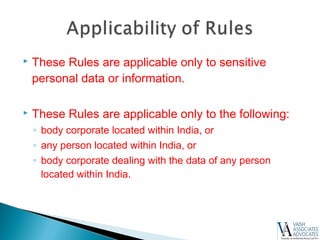
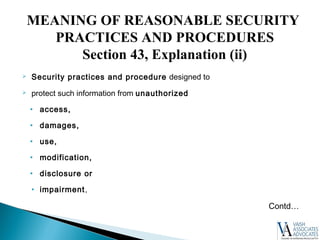
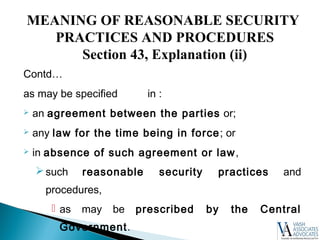
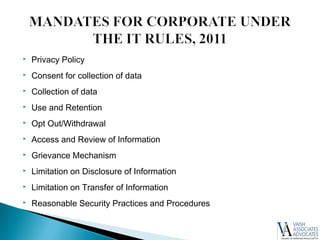
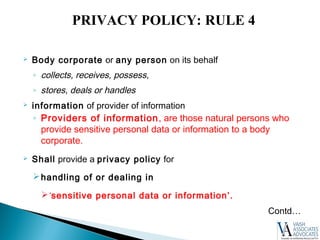
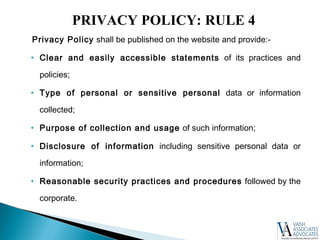
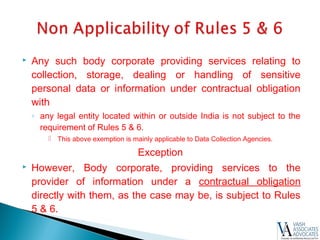
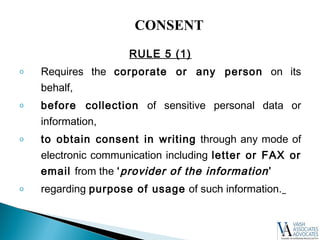
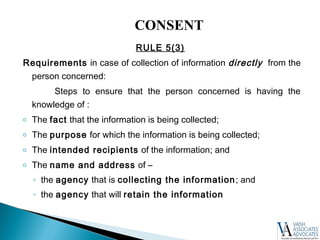
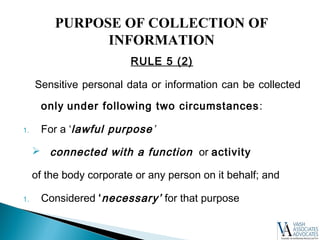
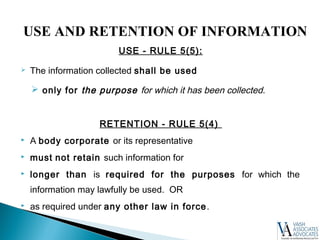
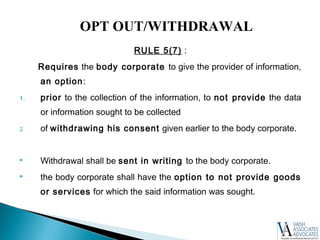
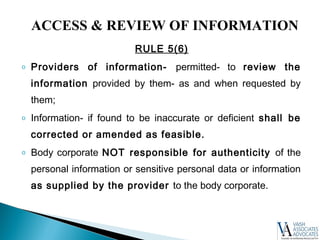
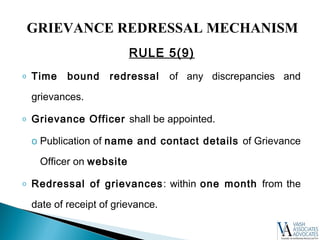
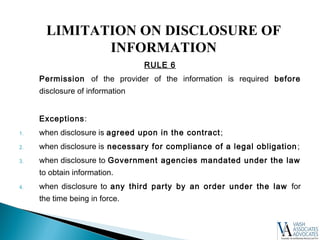
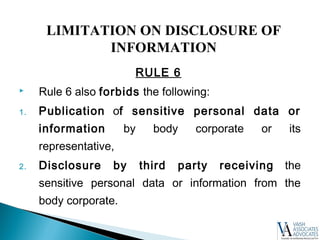
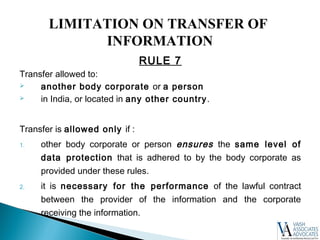
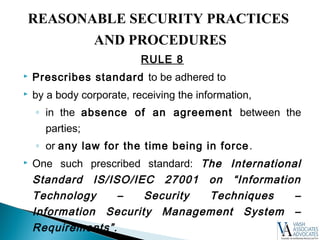
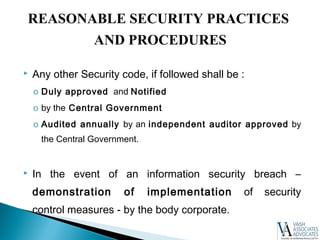
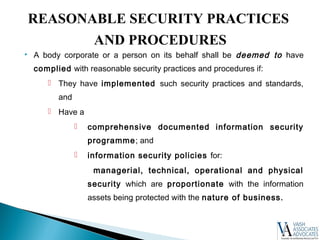
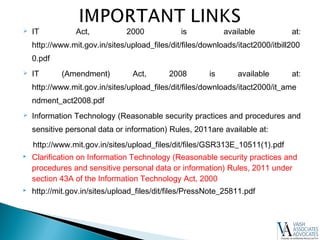
The document summarizes key aspects of data protection law in India. It outlines the Information Technology Act of 2000 and its amendments in 2008 that introduced provisions for protecting personal data. The Ministry of Communications and Information Technology then promulgated the Reasonable Security Practices and Procedures and Sensitive Personal Data or Information Rules in 2011 under these acts. The rules define sensitive personal data and set forth requirements for companies regarding privacy policies, consent, data access, security practices, and more to protect Indian citizens' personal information.