Embed presentation
Download to read offline












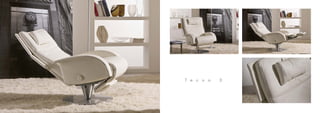
Il documento sembra riferirsi a Bertosalotti, un'azienda specializzata in poltrone. Potrebbe contenere dettagli relativi alla gestione delle prenotazioni o servizi professionali, ma non fornisce informazioni chiare su ulteriori aspetti.