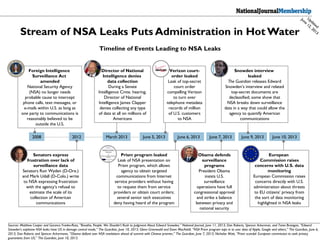
Timeline of National Security Agency Leaks
•
2 likes•639 views
Comprehensive graphic timeline of the events leading to and stemming from recent National Security Agency leaks. Members can see updates to this slide as news breaks.
Report
Share
Report
Share
Recommended
Parenting & Education using mobile phone

We are no more in 1990s, many time-demanding day-to-day activities must go on mobile and that is why Edves Basic gives educators and parents access to teaching, learning and parenting children/students on mobile devices
C U R R I C U L U M V I T A E

Marwan Jaber al amin is a Lebanese citizen currently pursuing a Master's degree in accounting from the Lebanese University in Nabatieh. He received his Bachelor's degree in business administration from the same university, majoring in accounting, finance, law, management, marketing, and math/economics. His work experience includes positions as a salesman and trainee in accounting, banking, and retail. He is fluent in Arabic, French, and English and has advanced knowledge of accounting, office software, marketing, and management. His hobbies include soccer and swimming.
Tipos de virus y antivirus

El documento describe diferentes tipos de virus informáticos como Caballo de Troya, gusano o worm y spyware. Luego menciona algunos antivirus populares como Avast, diseñado por Alwil Software que es ampliamente usado en hogares y empresas, y Kaspersky que protege redes completas y detecta páginas web sospechosas e identifica nuevas amenazas.
Policy and the Private Sector: Addressing the NSA Leaks

The document discusses policy changes being proposed in Congress in response to NSA surveillance leaks. It outlines two bills - the USA Freedom Act, which seeks to restrict NSA bulk data collection and increase transparency, and the FISA Improvement Act, which aims to codify NSA programs while enhancing oversight. The bills differ in their goals and key provisions, and also have varying prospects of passing based on support from lawmakers and tech companies.
CSGBM infomemo cbm 4-rig njwedit 131204

This document is an information memorandum for CSG Boremaster, a company raising up to $25 million in equity financing to exploit opportunities in drilling and production of coal bed methane and other unconventional oil and gas resources. The funds will be used to acquire CSG Exploration and Production, purchase drilling rigs and equipment, and fund operations. The memorandum provides an overview of the Asia Pacific rig market, coal bed methane as an opportunity, and risks associated with an investment in CSG Boremaster.
Implamasi Pancasila

Implementasi nilai-nilai Pancasila melalui pendidikan kewarganegaraan di Indonesia perlu direvisi karena saat ini kurikulum dan materi pembelajarannya kurang menarik sehingga makna Pancasila sulit ditangkap peserta didik. Pendidikan kewarganegaraan idealnya dapat membentuk karakter kebangsaan berdasarkan nilai-nilai Pancasila seperti ketuhanan, kemanusiaan, persatuan, dan keadilan sosial.
How to make the most out of hospital stay.

This document provides an overview and guidelines for the management of acute heart failure during hospitalization. It discusses evaluating the patient's volume status and filling pressures, starting intravenous diuretics and nitrates for initial stabilization, monitoring the patient daily and assessing response to treatment, identifying and treating the underlying cardiac cause, and ensuring proper long-term medication and management upon discharge to reduce risk of readmission. Rapid improvement in symptoms, filling pressures, and pulmonary congestion as estimated by combined echocardiography and lung ultrasound during the early treatment course can help determine treatment response and prognosis.
DECISION MAKING PRESENTATION | SYAFERI CENTER

How to make an decision , we would like to tell you all about that in here. Check this out
Recommended
Parenting & Education using mobile phone

We are no more in 1990s, many time-demanding day-to-day activities must go on mobile and that is why Edves Basic gives educators and parents access to teaching, learning and parenting children/students on mobile devices
C U R R I C U L U M V I T A E

Marwan Jaber al amin is a Lebanese citizen currently pursuing a Master's degree in accounting from the Lebanese University in Nabatieh. He received his Bachelor's degree in business administration from the same university, majoring in accounting, finance, law, management, marketing, and math/economics. His work experience includes positions as a salesman and trainee in accounting, banking, and retail. He is fluent in Arabic, French, and English and has advanced knowledge of accounting, office software, marketing, and management. His hobbies include soccer and swimming.
Tipos de virus y antivirus

El documento describe diferentes tipos de virus informáticos como Caballo de Troya, gusano o worm y spyware. Luego menciona algunos antivirus populares como Avast, diseñado por Alwil Software que es ampliamente usado en hogares y empresas, y Kaspersky que protege redes completas y detecta páginas web sospechosas e identifica nuevas amenazas.
Policy and the Private Sector: Addressing the NSA Leaks

The document discusses policy changes being proposed in Congress in response to NSA surveillance leaks. It outlines two bills - the USA Freedom Act, which seeks to restrict NSA bulk data collection and increase transparency, and the FISA Improvement Act, which aims to codify NSA programs while enhancing oversight. The bills differ in their goals and key provisions, and also have varying prospects of passing based on support from lawmakers and tech companies.
CSGBM infomemo cbm 4-rig njwedit 131204

