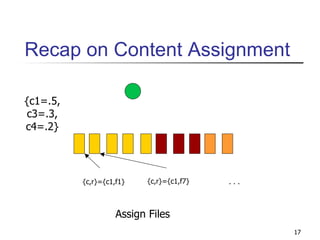
The document describes a query-cycle simulator for simulating peer-to-peer (P2P) networks. The simulator models properties of peers, including content, network parameters, and behavior over successive query cycles. Peer content is modeled by assigning files and interests according to observed distributions. Network parameters like topology and bandwidth are also modeled. Peer behavior, such as query generation and response, is simulated over query cycles based on models derived from measurements of real P2P systems. The simulator aims to accurately model key aspects of P2P networks to enable testing and comparison of P2P algorithms.