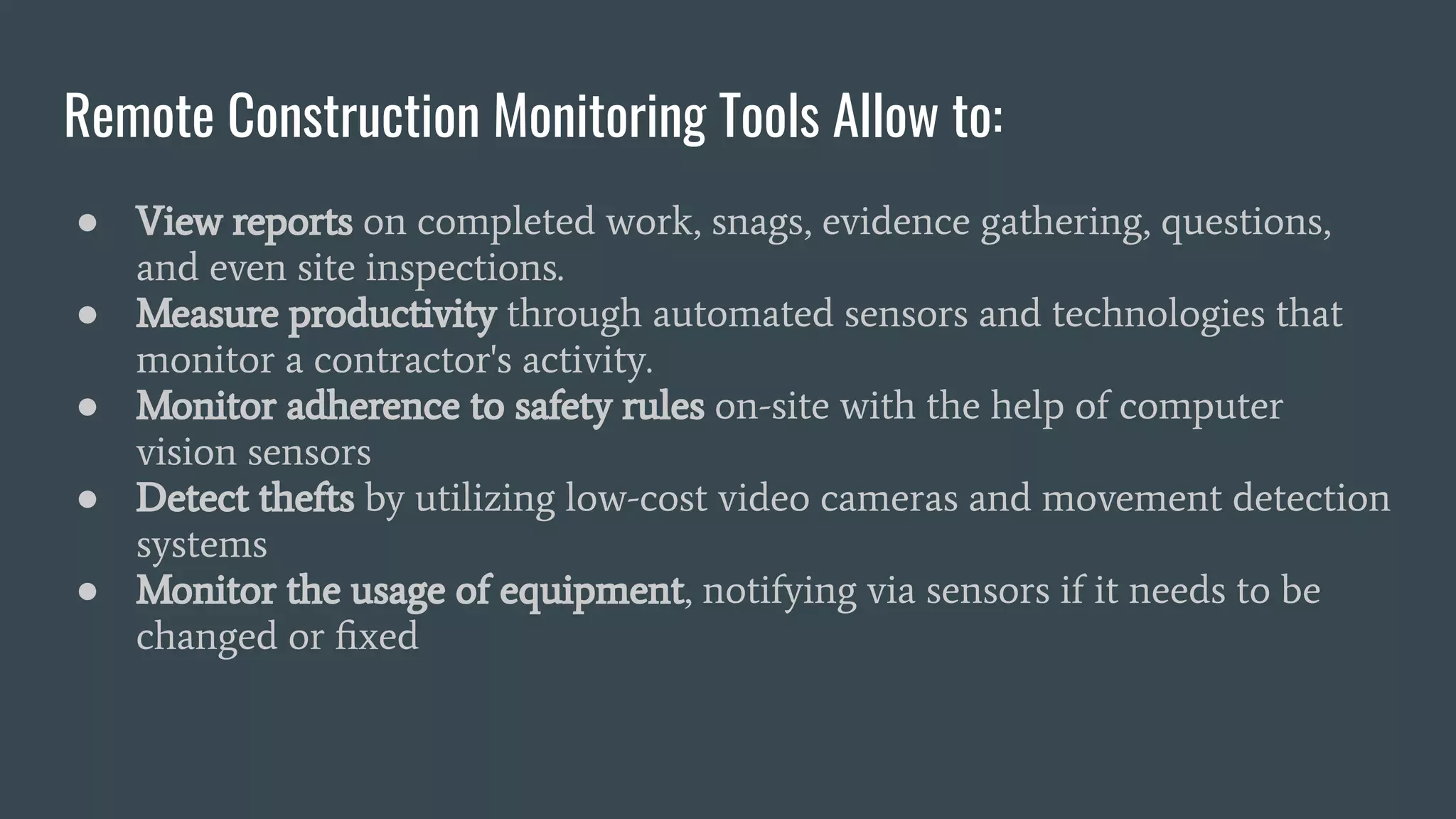
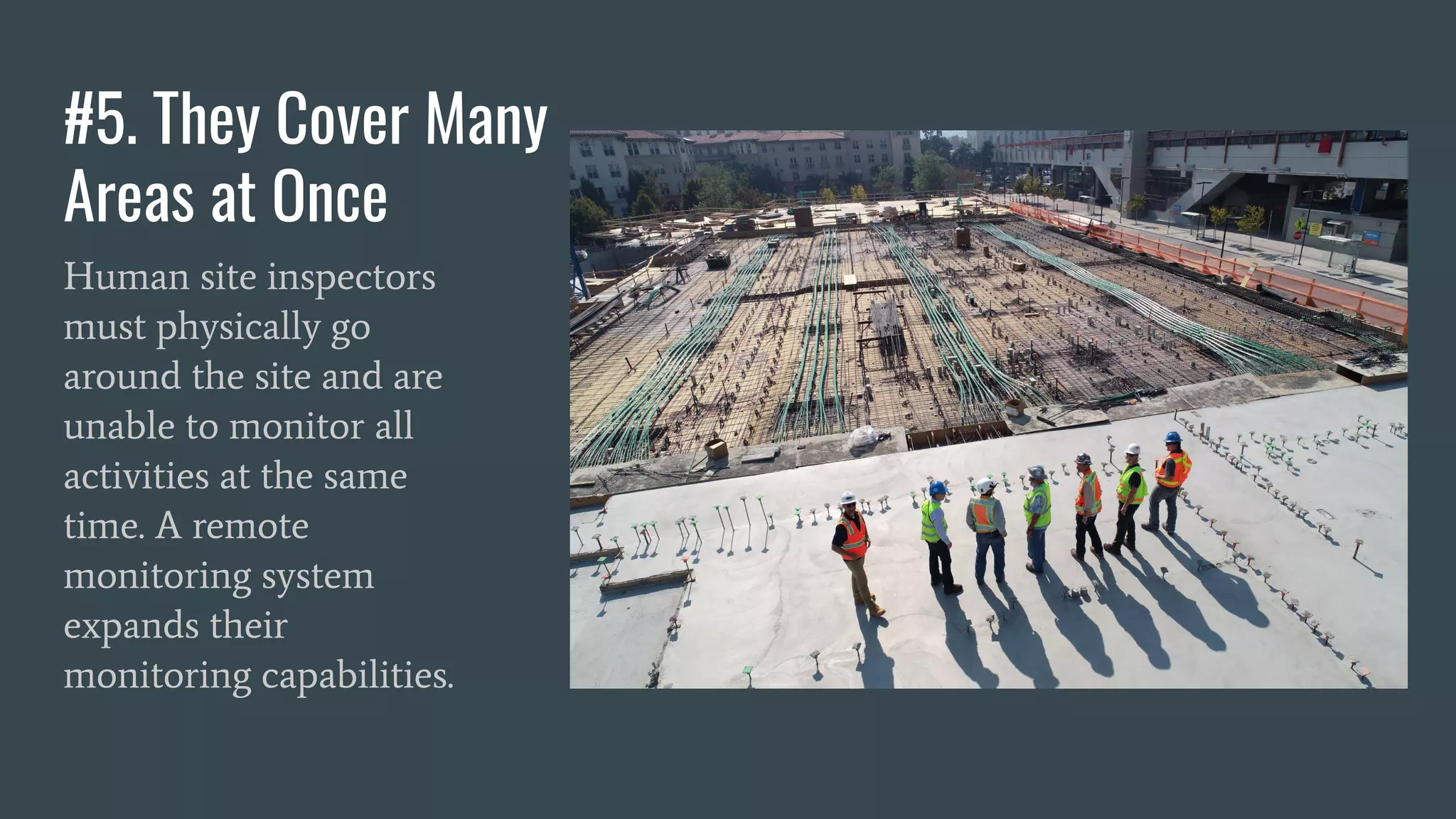
The document discusses the rise of remote construction monitoring, particularly due to the impact of the coronavirus pandemic, which has led to increased remote work in the construction industry. It outlines the advantages of remote monitoring systems, such as cost savings, improved safety, theft reduction, and the ability to monitor project progress from anywhere without the need for physical site visits. The document also mentions PlanRadar as a tool for managing defects, communication, and monitoring in construction projects.