This document is an information memorandum for CSG Boremaster, a company raising up to $25 million in equity financing to exploit opportunities in drilling and production of coal bed methane and other unconventional oil and gas resources. The funds will be used to acquire CSG Exploration and Production, purchase drilling rigs and equipment, and fund operations. The memorandum provides an overview of the Asia Pacific rig market, coal bed methane as an opportunity, and risks associated with an investment in CSG Boremaster.
Implamasi Pancasila

Implementasi nilai-nilai Pancasila melalui pendidikan kewarganegaraan di Indonesia perlu direvisi karena saat ini kurikulum dan materi pembelajarannya kurang menarik sehingga makna Pancasila sulit ditangkap peserta didik. Pendidikan kewarganegaraan idealnya dapat membentuk karakter kebangsaan berdasarkan nilai-nilai Pancasila seperti ketuhanan, kemanusiaan, persatuan, dan keadilan sosial.
How to make the most out of hospital stay.

This document provides an overview and guidelines for the management of acute heart failure during hospitalization. It discusses evaluating the patient's volume status and filling pressures, starting intravenous diuretics and nitrates for initial stabilization, monitoring the patient daily and assessing response to treatment, identifying and treating the underlying cardiac cause, and ensuring proper long-term medication and management upon discharge to reduce risk of readmission. Rapid improvement in symptoms, filling pressures, and pulmonary congestion as estimated by combined echocardiography and lung ultrasound during the early treatment course can help determine treatment response and prognosis.
DECISION MAKING PRESENTATION | SYAFERI CENTER

How to make an decision , we would like to tell you all about that in here. Check this out
RSTREET17

The document discusses how recent NSA surveillance program revelations have negatively impacted the technology industry and cloud computing. It summarizes that the NSA collected data from major tech companies without consent, details some of their surveillance programs, and reviews the legal and economic fallout, including two conflicting court rulings on the programs' constitutionality. Recent estimates suggest the NSA actions could cost the US tech industry between $35-180 billion over the next three years due to lost foreign business and erosion of trust in US cloud services.
Q&A about PRISM

This document is a Q&A about recent revelations of US government surveillance programs. It explains that the NSA has been collecting phone record metadata on millions of Americans under the Patriot Act since 2006 and information on foreigners from major tech companies through the PRISM program since 2007. These programs were authorized by secret courts but not revealed until leaks in 2013. While the government claims the goal is counterterrorism, critics argue it amounts to unprecedented domestic spying and the public deserves more transparency about surveillance of citizens.
Intelligence chief defends internet spying program

WASHINGTON (AP) — Eager to quell a domestic furor over U.S. spying, the nation’s top intelligence official stressed Saturday that a previously undisclosed program for tapping into Internet usage is authorized by Congress, falls under strict supervision of a secret court and cannot intentionally target a U.S. citizen. He decried the revelation of that and another intelligence-gathering program as reckless.
For the second time in three days, Director of National Intelligence James Clapper took the rare step of declassifying some details of an intelligence program to respond to media reports about counterterrorism techniques employed by the government.
‘‘Disclosing information about the specific methods the government uses to collect communications can obviously give our enemies a ‘playbook’ of how to avoid detection,’’ he said in a statement.
Foreign agency reportedly spied on US law firm with NSA's knowledge

It's the method to range from now on.The BasicsSite StatusAboutContactTip UsForumsJobsMobile SiteRol...
Krempley 1POL 300GoogleMulti-National Corporations, Inter.docx

Krempley 1
POL 300
Google/Multi-National Corporations, International Surveillance, and Human Rights
Abstract
The many news reports on cyber security, identity theft, Wikileaks, and NSA intelligence gathering programs over the past few years have shown the international community that the World Wide Web is anything but a safe place to store sensitive information, or any information for that matter. This study will examine how closely multi-national corporations in the information technology sector, such as Google, are involved with national governments on these issues. The study will analyze events in the U.S. and China and attempt to uncover whether or not these have directly infringed upon peoples’ basic human rights.
Question
With emerging information regarding the NSA's PRISM program and China's "Golden Shield Project", has either country directly infringed on peoples' basic human rights?
Hypothesis
As more information is uncovered regarding the true nature of the aims of these internationally implemented programs, it has become increasingly clear that there have been multiple violations of peoples' human rights in both the United States and China with their respective monitoring programs.
The NSA and the PRISM Project
"Since September 11th, 2001, the United States government has dramatically increased the ability of its intelligence agencies to collect and investigate information on both foreign subjects and US citizens. Some of these surveillance programs, including a secret program called PRISM, capture the private data of citizens who are not suspected of any connection to terrorism or any wrongdoing." (Sottek&Kopstein, 2013) Under the guise of a "war on terror", the United States government has consistently upped its efforts to gather as much information as possible regarding the activities of international and domestic citizens alike. Most U.S. citizens were wholly unaware that the government had been running a secret filtration program to determine threat levels of individual citizens both domestically and abroad. This PRISM project and its intentions have recently been leaked in the Edward Snowden fiasco that took the country and the media by storm.
"PRISM is a tool used by the US National Security Agency (NSA) to collect private electronic data belonging to users of major internet services like Gmail, Facebook, Outlook, and others. It’s the latest evolution of the US government’s post-9/11 electronic surveillance efforts, which began under President Bush with the Patriot Act, and expanded to include the Foreign Intelligence Surveillance Act (FISA) enacted in 2006 and 2007." (Sottek&Kopstein, 2013) FISA, "...may be the most powerful court you have never heard of -- operating out of a bunker-like complex blocks from the Capitol and the White House -- sealed tightly to prevent eavesdropping.The FISA Court's larger mission is to decide whether to grant certain types of government requests-- wiretapping, data anal ...
Case 9 Security vs Privacy

