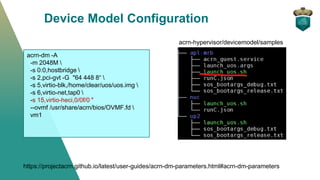
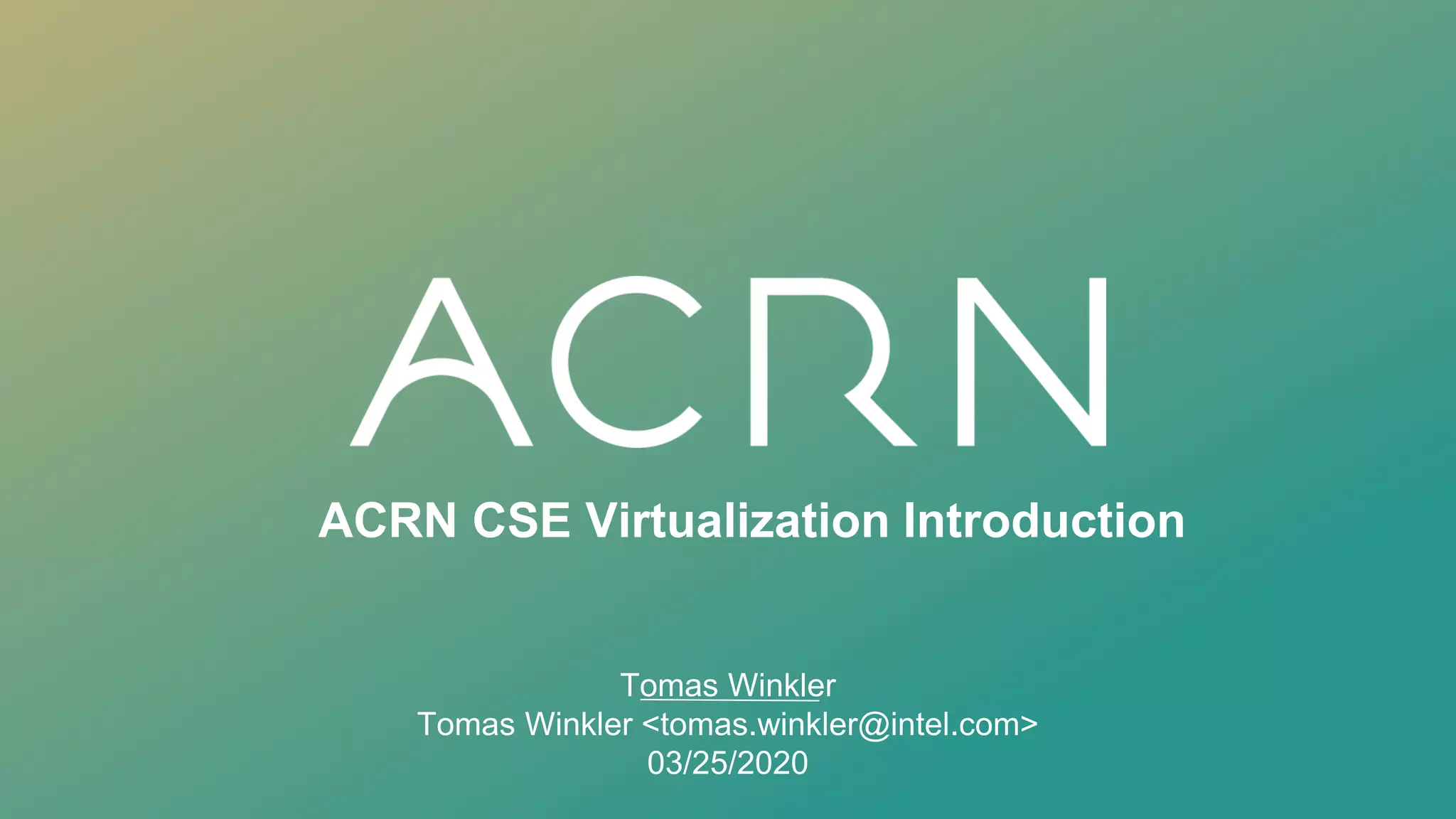
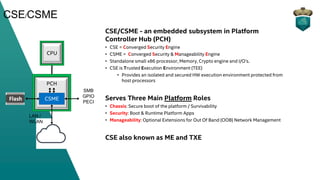
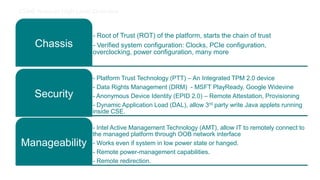
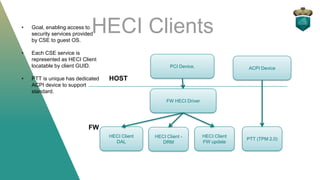
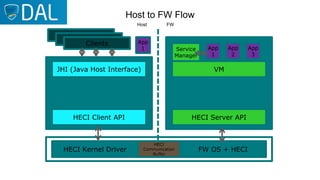
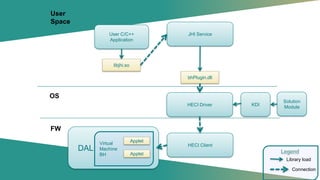
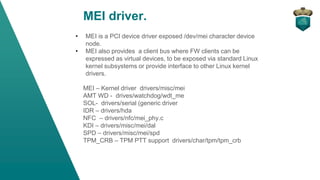
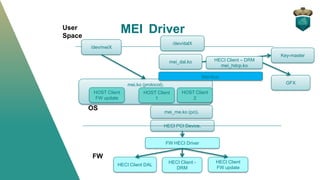
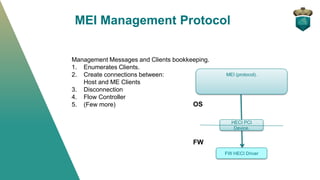
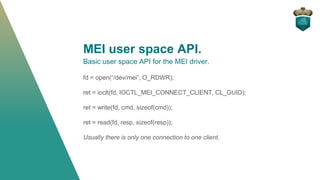
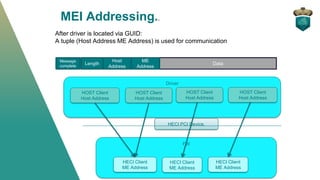
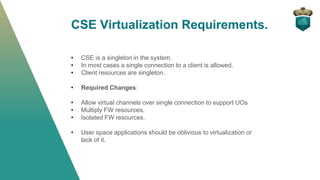
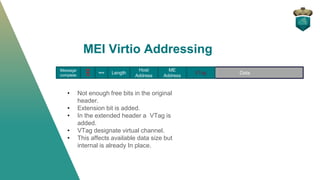
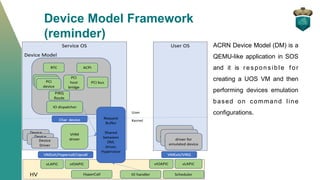
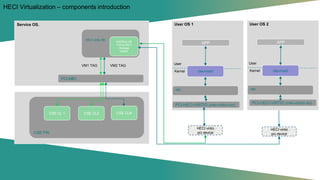
The document provides an overview of the Converged Security Engine (CSE) and how it is virtualized in ACRN. It discusses how the CSE provides security features like DRM and dynamic application loading. It then explains how the Management Engine Interface (MEI) driver is used to access CSE features and how MEI is virtualized using a front-end and back-end driver with VirtIO and addressing extensions to support multiple guest VMs. The ACRN device model is used to configure virtual MEI devices for each VM.


![MEI Front end driver.
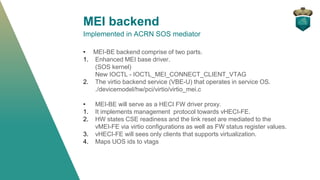
mei-virtio.ko
• mei-virito.ko implements a
virtio_driver that binds to virtio
device [0x1AF4, 0x8602]. The
device ID is hard coded in ACRN
device model.
• The driver implements virtio_driver
handlers: probe, remove,
config_changes, freeze, and
restore.
• The driver is using two virtio
queues for communication. One for
RX and one for TX.
OS HECI Driver
(e.g. /dev/mei0)
mei.ko
mei_virtio.ko
vHECI-FE
virtio
mei_me.ko](https://image.slidesharecdn.com/ww1520acrncsevirtualization-200426203604/85/Project-ACRN-CSE-Virtualization-27-320.jpg)