The survey conducted by Tsaaro Academy aimed to understand the privacy job market and privacy as a career choice. Key findings include:
- 96% of privacy professionals had less than 3 years of experience, indicating a growing field.
- 90% felt that privacy job opportunities would grow exponentially.
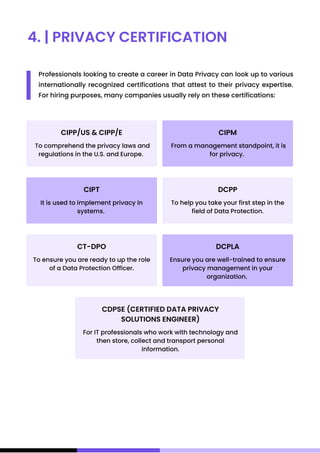
- 73% of professionals who obtained privacy certifications experienced promotions and salary increases.
- Common certifications held were IAPP and in-house certificates, with an average post-certification pay hike of 15-23%.
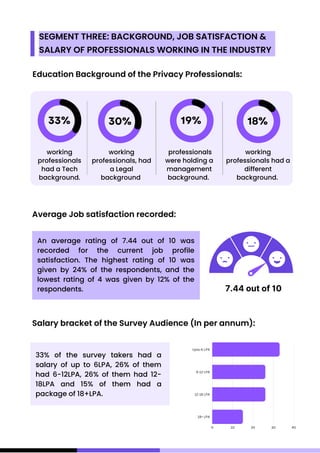
- Respondents were satisfied with their privacy roles, giving an average 7.44/10 rating.
- The majority earned between 6-18 LPA, with 33% under 6 LPA