The document discusses various revelations about NSA surveillance programs from documents leaked by Edward Snowden. It describes how the NSA collects vast amounts of metadata from telecommunications companies like Verizon on all Americans. It also discusses the PRISM program through which the NSA gains access to data from major tech companies. The document outlines the Boundless Informant tool used by the NSA to track global surveillance and maps which countries have the most metadata collected. It discusses the debate around whether Snowden should be considered a whistleblower or leaker and the espionage charges filed against him.
House rejects nsa spying restrictions after white house outcry

The US House of Representatives voted on Wednesday to reject an attempt to reign in domestic spying by the National Security Agency following a storm of lobbying by the White House against the measure.
In a 205-217 vote the House defeated an amendment introduced by Rep. Justin Amash (R-Michigan) which would have prevented the NSA from collecting the phone data of individuals not currently under investigation.
Katalin jakucs - crisis communication and the snowden affair

The document summarizes the Edward Snowden revelations about NSA surveillance programs and the resulting crisis in EU-US relations. It describes how the initial revelations raised concerns in Europe about privacy violations. While President Obama initially acknowledged European concerns and promised action, further reports that the NSA had bugged EU offices and monitored half a billion German communications monthly outraged European officials. The crisis exposed differing views between the US (seeing surveillance as normal intelligence work) and Europe (believing security should not compromise privacy). Obama agreed to a joint investigation, but trust between the allies was damaged.
Edward J. Snowden, the thirty-year-old former National Security Agen.docx

Edward J. Snowden, the thirty-year-old former National Security Agency contractor who handed over a treasure trove of classified documents about U.S. government surveillance to the Washington Post and Britain's Guardian, is a hero to some and a traitor to others. He claims to have acted out of a sense of outrage over the NSA's indiscriminate collection of the phone and internet records of Americans, decrying the danger such intrusive government oversight poses to democracy and privacy. Snowden subsequently fled to Hong Kong, and from there to Moscow. His eventual destination appears to be Ecuador, Cuba, or Venezuela.
Snowden's efforts to elude U.S. authorities cast an ambiguous light on his motives; the countries where he has sought refuge are not known for upholding the sort of democratic values he claims to be defending. While demanding accountability from the U.S. government, he appears to be seeking immunity for his own actions. Snowden's purposes and fate, however, should be of secondary concern. However misguided his actions may have been, they have reopened a much-needed debate about the reach and authority of what is often called the National Security State. While defending the NSA programs, even President Barack Obama seems to welcome that debate. "You can't have 100 percent security and also then have 100 percent privacy and zero inconvenience," Obama noted when asked about Snowden's leaks. "We're going to have to make some choices as a society. ... There are trade-offs involved."
Administration officials and members of Congress say the government's extensive surveillance programs are crucial to preventing terrorist attacks, and that Snowden has done real damage to efforts to keep Americans safe. Because almost all the relevant information remains classified, it is difficult to assess that claim. NSA officials have now promised to make public details of some of the dozens of terrorist plots they say the massive data-collection effort, called Prism, has helped thwart. That sort of disclosure is long overdue. Although Prism was approved by the Foreign Intelligence Surveillance Act court and is monitored by the intelligence committees of Congress, many Americans were shocked to learn that the government now stores their phone and internet records for possible use in future investigations. While the government is prohibited from listening to the tracked calls, it uses sophisticated algorithms to trace calling patterns. If a series of related calls seems suspicious, the NSA or FBI then gets a warrant from the FISA court to investigate further. No abuse of those procedures has come to light. Still, the mere existence of such records in the government's hands, information that might easily be exploited for political purposes, should concern every American.
It is axiomatic that fighting clandestine terrorist groups requires clandestine methods. Sources and allies must be protected; in preemptive actions the element of surprise must be prese.
Argument for Snowden Clemency

Paper written to present a case for Edward Snowden's clemency, an assignment completed for a Business Ethics course.
Edward Snowden Data-Breach

Edward Snowden : is a former National Security Agency subcontractor who made headlines in 2013 when he leaked top secret information about NSA surveillance activities.
Thanks to William Favre.
Reply to below posting in a paragraph of at least five sentences by.docx

