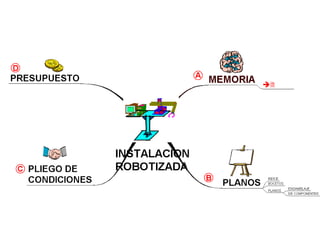
Retro 2001: Presentation of my degree thesis on May-2001
•
0 likes•249 views
Electromechanical robot arm
Report
Share
Report
Share
Recommended
Pinnacle Cart eCommerce - Product Demo 2012

Pinnacle Cart is a leading eCommerce platform founded in 2003. It provides a complete ecommerce ecosystem including shopping cart, order management, marketing, and analytics features. Key features include mobile and social storefronts for one price, PCI compliance, easy to use interface, and integration with QuickBooks and Facebook. The platform is designed to help small and medium businesses increase sales through online stores.
Starlah-Rose Endangered Species

The document discusses endangered animals and species. It notes that over 2,500 animal species are currently endangered. Some key reasons that animals become endangered are discussed, including habitat loss, disease, and human impacts. Endangered means a species is at risk of extinction due to low numbers. The document requests help in protecting endangered animals and getting them to safer places away from threats.
Presentación Mailrelay

Mailrelay es una herramienta de email marketing con características únicas. Te permite crear, enviar y gestionar sus campañas de email con estadísticas completas sobre el comportamiento de sus suscriptores.
Sabrás quién, dónde y cuándo hizo click en tu newsletter. Visualiza el rendimiento de tus boletines electrónicos y mejora tu relación con tus clientes ¡Y tus ventas!
Pete etheridge work

Manchester United's conference and events business needed its own identity to stand out. A new brand, "United Events", was created along with the proposition "where greatness begins". This helped highlight the inspiring atmosphere of Old Trafford while distinguishing the business from the football club. Targeted marketing increased sales and repeat business, and new products like corporate boxes as meeting spaces were developed.
Mc u nguyen bao foi mang foi

This document summarizes medical imaging findings and provides a diagnosis for an 8 month old female patient presenting with high fever, cough, and wheezing. Chest x-ray and CT scans revealed a large heterogeneous mass in the left upper lobe filling and compressing the lung, with associated pleural effusion. Based on these findings and the patient's young age, the diagnosis was determined to be a type II pleuro-pulmonary blastoma, a rare and aggressive malignant tumor of the pleural lung mesenchyme occurring in early childhood. Differential diagnoses including rhabdomyosarcoma and Ewing sarcoma were considered and ruled out.
Recommended
Pinnacle Cart eCommerce - Product Demo 2012

Pinnacle Cart is a leading eCommerce platform founded in 2003. It provides a complete ecommerce ecosystem including shopping cart, order management, marketing, and analytics features. Key features include mobile and social storefronts for one price, PCI compliance, easy to use interface, and integration with QuickBooks and Facebook. The platform is designed to help small and medium businesses increase sales through online stores.
Starlah-Rose Endangered Species

The document discusses endangered animals and species. It notes that over 2,500 animal species are currently endangered. Some key reasons that animals become endangered are discussed, including habitat loss, disease, and human impacts. Endangered means a species is at risk of extinction due to low numbers. The document requests help in protecting endangered animals and getting them to safer places away from threats.
Presentación Mailrelay

Mailrelay es una herramienta de email marketing con características únicas. Te permite crear, enviar y gestionar sus campañas de email con estadísticas completas sobre el comportamiento de sus suscriptores.
Sabrás quién, dónde y cuándo hizo click en tu newsletter. Visualiza el rendimiento de tus boletines electrónicos y mejora tu relación con tus clientes ¡Y tus ventas!
Pete etheridge work

Manchester United's conference and events business needed its own identity to stand out. A new brand, "United Events", was created along with the proposition "where greatness begins". This helped highlight the inspiring atmosphere of Old Trafford while distinguishing the business from the football club. Targeted marketing increased sales and repeat business, and new products like corporate boxes as meeting spaces were developed.
Mc u nguyen bao foi mang foi

This document summarizes medical imaging findings and provides a diagnosis for an 8 month old female patient presenting with high fever, cough, and wheezing. Chest x-ray and CT scans revealed a large heterogeneous mass in the left upper lobe filling and compressing the lung, with associated pleural effusion. Based on these findings and the patient's young age, the diagnosis was determined to be a type II pleuro-pulmonary blastoma, a rare and aggressive malignant tumor of the pleural lung mesenchyme occurring in early childhood. Differential diagnoses including rhabdomyosarcoma and Ewing sarcoma were considered and ruled out.
ISARCAMP: UnserParkplatz.de / Denise Schuster - collaborative consumption, de...

