’s Saner provides enterprises the ability to automate compliance while minimizing time spent on non-compliant state.
More from SecPod Technologies (20)
SanerNow a platform for Endpoint security and systems Management

SanerNow a platform for Endpoint security and systems Management
Recently uploaded
Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf

When it comes to unit testing in the .NET ecosystem, developers have a wide range of options available. Among the most popular choices are NUnit, XUnit, and MSTest. These unit testing frameworks provide essential tools and features to help ensure the quality and reliability of code. However, understanding the differences between these frameworks is crucial for selecting the most suitable one for your projects.
Digital Marketing Trends in 2024 | Guide for Staying Ahead

https://www.wask.co/ebooks/digital-marketing-trends-in-2024
Feeling lost in the digital marketing whirlwind of 2024? Technology is changing, consumer habits are evolving, and staying ahead of the curve feels like a never-ending pursuit. This e-book is your compass. Dive into actionable insights to handle the complexities of modern marketing. From hyper-personalization to the power of user-generated content, learn how to build long-term relationships with your audience and unlock the secrets to success in the ever-shifting digital landscape.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
AWS Cloud Cost Optimization Presentation.pptx

This presentation provides valuable insights into effective cost-saving techniques on AWS. Learn how to optimize your AWS resources by rightsizing, increasing elasticity, picking the right storage class, and choosing the best pricing model. Additionally, discover essential governance mechanisms to ensure continuous cost efficiency. Whether you are new to AWS or an experienced user, this presentation provides clear and practical tips to help you reduce your cloud costs and get the most out of your budget.
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on integration of Salesforce with Bonterra Impact Management.
Interested in deploying an integration with Salesforce for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
Recently uploaded (20)
Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf

Nunit vs XUnit vs MSTest Differences Between These Unit Testing Frameworks.pdf
Digital Marketing Trends in 2024 | Guide for Staying Ahead

Digital Marketing Trends in 2024 | Guide for Staying Ahead
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...

Salesforce Integration for Bonterra Impact Management (fka Social Solutions A...
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean lotus Threat actors project by John Sitima 2024 (1).pptx
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