Reply to below posting in a paragraph of at least five sentences by asking questions, reflecting on your own experience, challenging assumptions, pointing out something new you learned, offering suggestions.
1)
Edward Snowden is a hero or a criminal
Edward Snowden, a low-level private contractor to the US-based National Security Agency (NSA), breached moral confidentiality and secrecy obligations by engaging in unauthorized accessing, retrieving and/or releasing of a large volume of confidential data from NSA to the press and, possibly, to foreign powers. Edward Snowden (born June 21, 1983) is a computer programmer who worked as a subcontractor for the National Security Agency (NSA). Snowden collected top-secret documents regarding NSA domestic surveillance practices that he found disturbing and leaked them. During his years of IT work, Snowden had noticed the far reach of the NSA's everyday surveillance.
“While working for Booz Allen, Snowden began copying top-secret NSA documents.”
(Biography.com, 2019) After he had compiled a large store of documents, Snowden told his NSA supervisor that he needed a leave of absence for medical reasons, stating he had been diagnosed with epilepsy. On May 20, 2013, Snowden took a flight to Hong Kong, China. (Biography.com, 2019)
As mentioned by author Rouse in her article referring, he leaked and also raised questions about data sovereignty and how secure a company's data really is if it's stored by a cloud provider based in the United States. In 2014, almost 90% of respondents to a survey commissioned by security consultancy NTT Communications said they were changing their cloud-buying behavior as a result of Snowden’s revelations. Just over half said they are carrying out greater due diligence on cloud providers than ever before, and more than four-fifths responded that they would seek out more training on data protection laws. (Rouse, 2015)
Snowden has also been accused of irregularities under the Espionage Law for knowingly discovering mysterious national security data. When these charges were opened, newspapers quickly guaranteed that he was accused of undercover work. Such cases are not exactly accurate. Undercover work is commonly characterized as
"the act of spying ... to acquire data on plans and exercises, particularly from an external government."
(Richa, (2015) Although there have been hypotheses as to whether the nations to which Snowden fled (Russia and China) have kept their records, there is still no evidence that he has continued to his advantage or helped them easily as would be the case. The situation with great recognition. (Richa, (2015)
Contrary to Snowden’s claim about wanting to stand up for his fellow Americans, the information he leaked actually created more harm than good.
“The majority of the information that he shared is about the U.S. spying on foreign nations and not its domestic operations.”
(Rachel Segal, 2019) As such, he risked damaging America’s relatio.
Anger swells after NSA phone records collection revelations

The scale of America's surveillance state was laid bare on Thursday as senior politicians revealed that the US counter-terrorism effort had swept up swaths of personal data from the phone calls of millions of citizens for years.
After the revelation by the Guardian of a sweeping secret court order that authorised the FBI to seize all call records from a subsidiary of Verizon, the Obama administration sought to defuse mounting anger over what critics described as the broadest surveillance ruling ever issued.
Article research one edward snowdon

This document summarizes Edward Snowden's leaks revealing the NSA's mass surveillance programs and various reactions to the leaks. It discusses Snowden's intentions to expose NSA surveillance and reactions from politicians like David Cameron, Barack Obama, and Angela Merkel who were initially against the surveillance but some like Obama later supported Snowden. It also mentions those in support of NSA surveillance like Dianne Feinstein who argue it does not collect private communication content. The document provides context on NSA programs like PRISM that collect data from tech companies and justification that access to large data is needed to detect threats.
Prism

PRISM is a secret NSA program that collects intelligence from major tech companies like Google and Facebook. It allows analysts access to emails, chats, photos, and other data from foreigners using these services. While the NSA claims PRISM only targets non-US persons abroad, it may also incidentally collect some data on Americans due to large amounts of foreign data being routed through US servers. The program is conducted under Section 702 of the FISA Amendments Act but was leaked to the public by Edward Snowden.
Snowden -Hero OR Traitor

Edward Snowden revealed classified details of extensive US government surveillance programs to the media in 2013. He is currently living in temporary asylum in Russia after being charged with theft and unauthorized communication of national defense information by the US. Snowden believes he acted correctly to inform the public about surveillance that collected data on innocent people without their knowledge. However, others argue he sabotaged legal government programs and endangered national security. Public opinion polls at the time showed Americans were divided on whether Snowden was a hero or traitor for his actions.
Data localization vs global internet

Data localization requirements are on the rise around the world as governments seek to limit the flow of data across national borders. The document analyzes data localization measures in 16 countries and the European Union. It finds that countries are implementing a wide variety of measures from explicit requirements to store data locally to indirect measures like requiring consent for cross-border data transfers. The measures are driven by concerns over foreign surveillance, privacy, security and law enforcement. However, the document argues that data localization is likely to backfire and undermine rather than enhance these goals.
Lawmakers say Obama surveillance idea won't work

Lawmakers say Obama surveillance idea won't workA chief element of President Barack Obama's attempt ...
Lawmakers say Obama surveillance idea won't work

Lawmakers say Obama surveillance idea won't workA chief element of President Barack Obama's attempt ...
Icreach — nsa's secret google like search engine for metadata analysis

NSA, GCHQ, Five, Nine, Fourteen Eyes Alliances use Major Search engines Backdoor Access to collect, store and resell internet users information. Global internet users metadata is now "worth billion's of dollars world wide"
Congressional Gridlock Analysis

Graphs and charts analyzing low legislative productivity in Congress as well as trends in partisanship and ideological gaps among Congressional leaders
Long-Term Unemployment

The document is a chart showing the average yearly share of unemployed individuals in the United States broken down by the length of their unemployment from 2007 to 2012. It shows that the percentage of individuals unemployed for 27 weeks or more (long-term unemployed) has sharply increased since 2007, while the percentages of those unemployed for shorter durations have decreased. The source is labor statistics from the U.S. Bureau of Labor Statistics and an article from the National Journal.
More Related Content
Similar to Timeline of National Security Agency Leaks
RSTREET17

The document discusses how recent NSA surveillance program revelations have negatively impacted the technology industry and cloud computing. It summarizes that the NSA collected data from major tech companies without consent, details some of their surveillance programs, and reviews the legal and economic fallout, including two conflicting court rulings on the programs' constitutionality. Recent estimates suggest the NSA actions could cost the US tech industry between $35-180 billion over the next three years due to lost foreign business and erosion of trust in US cloud services.
Q&A about PRISM

