Stop Ransomware
•Download as PPTX, PDF•
0 likes•35 views
Real world case study clearly demonstrating protection against ransomware
Report
Share
Report
Share
Recommended
Application Security - 28 Nov 2018

Share about Azure Secure DevOps Kit and Azure Security Center.
.Net UG Singapore
Mistral and StackStorm

Dmitri Zimine's slides on Design Summit at OpenStack Barcelona 2016. Talked about the history of two projects, technical differences, discussed an overlap and drafted a path forward.
https://www.openstack.org/summit/barcelona-2016/summit-schedule/events/16999/mistral-mistral-and-stackstorm
TLS 1.3 and Other New Features in NGINX Plus R17 and NGINX Open Source

The latest version of the TLS protocol, TLS 1.3, was just released in August 2018. TLS 1.3 is faster and more secure than TLS 1.2. In this webinar, we cover what’s new in TLS 1.3 and how to use it with NGINX, plus other new features in NGINX Open Source and NGINX Plus.
Join this webinar to learn:
- What’s new in TLS 1.3 and why it's faster and more secure than TLS 1.2
- How to use TLS 1.3 with NGINX Plus and NGINX Open Source
- About two-stage rate limiting, simplified OpenID Connect, and 2x faster NGINX and ModSecurity WAF performance
- More with a live demo of TLS 1.3 in action
Watch On-demand: https://www.nginx.com/resources/webinars/tls-1-3-new-features-nginx-plus-r17-nginx-open-source/
An Introduction to WSO2 Microservices Framework for Java

any organizations today are leveraging microservices architecture (MSA) which is becoming increasingly popular because of its many potential advantages. This webinar introduces WSO2 Microservices Framework for Java (MSF4J), which provides the necessary framework and tooling to build an MSA solution.
During this webinar, Sagara will
Introduce WSO2 MSF4J programming model and deployment options
Discuss the key strengths and performance measures of WSO2 MSF4J over other frameworks
Demonstrate security, analytics and service discovery
Highlight tooling, Swagger support and its seamless integration with rest of the platform
Digital Forensics and Incident Response in The Cloud

TUTORIAL: Digital Forensics and Incident Response in the Cloud
Cloud technologies have made it easier for organizations to adapt rapidly to changing IT needs. Teams may acquire (and destroy) new computing resources at a press of a button providing for very flexible deployment environment. While this capability is generally useful, it does come at the cost of increasing management overheads and particularly degraded security posture. Traditionally, IT managers have provided visibility into organizational inventories and could use this information to enforce org wide standard operating environments (SOEs), institute patching regimes etc. However, with the advent of cloud computing, every team can create new VMs and containers on a whim for both production and development use, typically consisting of the cloud service provider's SOE offering.
In this tutorial we explore open source tools available for managing cloud deployments. In particular we look at the endpoint monitoring solutions provided by Google's Rekall Agent and Facebook's OSQuery and how these can be integrated into typical cloud deployments. Delegates should be able to walk away from this tutorial being able to install and manage a cloud deployment of Rekall Agent and OSQuery on their VM endpoints.
These solutions allow the administrators to gain insight into their enterprise wide deployment. For example, one could ask questions such as:
What is the current patch level of all my cloud VM's and containers for each software package? Which VM's are in need of patching? Which VMs have been created recently, and do they comply with minimum security hardening standards?
Who has remote access to my VM's? E.g. via ssh authorized_keys? Via cloud IAM's security policy?
Do any VM's contain a particular indicator of compromise? E.g. Run a YARA signature over all executables on my virtual machines and tell me which ones match.
Digital Forensics and Incident Response in The Cloud

