Reasearch of moving toys
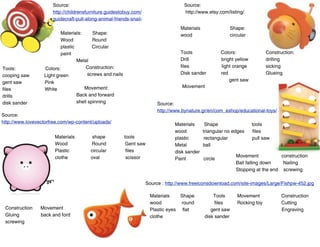
- 1. Source: Source: http://childrensfurniture.guidestobuy.com/ http://www.etsy.com/listing/ guidecraft-pull-along-animal-friends-snail- Materials Shape: Materials: Shape: wood circular Wood Round plastic Circular paint Tools Colors: Construction: Metal Drill bright yellow drilling Construction: files light orange sicking Tools: Colors: screws and nails Disk sander red Glueing cooping saw Light green gent saw gent saw Pink Movement: Movement files White drills Back and forward disk sander shell spinning Source: http://www.bynature.gr/en/com_eshop/educational-toys/ Source: http://www.lovevectorfree.com/wp-content/uploads/ Materials Shape tools wood triangular no edges files Materials shape tools plastic rectangular pull saw Wood Round Gent saw Metal ball Plastic circular files disk sander clothe oval scissor Movement construction Paint circle Ball falling down Nailing Stopping at the end screwing Source : http://www.freeiconsdownload.com/site-images/Large/Fishpw-452.jpg Materials Shape Tools Movement Construction wood round files Rocking toy Cutting Construction Movement Plastic eyes flat gent saw Engraving Gluing back and ford clothe disk sander screwing
- 2. Source: http://www.desktop2wallpapers.com/wallpaper/Cute-bee/ Source:http:// Materials Shape Tools Materials shape Tools Wood round File Plastic Oval Disk sander String Circular drill engraving Construction: Construction Movement filing and sticking together Gluing together back and ford wheels Movement Materials shape Source :http:// wood same shape as the picture Materials Shape Tools Paint Wood round disk sander paint tentacles shape drill Contruction movement wheels construction sanding and gluing together Source: Memory game - zazil Movement forward some tentacles moving Source: Baby einstein - My first words page 19 Source: Mein erstes Lexikon A-Z Materials shape tools Materials shape tools Wood round with Paint craws sticking outside Contruction Construction filing it and drawing the shape in Movement