This document is a Q&A about recent revelations of US government surveillance programs. It explains that the NSA has been collecting phone record metadata on millions of Americans under the Patriot Act since 2006 and information on foreigners from major tech companies through the PRISM program since 2007. These programs were authorized by secret courts but not revealed until leaks in 2013. While the government claims the goal is counterterrorism, critics argue it amounts to unprecedented domestic spying and the public deserves more transparency about surveillance of citizens.
Intelligence chief defends internet spying program

WASHINGTON (AP) — Eager to quell a domestic furor over U.S. spying, the nation’s top intelligence official stressed Saturday that a previously undisclosed program for tapping into Internet usage is authorized by Congress, falls under strict supervision of a secret court and cannot intentionally target a U.S. citizen. He decried the revelation of that and another intelligence-gathering program as reckless.
For the second time in three days, Director of National Intelligence James Clapper took the rare step of declassifying some details of an intelligence program to respond to media reports about counterterrorism techniques employed by the government.
‘‘Disclosing information about the specific methods the government uses to collect communications can obviously give our enemies a ‘playbook’ of how to avoid detection,’’ he said in a statement.
Foreign agency reportedly spied on US law firm with NSA's knowledge

It's the method to range from now on.The BasicsSite StatusAboutContactTip UsForumsJobsMobile SiteRol...
Krempley 1POL 300GoogleMulti-National Corporations, Inter.docx

Krempley 1
POL 300
Google/Multi-National Corporations, International Surveillance, and Human Rights
Abstract
The many news reports on cyber security, identity theft, Wikileaks, and NSA intelligence gathering programs over the past few years have shown the international community that the World Wide Web is anything but a safe place to store sensitive information, or any information for that matter. This study will examine how closely multi-national corporations in the information technology sector, such as Google, are involved with national governments on these issues. The study will analyze events in the U.S. and China and attempt to uncover whether or not these have directly infringed upon peoples’ basic human rights.
Question
With emerging information regarding the NSA's PRISM program and China's "Golden Shield Project", has either country directly infringed on peoples' basic human rights?
Hypothesis
As more information is uncovered regarding the true nature of the aims of these internationally implemented programs, it has become increasingly clear that there have been multiple violations of peoples' human rights in both the United States and China with their respective monitoring programs.
The NSA and the PRISM Project
"Since September 11th, 2001, the United States government has dramatically increased the ability of its intelligence agencies to collect and investigate information on both foreign subjects and US citizens. Some of these surveillance programs, including a secret program called PRISM, capture the private data of citizens who are not suspected of any connection to terrorism or any wrongdoing." (Sottek&Kopstein, 2013) Under the guise of a "war on terror", the United States government has consistently upped its efforts to gather as much information as possible regarding the activities of international and domestic citizens alike. Most U.S. citizens were wholly unaware that the government had been running a secret filtration program to determine threat levels of individual citizens both domestically and abroad. This PRISM project and its intentions have recently been leaked in the Edward Snowden fiasco that took the country and the media by storm.
"PRISM is a tool used by the US National Security Agency (NSA) to collect private electronic data belonging to users of major internet services like Gmail, Facebook, Outlook, and others. It’s the latest evolution of the US government’s post-9/11 electronic surveillance efforts, which began under President Bush with the Patriot Act, and expanded to include the Foreign Intelligence Surveillance Act (FISA) enacted in 2006 and 2007." (Sottek&Kopstein, 2013) FISA, "...may be the most powerful court you have never heard of -- operating out of a bunker-like complex blocks from the Capitol and the White House -- sealed tightly to prevent eavesdropping.The FISA Court's larger mission is to decide whether to grant certain types of government requests-- wiretapping, data anal ...
Case 9 Security vs Privacy

The document discusses various revelations about NSA surveillance programs from documents leaked by Edward Snowden. It describes how the NSA collects vast amounts of metadata from telecommunications companies like Verizon on all Americans. It also discusses the PRISM program through which the NSA gains access to data from major tech companies. The document outlines the Boundless Informant tool used by the NSA to track global surveillance and maps which countries have the most metadata collected. It discusses the debate around whether Snowden should be considered a whistleblower or leaker and the espionage charges filed against him.
House rejects nsa spying restrictions after white house outcry

The US House of Representatives voted on Wednesday to reject an attempt to reign in domestic spying by the National Security Agency following a storm of lobbying by the White House against the measure.
In a 205-217 vote the House defeated an amendment introduced by Rep. Justin Amash (R-Michigan) which would have prevented the NSA from collecting the phone data of individuals not currently under investigation.
Katalin jakucs - crisis communication and the snowden affair

The document summarizes the Edward Snowden revelations about NSA surveillance programs and the resulting crisis in EU-US relations. It describes how the initial revelations raised concerns in Europe about privacy violations. While President Obama initially acknowledged European concerns and promised action, further reports that the NSA had bugged EU offices and monitored half a billion German communications monthly outraged European officials. The crisis exposed differing views between the US (seeing surveillance as normal intelligence work) and Europe (believing security should not compromise privacy). Obama agreed to a joint investigation, but trust between the allies was damaged.
Edward J. Snowden, the thirty-year-old former National Security Agen.docx

