1. Oracle Database 12c includes new features such as pluggable databases for consolidation, increased size limits for data types, and inline PL/SQL functions.
2. Other features include improved redaction policies, the ability to migrate table partitions online without disruption, and indexing on single columns.
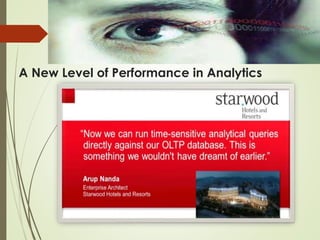
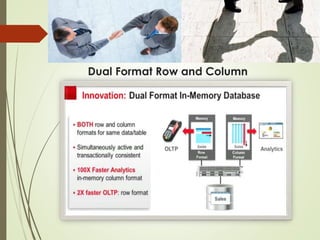
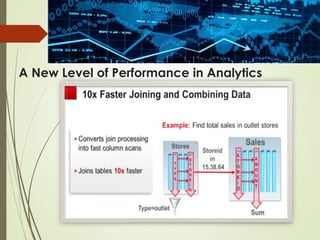
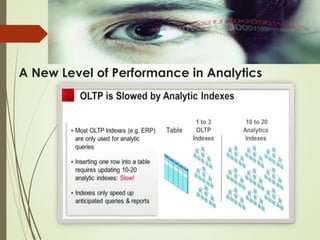
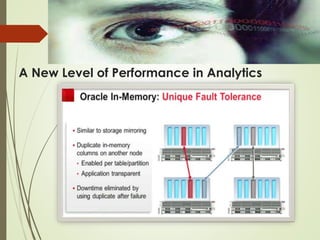
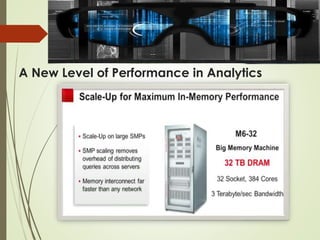
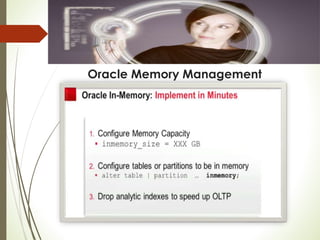
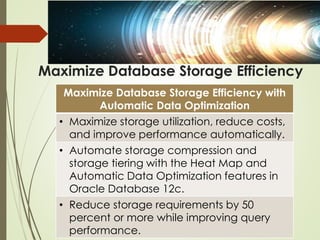
3. Performance is also enhanced through in-memory options, adaptive query optimization, and temporary undo settings.