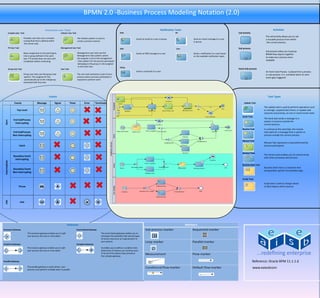
Oracle BPMN 2.0 Poster
- 1. BPMN 2.0 -Business Process Modeling Notation (2.0) Interactive user Tasks Notification Tasks Activities Complex User Task Initiator User Task Mail IM Call Activity The call activity allows you to call Complex user task uses a complex The initiator pattern is used to Sends an email to a user or group. Send an instant message to a user a reusable process from within routing flow that is defined within create a process instance or group. the human task. the current process. FYI User Task Management User Task SMS User Sub process Sub process allow you to group Bases assignment on the participant, Management user task uses the Sends an SMS message to a user Sends a notification to a user based BPMN flow objects together role or group defined in the swim Management chain pattern where on the available notification types. the assignee is set to the management to make your process more lane. FYI activity does not wait until completion before continuing chain pattern for the process participant readable belonging to the group or role assigned to the swim lane Voice Group User Task User Task Event Sub process Sends a voicemail to a user. An Event Sub-Process is placed into a process Group user task uses the group vote The user task represents a part of your or sub-process. It is activated when its start pattern. The assignee for this process where a process participant is event gets triggered automatically set to the role/group required to perform work. associated with the Lane. Events Events Task Types Events Message Signal Timer Error Terminate Update Task The update task is used to perform operations such Top Level as reassign, suspend task timers, or update task outcome and priority, on one or more human tasks Send Task The Send task sends a message to a End SubProcess Start system or process outside the Interrupting current process. Receive Task In contrast to the send task, the receive End SubProcess task waits for a message from a system or Non Interrupting process outside the current process. Manual Task Manual Task represents a task performed by Catch process participants Service Task The Service task enables you to communicate Boundary Event with other processes and services. Interrupting Intermediate Business Rule Task Business Rule Task is a container that Boundary Event encapsulates specific functionality logic. Non Interrupting Script Task Script task is used to change values Throw of data objects within process END END Gateways Exclusive Gateway Event Based Gateway The exclusive gateway enables you to split The event-based gateway enables you to your process into two or more paths. anticipate the possibility that several types of events may occur at a special point in your process. Inclusive Gateway Complex Gateway The inclusive gateway enables you to split It enables you to define a condition that your process into two or more paths determines if instance can continue even if not all of the tokens have arrived at the complex gateway. Parallel Gateway Reference: Oracle BPM 11.1.1.6 The parallel gateway is useful where your process must perform multiple tasks in parallel www.eaiesbcom