Edward J. Snowden, the thirty-year-old former National Security Agency contractor who handed over a treasure trove of classified documents about U.S. government surveillance to the Washington Post and Britain's Guardian, is a hero to some and a traitor to others. He claims to have acted out of a sense of outrage over the NSA's indiscriminate collection of the phone and internet records of Americans, decrying the danger such intrusive government oversight poses to democracy and privacy. Snowden subsequently fled to Hong Kong, and from there to Moscow. His eventual destination appears to be Ecuador, Cuba, or Venezuela.
Snowden's efforts to elude U.S. authorities cast an ambiguous light on his motives; the countries where he has sought refuge are not known for upholding the sort of democratic values he claims to be defending. While demanding accountability from the U.S. government, he appears to be seeking immunity for his own actions. Snowden's purposes and fate, however, should be of secondary concern. However misguided his actions may have been, they have reopened a much-needed debate about the reach and authority of what is often called the National Security State. While defending the NSA programs, even President Barack Obama seems to welcome that debate. "You can't have 100 percent security and also then have 100 percent privacy and zero inconvenience," Obama noted when asked about Snowden's leaks. "We're going to have to make some choices as a society. ... There are trade-offs involved."
Administration officials and members of Congress say the government's extensive surveillance programs are crucial to preventing terrorist attacks, and that Snowden has done real damage to efforts to keep Americans safe. Because almost all the relevant information remains classified, it is difficult to assess that claim. NSA officials have now promised to make public details of some of the dozens of terrorist plots they say the massive data-collection effort, called Prism, has helped thwart. That sort of disclosure is long overdue. Although Prism was approved by the Foreign Intelligence Surveillance Act court and is monitored by the intelligence committees of Congress, many Americans were shocked to learn that the government now stores their phone and internet records for possible use in future investigations. While the government is prohibited from listening to the tracked calls, it uses sophisticated algorithms to trace calling patterns. If a series of related calls seems suspicious, the NSA or FBI then gets a warrant from the FISA court to investigate further. No abuse of those procedures has come to light. Still, the mere existence of such records in the government's hands, information that might easily be exploited for political purposes, should concern every American.
It is axiomatic that fighting clandestine terrorist groups requires clandestine methods. Sources and allies must be protected; in preemptive actions the element of surprise must be prese.
Argument for Snowden Clemency

Paper written to present a case for Edward Snowden's clemency, an assignment completed for a Business Ethics course.
Edward Snowden Data-Breach

Edward Snowden : is a former National Security Agency subcontractor who made headlines in 2013 when he leaked top secret information about NSA surveillance activities.
Thanks to William Favre.
Reply to below posting in a paragraph of at least five sentences by.docx

Reply to below posting in a paragraph of at least five sentences by asking questions, reflecting on your own experience, challenging assumptions, pointing out something new you learned, offering suggestions.
1)
Edward Snowden is a hero or a criminal
Edward Snowden, a low-level private contractor to the US-based National Security Agency (NSA), breached moral confidentiality and secrecy obligations by engaging in unauthorized accessing, retrieving and/or releasing of a large volume of confidential data from NSA to the press and, possibly, to foreign powers. Edward Snowden (born June 21, 1983) is a computer programmer who worked as a subcontractor for the National Security Agency (NSA). Snowden collected top-secret documents regarding NSA domestic surveillance practices that he found disturbing and leaked them. During his years of IT work, Snowden had noticed the far reach of the NSA's everyday surveillance.
“While working for Booz Allen, Snowden began copying top-secret NSA documents.”
(Biography.com, 2019) After he had compiled a large store of documents, Snowden told his NSA supervisor that he needed a leave of absence for medical reasons, stating he had been diagnosed with epilepsy. On May 20, 2013, Snowden took a flight to Hong Kong, China. (Biography.com, 2019)
As mentioned by author Rouse in her article referring, he leaked and also raised questions about data sovereignty and how secure a company's data really is if it's stored by a cloud provider based in the United States. In 2014, almost 90% of respondents to a survey commissioned by security consultancy NTT Communications said they were changing their cloud-buying behavior as a result of Snowden’s revelations. Just over half said they are carrying out greater due diligence on cloud providers than ever before, and more than four-fifths responded that they would seek out more training on data protection laws. (Rouse, 2015)
Snowden has also been accused of irregularities under the Espionage Law for knowingly discovering mysterious national security data. When these charges were opened, newspapers quickly guaranteed that he was accused of undercover work. Such cases are not exactly accurate. Undercover work is commonly characterized as
"the act of spying ... to acquire data on plans and exercises, particularly from an external government."
(Richa, (2015) Although there have been hypotheses as to whether the nations to which Snowden fled (Russia and China) have kept their records, there is still no evidence that he has continued to his advantage or helped them easily as would be the case. The situation with great recognition. (Richa, (2015)
Contrary to Snowden’s claim about wanting to stand up for his fellow Americans, the information he leaked actually created more harm than good.
“The majority of the information that he shared is about the U.S. spying on foreign nations and not its domestic operations.”
(Rachel Segal, 2019) As such, he risked damaging America’s relatio.
Anger swells after NSA phone records collection revelations