TUTORIAL: Digital Forensics and Incident Response in the Cloud
Cloud technologies have made it easier for organizations to adapt rapidly to changing IT needs. Teams may acquire (and destroy) new computing resources at a press of a button providing for very flexible deployment environment. While this capability is generally useful, it does come at the cost of increasing management overheads and particularly degraded security posture. Traditionally, IT managers have provided visibility into organizational inventories and could use this information to enforce org wide standard operating environments (SOEs), institute patching regimes etc. However, with the advent of cloud computing, every team can create new VMs and containers on a whim for both production and development use, typically consisting of the cloud service provider's SOE offering.
In this tutorial we explore open source tools available for managing cloud deployments. In particular we look at the endpoint monitoring solutions provided by Google's Rekall Agent and Facebook's OSQuery and how these can be integrated into typical cloud deployments. Delegates should be able to walk away from this tutorial being able to install and manage a cloud deployment of Rekall Agent and OSQuery on their VM endpoints.
These solutions allow the administrators to gain insight into their enterprise wide deployment. For example, one could ask questions such as:
What is the current patch level of all my cloud VM's and containers for each software package? Which VM's are in need of patching? Which VMs have been created recently, and do they comply with minimum security hardening standards?
Who has remote access to my VM's? E.g. via ssh authorized_keys? Via cloud IAM's security policy?
Do any VM's contain a particular indicator of compromise? E.g. Run a YARA signature over all executables on my virtual machines and tell me which ones match.
Sullivan handshake proxying-ieee-sp_2014

Two of the major concerns for serving information over the
internet are latency and security. Reducing latency improves
response times, making content delivery seem more
instantaneous and improving user experience. The most
common approach to improving security is TLS, where data is sent over an authenticated encryption tunnel between a server and a client. The Internet’s architecture and the physical realities of how networks are spread geographically can cause these two goals to be competitive. This talk introduces a model to deal with private key security in this situation.
Nagios Conference 2013 - Nick Scott - Nagios Network Analyzer

Nick Scott's presentation on Nagios Network Analyzer.
The presentation was given during the Nagios World Conference North America held Sept 20-Oct 2nd, 2013 in Saint Paul, MN. For more information on the conference (including photos and videos), visit: http://go.nagios.com/nwcna
Recommended
Application Security - 28 Nov 2018

Share about Azure Secure DevOps Kit and Azure Security Center.
.Net UG Singapore
Mistral and StackStorm

Dmitri Zimine's slides on Design Summit at OpenStack Barcelona 2016. Talked about the history of two projects, technical differences, discussed an overlap and drafted a path forward.
https://www.openstack.org/summit/barcelona-2016/summit-schedule/events/16999/mistral-mistral-and-stackstorm
TLS 1.3 and Other New Features in NGINX Plus R17 and NGINX Open Source

The latest version of the TLS protocol, TLS 1.3, was just released in August 2018. TLS 1.3 is faster and more secure than TLS 1.2. In this webinar, we cover what’s new in TLS 1.3 and how to use it with NGINX, plus other new features in NGINX Open Source and NGINX Plus.
Join this webinar to learn:
- What’s new in TLS 1.3 and why it's faster and more secure than TLS 1.2
- How to use TLS 1.3 with NGINX Plus and NGINX Open Source
- About two-stage rate limiting, simplified OpenID Connect, and 2x faster NGINX and ModSecurity WAF performance
- More with a live demo of TLS 1.3 in action
Watch On-demand: https://www.nginx.com/resources/webinars/tls-1-3-new-features-nginx-plus-r17-nginx-open-source/
An Introduction to WSO2 Microservices Framework for Java

any organizations today are leveraging microservices architecture (MSA) which is becoming increasingly popular because of its many potential advantages. This webinar introduces WSO2 Microservices Framework for Java (MSF4J), which provides the necessary framework and tooling to build an MSA solution.
During this webinar, Sagara will
Introduce WSO2 MSF4J programming model and deployment options
Discuss the key strengths and performance measures of WSO2 MSF4J over other frameworks
Demonstrate security, analytics and service discovery
Highlight tooling, Swagger support and its seamless integration with rest of the platform
Digital Forensics and Incident Response in The Cloud

