The document explains the fundamentals of object-oriented programming (OOP) in Java, detailing the nature of objects, their states, behaviors, and instantiation. It covers key concepts like class vs. object distinction, UML diagrams for object design, relationships between objects, and the necessity of reducing dependencies in software design. Exercises and examples are provided to illustrate these concepts and facilitate learning.
![© Justin Robertson 2017. All rights reserved.
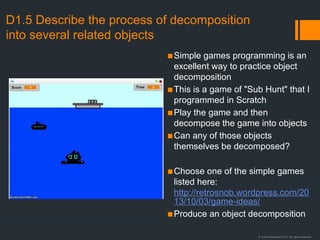
Relationships between UML objects
Bird
- species: String
- etc
+ getSpecies: String
+ setSpecies(species: String): void
Finch
[Finch-specifc variables]
[Finch-specifc methods]
Club
- members: Member[]
+ getMember(id: int): Member
Member
- id: int
+ getId(): int
Course
- students: Student[]
+ getStudent(id: int): Student
Student
- id: int
+ getId(): int
Inheritance
A finch is a bird.
Note that the arrow points at the
superclass.
Composition
A club has members..
When the club is deleted, its
members are deleted too.
Aggregation
A course has students..
When the course is deleted, the
students remain in the system..
Note: I doubt you would ever have to distinguish between composition and aggregation. If you get a
question and you think the answer is composition/aggregation then I suggest you do what I just did
and write "composition/aggregation" and then add "a Club has a Member" and give an example.
I also doubt you will need to remember the shapes of the connectors. I'm sure it would be fine just to
draw a line between the boxes and write "is a" or "has" in these cases.](https://image.slidesharecdn.com/optiond-241110213038-58524ecb/85/Option-D-Relacion-de-Conceptos-basicos-de-modelamiento-9-320.jpg)
![© Justin Robertson 2017. All rights reserved.
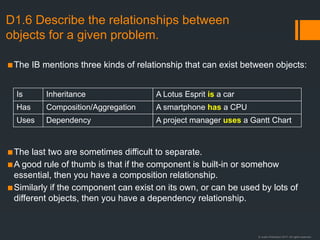
Practice with inheritance hierarchies
Sample Superclasses:
▪ Vehicle {Car, Bus, Lorry}
▪ Animal {…etc
▪ Employee
▪ RPGCharacter
▪ Shape
▪ Publication
▪ Subject
▪ Teacher
▪ Student
Task:
1. Choose a superclass.
2. Identify three possible subclasses
3. Identify one variable and one method
that belongs to the superclass
4. Identify one variable and one method
for each of the subclasses
▪ The "is-a" test
If you create an inheritance hierarchy e.g.
class [Subclass] extends [Superclass], then
it must make sense to say the sentence:
"A [Subclass] is a [Superclass]"
(e.g. "A square is a shape" makes sense.)
▪ If that sentence doesn't make sense for your
example, then you haven't got an
inheritance hierarchy.
▪ Which of these are valid inheritance
hierarchies using the "is-a" test?
▪ class Finch extends Bird
▪ class Guitar extends Instrument
▪ class Teacher extends School
▪ class Player extends FootballTeam
▪ class Beef extends Meat
▪ class Actor extends Movie](https://image.slidesharecdn.com/optiond-241110213038-58524ecb/85/Option-D-Relacion-de-Conceptos-basicos-de-modelamiento-29-320.jpg)
![© Justin Robertson 2017. All rights reserved.
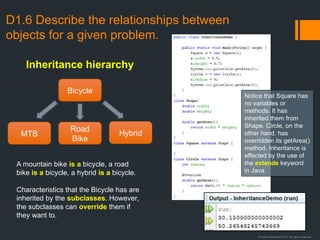
A quick word about
the super keyword
• Super refers to the
superclass.
• When called as a method,
super() refers to the
superclass constructor.
• If the superclass
constructor is overloaded
then super() can be called
with parameters and
polymorphism will ensure
that the correct constructor
is called.
• In the example note that id
is private to the Employee
and so can't be accessed
in the Teacher.
• However, the value of the
id field can be set using a
call to the super() function
with id as a parameter.
public class SuperDemo {
public static void main(String[] args) {
System.out.println("Starting main...");
Teacher teacher = new Teacher(345);
System.out.println(teacher.getId());
}
}
class Employee {
private int id;
Employee() {
System.out.println("Employee constructor");
}
Employee(int id) {
this.id = id;
}
public int getId() {
return id;
}
}
class Teacher extends Employee {
Teacher() {
super();
System.out.println("Teacher constructor");
}
Teacher(int id) {
super(id);
}
}](https://image.slidesharecdn.com/optiond-241110213038-58524ecb/85/Option-D-Relacion-de-Conceptos-basicos-de-modelamiento-37-320.jpg)
![© Justin Robertson 2017. All rights reserved.
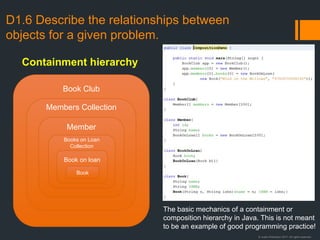
D3.8 Construct code examples related
to static arrays
• Declaration of an array
literal
• Direct access
• Standard array traversals
using a for loop and an
enhanced for loop
int array[] = {2, 5, 4, 8, 6, 7, 1, 3};
arry[4] = 0;
for (int i = 0; x < array.length; i = i + 1)
{
output(array[i]);
}
for (int i : array) {
output(i);
}](https://image.slidesharecdn.com/optiond-241110213038-58524ecb/85/Option-D-Relacion-de-Conceptos-basicos-de-modelamiento-45-320.jpg)
![© Justin Robertson 2017. All rights reserved.
D4.3 Construct algorithms that use recursion
• In addition to the factorial algorithm, here are some other recursive algorithms in Java that are
relevant to the course.
HL only
void hanoi(int n, int from, int to, int via){
if (n==0) {
return;
}
else{
hanoi(n-1, from, via, to);
System.out.println(count++ + ". Move a disc
from " + from + " to " + to);
hanoi(n-1, via, to, from);
}
}
int binary_search(int A[], int key, int imin, int imax) {
// calculate midpoint to cut set in half
int imid = midpoint(imin, imax);
// three-way comparison
if (A[imid] > key)
// key is in lower half of the list
return binary_search(A, key, imin, imid-1);
else if (A[imid] < key)
// key is in upper half of the list
return binary_search(A, key, imid+1, imax);
else
// key has been found
return imid;
}
void insertNode(Node root, int data) {
if (root == NULL)
root = new Node(data);
else if (data < root.getData())
insertNode(root.getLeft(), data);
else
insertNode(root.getRight(), data);
}
void inOrder(Node n){
if(n == null) return;
inOrder(n.left);
print(n);
inOrder(n.right);
}
Towers of Hanoi
inOrder binary tree traversal
Binary tree node insertion
Binary search](https://image.slidesharecdn.com/optiond-241110213038-58524ecb/85/Option-D-Relacion-de-Conceptos-basicos-de-modelamiento-51-320.jpg)