The scale of America's surveillance state was laid bare on Thursday as senior politicians revealed that the US counter-terrorism effort had swept up swaths of personal data from the phone calls of millions of citizens for years.
After the revelation by the Guardian of a sweeping secret court order that authorised the FBI to seize all call records from a subsidiary of Verizon, the Obama administration sought to defuse mounting anger over what critics described as the broadest surveillance ruling ever issued.
Article research one edward snowdon

This document summarizes Edward Snowden's leaks revealing the NSA's mass surveillance programs and various reactions to the leaks. It discusses Snowden's intentions to expose NSA surveillance and reactions from politicians like David Cameron, Barack Obama, and Angela Merkel who were initially against the surveillance but some like Obama later supported Snowden. It also mentions those in support of NSA surveillance like Dianne Feinstein who argue it does not collect private communication content. The document provides context on NSA programs like PRISM that collect data from tech companies and justification that access to large data is needed to detect threats.
Prism

PRISM is a secret NSA program that collects intelligence from major tech companies like Google and Facebook. It allows analysts access to emails, chats, photos, and other data from foreigners using these services. While the NSA claims PRISM only targets non-US persons abroad, it may also incidentally collect some data on Americans due to large amounts of foreign data being routed through US servers. The program is conducted under Section 702 of the FISA Amendments Act but was leaked to the public by Edward Snowden.
Snowden -Hero OR Traitor

Edward Snowden revealed classified details of extensive US government surveillance programs to the media in 2013. He is currently living in temporary asylum in Russia after being charged with theft and unauthorized communication of national defense information by the US. Snowden believes he acted correctly to inform the public about surveillance that collected data on innocent people without their knowledge. However, others argue he sabotaged legal government programs and endangered national security. Public opinion polls at the time showed Americans were divided on whether Snowden was a hero or traitor for his actions.
Data localization vs global internet

Data localization requirements are on the rise around the world as governments seek to limit the flow of data across national borders. The document analyzes data localization measures in 16 countries and the European Union. It finds that countries are implementing a wide variety of measures from explicit requirements to store data locally to indirect measures like requiring consent for cross-border data transfers. The measures are driven by concerns over foreign surveillance, privacy, security and law enforcement. However, the document argues that data localization is likely to backfire and undermine rather than enhance these goals.
Lawmakers say Obama surveillance idea won't work

Lawmakers say Obama surveillance idea won't workA chief element of President Barack Obama's attempt ...
Lawmakers say Obama surveillance idea won't work

Lawmakers say Obama surveillance idea won't workA chief element of President Barack Obama's attempt ...
Icreach — nsa's secret google like search engine for metadata analysis

NSA, GCHQ, Five, Nine, Fourteen Eyes Alliances use Major Search engines Backdoor Access to collect, store and resell internet users information. Global internet users metadata is now "worth billion's of dollars world wide"
Similar to Timeline of National Security Agency Leaks (20)
Intelligence chief defends internet spying program

Intelligence chief defends internet spying program
Foreign agency reportedly spied on US law firm with NSA's knowledge

Foreign agency reportedly spied on US law firm with NSA's knowledge
Krempley 1POL 300GoogleMulti-National Corporations, Inter.docx

Krempley 1POL 300GoogleMulti-National Corporations, Inter.docx
House rejects nsa spying restrictions after white house outcry

House rejects nsa spying restrictions after white house outcry
Katalin jakucs - crisis communication and the snowden affair

Katalin jakucs - crisis communication and the snowden affair
Edward J. Snowden, the thirty-year-old former National Security Agen.docx

Edward J. Snowden, the thirty-year-old former National Security Agen.docx
Reply to below posting in a paragraph of at least five sentences by.docx

Reply to below posting in a paragraph of at least five sentences by.docx
Anger swells after NSA phone records collection revelations

Anger swells after NSA phone records collection revelations
Icreach — nsa's secret google like search engine for metadata analysis

Icreach — nsa's secret google like search engine for metadata analysis
More from National Journal Membership
Congressional Gridlock Analysis

Graphs and charts analyzing low legislative productivity in Congress as well as trends in partisanship and ideological gaps among Congressional leaders
Long-Term Unemployment

The document is a chart showing the average yearly share of unemployed individuals in the United States broken down by the length of their unemployment from 2007 to 2012. It shows that the percentage of individuals unemployed for 27 weeks or more (long-term unemployed) has sharply increased since 2007, while the percentages of those unemployed for shorter durations have decreased. The source is labor statistics from the U.S. Bureau of Labor Statistics and an article from the National Journal.
Immigration Reform Primer

Charts and analysis on the growing minority population, its voting power, and the renewed push for immigration reform
What to Expect in Obama's Second Term

The document discusses President Obama's positions on key issues during his reelection campaign and what actions he may take on those issues during his second term, as well as potential obstacles. It analyzes Obama's stances on the economy, health care reform, energy and climate change, immigration reform, and national security based on his campaign materials and interviews with experts from the National Journal.
Debt and the Debt Ceiling Crisis

A primer on national debt and the debt ceiling with a focus on the 2011 debt ceiling crisis and the Budget Control Act as well as an analysis of scenarios for debt reduction in 2013
Sequestration Update

The document discusses sequestration, which mandates automatic spending cuts to reduce the federal deficit. It notes that sequestration was originally set to begin on January 2nd, 2013 but the American Taxpayer Relief Act of 2012 delayed it until March 1st, 2013. This Act also reduced the total spending cuts for 2013 from $109 billion under the original law to $85 billion. The document provides pros and cons of sequestration and shows how different areas of the budget would be impacted by the reduced cuts compared to the original levels.
The Budget Deficit