#ISARCAMP @ISARNETZ münchner webwoche 2013 #mww13 -
Keynote:
UnserParkplatz.de / Denise Schuster - collaborative consumption, definitiv kein trend
Cómo entrar en Hotmail (1/2)

Noé Soriano de Mailrelay nos explica las buenas prácticas para que nuestros mailings a Hotmail lleguen a la bandeja de entrada sin problema.
Edtc 6340 assignment 2 ppt

The document discusses copyright and fair use laws. It provides definitions and explanations of key concepts such as copyright, creative commons licenses, orphan works, and fair use. It examines factors in determining fair use and discusses how fair use works in educational settings, including limitations of what can be used under fair use for digital distance education. The TEACH Act is also summarized, including restrictions around what types of works and portions of works can be used under this law.
Derechos fundamentales en el derecho de la información

Los Derechos Fundamentales son aplicables a todas las materias no solo del derecho sino a todas aquellas que se encuentran vinculadas de alguna manera y otra con la sociedad y específicamente con las personas, por tanto el Derecho a la Información no se encuentra ajeno a la necesidad de regularlo de acuerdo a los Derechos Fundamentales planteados inicialmente, para ello es necesario cuestionarnos cuál es la fuente de información activa más potente, barata y útil, no es necesario realizar un exhaustivo análisis para concluir que es el internet, un medio de información que ha demostrado a lo largo de los últimos años que es efectivo y además necesario por las exigencias actuales de adaptarse a la modernidad, por tanto iniciaremos con definir específicamente qué es el internet, viene a ser un conjunto descentralizado de redes de comunicación interconectadas que utilizan la familia de protocolos TCP/IP, lo cual garantiza que las redes físicas heterogéneas que la componen como una red lógica única de alcance mundial estableciendo un intercambio de información constante entre diversos usuarios en un tiempo reducido, si bien es cierto, Internet ya no es un fenómeno nuevo, ha revolucionado el mundo tal y como se conocía hace 30 años. Es un fenómeno global, vinculado estrechamente con la comunicación, pero que influye en gran medida sobre casi todos los ámbitos de la sociedad. Poco podían imaginar sus creadores que en apenas 20 años sería un invento tan imprescindible como el teléfono o la televisión.
Tegnologia

La lista enumera diferentes categorías de tecnología para el hogar, incluyendo tabletas de marcas como Apple, Samsung y Lenovo, computadoras, y cámaras de seguridad.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
CAKE: Sharing Slices of Confidential Data on Blockchain

Presented at the CAiSE 2024 Forum, Intelligent Information Systems, June 6th, Limassol, Cyprus.
Synopsis: Cooperative information systems typically involve various entities in a collaborative process within a distributed environment. Blockchain technology offers a mechanism for automating such processes, even when only partial trust exists among participants. The data stored on the blockchain is replicated across all nodes in the network, ensuring accessibility to all participants. While this aspect facilitates traceability, integrity, and persistence, it poses challenges for adopting public blockchains in enterprise settings due to confidentiality issues. In this paper, we present a software tool named Control Access via Key Encryption (CAKE), designed to ensure data confidentiality in scenarios involving public blockchains. After outlining its core components and functionalities, we showcase the application of CAKE in the context of a real-world cyber-security project within the logistics domain.
Paper: https://doi.org/10.1007/978-3-031-61000-4_16
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Infrastructure Challenges in Scaling RAG with Custom AI models

Building Retrieval-Augmented Generation (RAG) systems with open-source and custom AI models is a complex task. This talk explores the challenges in productionizing RAG systems, including retrieval performance, response synthesis, and evaluation. We’ll discuss how to leverage open-source models like text embeddings, language models, and custom fine-tuned models to enhance RAG performance. Additionally, we’ll cover how BentoML can help orchestrate and scale these AI components efficiently, ensuring seamless deployment and management of RAG systems in the cloud.
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
More Related Content
Viewers also liked
ISARCAMP: UnserParkplatz.de / Denise Schuster - collaborative consumption, de...