TUTORIAL: Digital Forensics and Incident Response in the Cloud
Cloud technologies have made it easier for organizations to adapt rapidly to changing IT needs. Teams may acquire (and destroy) new computing resources at a press of a button providing for very flexible deployment environment. While this capability is generally useful, it does come at the cost of increasing management overheads and particularly degraded security posture. Traditionally, IT managers have provided visibility into organizational inventories and could use this information to enforce org wide standard operating environments (SOEs), institute patching regimes etc. However, with the advent of cloud computing, every team can create new VMs and containers on a whim for both production and development use, typically consisting of the cloud service provider's SOE offering.
In this tutorial we explore open source tools available for managing cloud deployments. In particular we look at the endpoint monitoring solutions provided by Google's Rekall Agent and Facebook's OSQuery and how these can be integrated into typical cloud deployments. Delegates should be able to walk away from this tutorial being able to install and manage a cloud deployment of Rekall Agent and OSQuery on their VM endpoints.
These solutions allow the administrators to gain insight into their enterprise wide deployment. For example, one could ask questions such as:
What is the current patch level of all my cloud VM's and containers for each software package? Which VM's are in need of patching? Which VMs have been created recently, and do they comply with minimum security hardening standards?
Who has remote access to my VM's? E.g. via ssh authorized_keys? Via cloud IAM's security policy?
Do any VM's contain a particular indicator of compromise? E.g. Run a YARA signature over all executables on my virtual machines and tell me which ones match.
Digital Forensics and Incident Response in The Cloud

TUTORIAL: Digital Forensics and Incident Response in the Cloud
Cloud technologies have made it easier for organizations to adapt rapidly to changing IT needs. Teams may acquire (and destroy) new computing resources at a press of a button providing for very flexible deployment environment. While this capability is generally useful, it does come at the cost of increasing management overheads and particularly degraded security posture. Traditionally, IT managers have provided visibility into organizational inventories and could use this information to enforce org wide standard operating environments (SOEs), institute patching regimes etc. However, with the advent of cloud computing, every team can create new VMs and containers on a whim for both production and development use, typically consisting of the cloud service provider's SOE offering.
In this tutorial we explore open source tools available for managing cloud deployments. In particular we look at the endpoint monitoring solutions provided by Google's Rekall Agent and Facebook's OSQuery and how these can be integrated into typical cloud deployments. Delegates should be able to walk away from this tutorial being able to install and manage a cloud deployment of Rekall Agent and OSQuery on their VM endpoints.
These solutions allow the administrators to gain insight into their enterprise wide deployment. For example, one could ask questions such as:
What is the current patch level of all my cloud VM's and containers for each software package? Which VM's are in need of patching? Which VMs have been created recently, and do they comply with minimum security hardening standards?
Who has remote access to my VM's? E.g. via ssh authorized_keys? Via cloud IAM's security policy?
Do any VM's contain a particular indicator of compromise? E.g. Run a YARA signature over all executables on my virtual machines and tell me which ones match.
Sullivan handshake proxying-ieee-sp_2014

Two of the major concerns for serving information over the
internet are latency and security. Reducing latency improves
response times, making content delivery seem more
instantaneous and improving user experience. The most
common approach to improving security is TLS, where data is sent over an authenticated encryption tunnel between a server and a client. The Internet’s architecture and the physical realities of how networks are spread geographically can cause these two goals to be competitive. This talk introduces a model to deal with private key security in this situation.
Nagios Conference 2013 - Nick Scott - Nagios Network Analyzer

Nick Scott's presentation on Nagios Network Analyzer.
The presentation was given during the Nagios World Conference North America held Sept 20-Oct 2nd, 2013 in Saint Paul, MN. For more information on the conference (including photos and videos), visit: http://go.nagios.com/nwcna
Informe software libre

Importancias del Software libre en la actualidad, LibreOffice, Aplicaciones informáticas
Over view on Official statistics

informative summary about the official statistics, definitions, partners, process, and new developments in the roles and structures of statistical systems.
LA HUG - Video Testimonials with Chynna Morgan - June 2024

Have you ever heard that user-generated content or video testimonials can take your brand to the next level? We will explore how you can effectively use video testimonials to leverage and boost your sales, content strategy, and increase your CRM data.🤯
We will dig deeper into:
1. How to capture video testimonials that convert from your audience 🎥
2. How to leverage your testimonials to boost your sales 💲
3. How you can capture more CRM data to understand your audience better through video testimonials. 📊
Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...