A primer on the U.S. federal budget deficit, including an examination of political policies and economic factors adding to the deficit and a look at future deficit projections
More from National Journal Membership (7)
Recently uploaded
Letter-from-ECI-to-MeiTY-21st-march-2024.pdf

भारत सरकार द्वारा बड़े पैमाने पर व्हाट्सएप अभियान चलाए जाने से डेटा गोपनीयता, नैतिकता और चुनावों की निष्पक्षता पर सवाल उठते हैं।
Acolyte Episodes review (TV series)..pdf

Acolyte Episodes review (TV series) The Acolyte. Learn about the influence of the program on the Star Wars world, as well as new characters and story twists.
EED - The Container Port PERFORMANCE INDEX 2023

El Puerto de Algeciras continúa un año más como el más eficiente del continente europeo y vuelve a situarse en el “top ten” mundial, según el informe The Container Port Performance Index 2023 (CPPI), elaborado por el Banco Mundial y la consultora S&P Global.
El informe CPPI utiliza dos enfoques metodológicos diferentes para calcular la clasificación del índice: uno administrativo o técnico y otro estadístico, basado en análisis factorial (FA). Según los autores, esta dualidad pretende asegurar una clasificación que refleje con precisión el rendimiento real del puerto, a la vez que sea estadísticamente sólida. En esta edición del informe CPPI 2023, se han empleado los mismos enfoques metodológicos y se ha aplicado un método de agregación de clasificaciones para combinar los resultados de ambos enfoques y obtener una clasificación agregada.
Essential Tools for Modern PR Business .pptx

Discover the essential tools and strategies for modern PR business success. Learn how to craft compelling news releases, leverage press release sites and news wires, stay updated with PR news, and integrate effective PR practices to enhance your brand's visibility and credibility. Elevate your PR efforts with our comprehensive guide.
What Ukraine Has Lost During Russia’s Invasion

An astonishing, first-of-its-kind, report by the NYT assessing damage in Ukraine. Even if the war ends tomorrow, in many places there will be nothing to go back to.
Gabriel Whitley's Motion Summary Judgment

Here is Gabe Whitley's response to my defamation lawsuit for him calling me a rapist and perjurer in court documents.
You have to read it to believe it, but after you read it, you won't believe it. And I included eight examples of defamatory statements/
04062024_First India Newspaper Jaipur.pdf

Find Latest India News and Breaking News these days from India on Politics, Business, Entertainment, Technology, Sports, Lifestyle and Coronavirus News in India and the world over that you can't miss. For real time update Visit our social media handle. Read First India NewsPaper in your morning replace. Visit First India.
CLICK:- https://firstindia.co.in/
#First_India_NewsPaper
Recently uploaded (10)
Timeline of National Security Agency Leaks
- 1. Stream of NSA Leaks Puts Administration in Hot Water Sources: Matthew Cooper and Garance Franke-Ruta, “Breathe, People: We Shouldn’t Rush to Judgment About Edward Snowden,” National Journal, June 11, 2013; Dan Roberts, Spencer Ackerman, and Tania Branigan, “Edward Snowden’s explosive NSA leaks have US in damage control mode,” The Guardian, June 10, 2013; Glenn Greenwald and Ewen MacAskill, “NSA Prism program taps in to user data of Apple, Google and others,” The Guardian, June 6, 2013; Dan Roberts and Spencer Ackermann, “Obama defiant over NSA revelations ahead of summit with Chinese premier,” The Guardian, June 7, 2013; Nicholas Watt, “Prism scandal: European commission to seek privacy guarantees from US,” The Guardian, June 10, 2013. Updated June 12, 2013 Timeline of Events Leading to NSA Leaks 2008 2012 March 2013 June 5, 2013 June 6, 2013 June 7, 2013 June 9, 2013 June 10, 2013 Foreign Intelligence Surveillance Act amended National Security Agency (NSA) no longer needs probable cause to intercept phone calls, text messages, or e-mails within U.S. as long as one party to communications is reasonably believed to be outside the U.S. Senators express frustration over lack of surveillance data Senators Ron Wyden (D-Ore.) and Mark Udall (D-Colo.) write to NSA expressing frustration with the agency’s refusal to estimate the scale of its collection of American communications Prism program leaked Leak of NSA presentation on Prism program, which allows agency to obtain targeted communications from Internet service providers without having to request them from service providers or obtain court orders; several senior tech executives deny having heard of the program Director of National Intelligence denies data collection During a Senate Intelligence Cmte. hearing, Director of National Intelligence James Clapper denies collecting any type of data at all on millions of Americans Verizon court- order leaked Leak of top-secret court order compelling Verizon to turn over telephone metadata records of million of U.S. customers to NSA Obama defends surveillance programs President Obama insists U.S. surveillance operations have full congressional approval and strike a balance between privacy and national security Snowden interview leaked The Guardian releases Edward Snowden’s interview and related top-secret documents are declassified; some show that NSA breaks down surveillance data in a way that could allow the agency to quantify American communications European Commission raises concerns with U.S. data monitoring European Commission raises concerns directly with U.S. administration about threats to EU citizens’ privacy from the sort of data monitoring highlighted in NSA leaks
