The document provides an overview of cloud storage, describing it as an online service for hosting and accessing files from various devices over the internet. It discusses the benefits of using the cloud, including data backup, accessibility, and file sharing, while cautioning against storing personal information due to security concerns. Additionally, it outlines steps for creating accounts with services like 4shared and managing multiple cloud accounts through Zeropc.


!["The Cloud" also serves as a backup device.
This is also a good way to backup an existing
tablet, netbook, laptop, etc.
Other benefits include the ability to "share"
files or folders with others. This may be used to
collaborate on a project; swap family photos;
disseminate information to a class or board
members.
As a side note: I wouldn't advise placing
personal information into "The Cloud" for
securuty reasons and peace of mind.
While on the topic of security, these services
offer solid security as is. You must first create an
account by registering at the site and
establishing a USERNAME and PASSWORD.
This is key if you wish to gain access to your
information.
Since many companies are now offering
"cloud" services, they understand that security,
accessability, continuous backups are critical to
mainstream users. For those who desire
additional features [for a fee], there is also tech For more information on how to create a solid password,
support, greater storage capacity, and in some please read this NY Times article:
cases, the ability to manage multiple storage
accounts. http://www.nytimes.com/2012/11/08/technology/personalt
ech/howtodevisepasswordsthatdrivehackers
away.html?smid=lishare
Issue 1 Page 3](https://image.slidesharecdn.com/thecloud-1-121116210500-phpapp02/85/The-Cloud-2012-3-320.jpg)






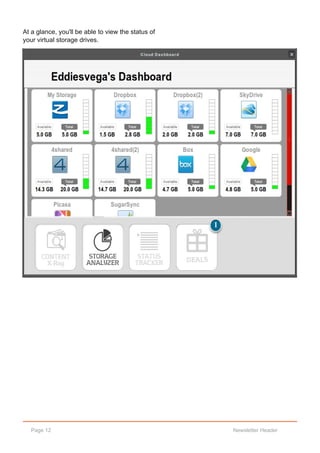
![How do you manage multiple
accounts?
If you're like me, who has multiple online
storage accounts and do not enjoy having to
login into every account to see where things are
located, then try ZeroPC [www.zeropc.com].
The user interface allows you to easily access
your accounts all at once. All this for FREE.
There is also a subscription option to ZeroPC,
where you can then add additional accounts to
your online storage arsenal, which in turn would
significantly increase your storage size
capabilities. I use the subscription version which
allows me to add additional Dropbox and
4Shared accounts. This interface can also be
accessed from your desktop, laptop, notebook or
netbook, and tablet.
Note: I have not tried a SmartPhone yet.
Page 10 Newsletter Header](https://image.slidesharecdn.com/thecloud-1-121116210500-phpapp02/85/The-Cloud-2012-10-320.jpg)