Evgen Osmak: Methods of key project parameters estimation: from the shaman-inspired to the data-driven praxis (UA)
Kyiv PMDay 2024 Summer
Website – www.pmday.org
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Premium MEAN Stack Development Solutions for Modern Businesses

Stay ahead of the curve with our premium MEAN Stack Development Solutions. Our expert developers utilize MongoDB, Express.js, AngularJS, and Node.js to create modern and responsive web applications. Trust us for cutting-edge solutions that drive your business growth and success.
Know more: https://www.synapseindia.com/technology/mean-stack-development-company.html
RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...

Grote partijen zijn al een tijdje onderweg met retail media. Ondertussen worden in dit domein ook de kansen zichtbaar voor andere spelers in de markt. Maar met die kansen ontstaan ook vragen: Zelf retail media worden of erop adverteren? In welke fase van de funnel past het en hoe integreer je het in een mediaplan? Wat is nu precies het verschil met marketplaces en Programmatic ads? In dit half uur beslechten we de dilemma's en krijg je antwoorden op wanneer het voor jou tijd is om de volgende stap te zetten.
3.0 Project 2_ Developing My Brand Identity Kit.pptx

A personal brand exploration presentation summarizes an individual's unique qualities and goals, covering strengths, values, passions, and target audience. It helps individuals understand what makes them stand out, their desired image, and how they aim to achieve it.
The Parable of the Pipeline a book every new businessman or business student ...

The-Parable of the Pipeline a book every new businessman or business student must read before diving into real world of business.
More Related Content
Viewers also liked
Informe software libre

Importancias del Software libre en la actualidad, LibreOffice, Aplicaciones informáticas
Over view on Official statistics

informative summary about the official statistics, definitions, partners, process, and new developments in the roles and structures of statistical systems.
Viewers also liked (14)
Recently uploaded
LA HUG - Video Testimonials with Chynna Morgan - June 2024

Have you ever heard that user-generated content or video testimonials can take your brand to the next level? We will explore how you can effectively use video testimonials to leverage and boost your sales, content strategy, and increase your CRM data.🤯
We will dig deeper into:
1. How to capture video testimonials that convert from your audience 🎥
2. How to leverage your testimonials to boost your sales 💲
3. How you can capture more CRM data to understand your audience better through video testimonials. 📊
Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...

Evgen Osmak: Methods of key project parameters estimation: from the shaman-inspired to the data-driven praxis (UA)
Kyiv PMDay 2024 Summer
Website – www.pmday.org
Youtube – https://www.youtube.com/startuplviv
FB – https://www.facebook.com/pmdayconference
Premium MEAN Stack Development Solutions for Modern Businesses

Stay ahead of the curve with our premium MEAN Stack Development Solutions. Our expert developers utilize MongoDB, Express.js, AngularJS, and Node.js to create modern and responsive web applications. Trust us for cutting-edge solutions that drive your business growth and success.
Know more: https://www.synapseindia.com/technology/mean-stack-development-company.html
RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...

Grote partijen zijn al een tijdje onderweg met retail media. Ondertussen worden in dit domein ook de kansen zichtbaar voor andere spelers in de markt. Maar met die kansen ontstaan ook vragen: Zelf retail media worden of erop adverteren? In welke fase van de funnel past het en hoe integreer je het in een mediaplan? Wat is nu precies het verschil met marketplaces en Programmatic ads? In dit half uur beslechten we de dilemma's en krijg je antwoorden op wanneer het voor jou tijd is om de volgende stap te zetten.
3.0 Project 2_ Developing My Brand Identity Kit.pptx

A personal brand exploration presentation summarizes an individual's unique qualities and goals, covering strengths, values, passions, and target audience. It helps individuals understand what makes them stand out, their desired image, and how they aim to achieve it.
The Parable of the Pipeline a book every new businessman or business student ...