#ISARCAMP @ISARNETZ münchner webwoche 2013 #mww13 -
Keynote:
UnserParkplatz.de / Denise Schuster - collaborative consumption, definitiv kein trend
Cómo entrar en Hotmail (1/2)

Noé Soriano de Mailrelay nos explica las buenas prácticas para que nuestros mailings a Hotmail lleguen a la bandeja de entrada sin problema.
Edtc 6340 assignment 2 ppt

The document discusses copyright and fair use laws. It provides definitions and explanations of key concepts such as copyright, creative commons licenses, orphan works, and fair use. It examines factors in determining fair use and discusses how fair use works in educational settings, including limitations of what can be used under fair use for digital distance education. The TEACH Act is also summarized, including restrictions around what types of works and portions of works can be used under this law.
Derechos fundamentales en el derecho de la información

Los Derechos Fundamentales son aplicables a todas las materias no solo del derecho sino a todas aquellas que se encuentran vinculadas de alguna manera y otra con la sociedad y específicamente con las personas, por tanto el Derecho a la Información no se encuentra ajeno a la necesidad de regularlo de acuerdo a los Derechos Fundamentales planteados inicialmente, para ello es necesario cuestionarnos cuál es la fuente de información activa más potente, barata y útil, no es necesario realizar un exhaustivo análisis para concluir que es el internet, un medio de información que ha demostrado a lo largo de los últimos años que es efectivo y además necesario por las exigencias actuales de adaptarse a la modernidad, por tanto iniciaremos con definir específicamente qué es el internet, viene a ser un conjunto descentralizado de redes de comunicación interconectadas que utilizan la familia de protocolos TCP/IP, lo cual garantiza que las redes físicas heterogéneas que la componen como una red lógica única de alcance mundial estableciendo un intercambio de información constante entre diversos usuarios en un tiempo reducido, si bien es cierto, Internet ya no es un fenómeno nuevo, ha revolucionado el mundo tal y como se conocía hace 30 años. Es un fenómeno global, vinculado estrechamente con la comunicación, pero que influye en gran medida sobre casi todos los ámbitos de la sociedad. Poco podían imaginar sus creadores que en apenas 20 años sería un invento tan imprescindible como el teléfono o la televisión.
Tegnologia

La lista enumera diferentes categorías de tecnología para el hogar, incluyendo tabletas de marcas como Apple, Samsung y Lenovo, computadoras, y cámaras de seguridad.
Viewers also liked (6)
ISARCAMP: UnserParkplatz.de / Denise Schuster - collaborative consumption, de...

ISARCAMP: UnserParkplatz.de / Denise Schuster - collaborative consumption, de...
Derechos fundamentales en el derecho de la información

Derechos fundamentales en el derecho de la información
Recently uploaded
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
CAKE: Sharing Slices of Confidential Data on Blockchain

Presented at the CAiSE 2024 Forum, Intelligent Information Systems, June 6th, Limassol, Cyprus.
Synopsis: Cooperative information systems typically involve various entities in a collaborative process within a distributed environment. Blockchain technology offers a mechanism for automating such processes, even when only partial trust exists among participants. The data stored on the blockchain is replicated across all nodes in the network, ensuring accessibility to all participants. While this aspect facilitates traceability, integrity, and persistence, it poses challenges for adopting public blockchains in enterprise settings due to confidentiality issues. In this paper, we present a software tool named Control Access via Key Encryption (CAKE), designed to ensure data confidentiality in scenarios involving public blockchains. After outlining its core components and functionalities, we showcase the application of CAKE in the context of a real-world cyber-security project within the logistics domain.
Paper: https://doi.org/10.1007/978-3-031-61000-4_16
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Infrastructure Challenges in Scaling RAG with Custom AI models

Building Retrieval-Augmented Generation (RAG) systems with open-source and custom AI models is a complex task. This talk explores the challenges in productionizing RAG systems, including retrieval performance, response synthesis, and evaluation. We’ll discuss how to leverage open-source models like text embeddings, language models, and custom fine-tuned models to enhance RAG performance. Additionally, we’ll cover how BentoML can help orchestrate and scale these AI components efficiently, ensuring seamless deployment and management of RAG systems in the cloud.
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Recently uploaded (20)
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
CAKE: Sharing Slices of Confidential Data on Blockchain

CAKE: Sharing Slices of Confidential Data on Blockchain
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean lotus Threat actors project by John Sitima 2024 (1).pptx
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
Infrastructure Challenges in Scaling RAG with Custom AI models

Infrastructure Challenges in Scaling RAG with Custom AI models
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