The-Parable of the Pipeline a book every new businessman or business student must read before diving into real world of business.
Recruiting in the Digital Age: A Social Media Masterclass

In this masterclass, presented at the Global HR Summit on 5th June 2024, Luan Wise explored the essential features of social media platforms that support talent acquisition, including LinkedIn, Facebook, Instagram, X (formerly Twitter) and TikTok.
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection -Introduction to Social Dreaming
#Systems Psychodynamics
#Innovation
#Creativity
#Consultancy
#Coaching
Mastering B2B Payments Webinar from BlueSnap

B2B payments are rapidly changing. Find out the 5 key questions you need to be asking yourself to be sure you are mastering B2B payments today. Learn more at www.BlueSnap.com.
What is the TDS Return Filing Due Date for FY 2024-25.pdf

It is crucial for the taxpayers to understand about the TDS Return Filing Due Date, so that they can fulfill your TDS obligations efficiently. Taxpayers can avoid penalties by sticking to the deadlines and by accurate filing of TDS. Timely filing of TDS will make sure about the availability of tax credits. You can also seek the professional guidance of experts like Legal Pillers for timely filing of the TDS Return.
一比一原版加拿大渥太华大学毕业证(uottawa毕业证书)如何办理

一模一样【q/微:1954292140】【加拿大渥太华大学毕业证(uottawa毕业证书)成绩单Offer】【q/微:1954292140】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【q/微:1954292140】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【q/微:1954292140】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
-- June 2024 is National Volunteer Month --

Check out our June display of books on voluntary organisations
RMD24 | Debunking the non-endemic revenue myth Marvin Vacquier Droop | First ...

Marvin neemt je in deze presentatie mee in de voordelen van non-endemic advertising op retail media netwerken. Hij brengt ook de uitdagingen in beeld die de markt op dit moment heeft op het gebied van retail media voor niet-leveranciers.
Retail media wordt gezien als het nieuwe advertising-medium en ook mediabureaus richten massaal retail media-afdelingen op. Merken die niet in de betreffende winkel liggen staan ook nog niet in de rij om op de retail media netwerken te adverteren. Marvin belicht de uitdagingen die er zijn om echt aansluiting te vinden op die markt van non-endemic advertising.
Recently uploaded (20)
LA HUG - Video Testimonials with Chynna Morgan - June 2024

LA HUG - Video Testimonials with Chynna Morgan - June 2024
Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...

Evgen Osmak: Methods of key project parameters estimation: from the shaman-in...
Bài tập - Tiếng anh 11 Global Success UNIT 1 - Bản HS.doc

Bài tập - Tiếng anh 11 Global Success UNIT 1 - Bản HS.doc
Premium MEAN Stack Development Solutions for Modern Businesses

Premium MEAN Stack Development Solutions for Modern Businesses
RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...

RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...
3.0 Project 2_ Developing My Brand Identity Kit.pptx

3.0 Project 2_ Developing My Brand Identity Kit.pptx
The Parable of the Pipeline a book every new businessman or business student ...

The Parable of the Pipeline a book every new businessman or business student ...
Recruiting in the Digital Age: A Social Media Masterclass

Recruiting in the Digital Age: A Social Media Masterclass
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection with Social Dreaming
What is the TDS Return Filing Due Date for FY 2024-25.pdf

What is the TDS Return Filing Due Date for FY 2024-25.pdf
RMD24 | Debunking the non-endemic revenue myth Marvin Vacquier Droop | First ...

RMD24 | Debunking the non-endemic revenue myth Marvin Vacquier Droop | First ...
Stop Ransomware
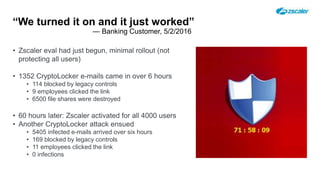
- 1. “We turned it on and it just worked” — Banking Customer, 5/2/2016 • Zscaler eval had just begun, minimal rollout (not protecting all users) • 1352 CryptoLocker e-mails came in over 6 hours • 114 blocked by legacy controls • 9 employees clicked the link • 6500 file shares were destroyed • 60 hours later: Zscaler activated for all 4000 users • Another CryptoLocker attack ensued • 5405 infected e-mails arrived over six hours • 169 blocked by legacy controls • 11 employees clicked the link • 0 infections
Editor's Notes
- Monday Masters 5/2/2016. Banking customer was evaluating Zscaler. Made an emergency decision to activate Zscaler in the middle of a PoC. It went well. Screenshot of customer slide https://drive.google.com/a/zscaler.com/file/d/0B-VgGr-RyWRaTjdxZk9TRm5WR0U/view?usp=sharing