This document contains summaries of student scores on several exams:
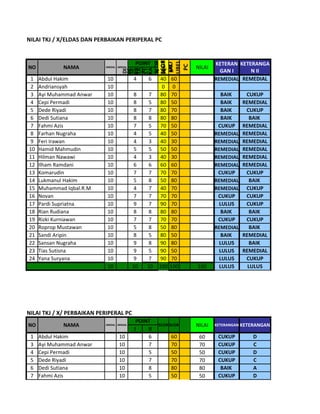
1. The first section summarizes scores on an exam about computer hardware and peripherals. It lists students' names, scores on two parts of the exam, total scores, and performance levels.
2. The second section summarizes scores on an exam about repairing computer peripherals. It follows a similar format to the first section.
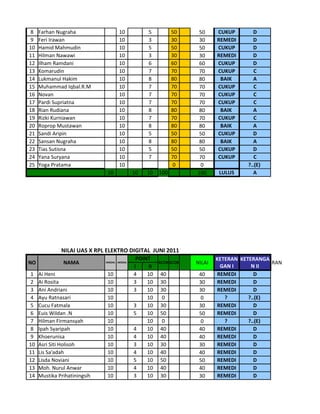
3. The third section summarizes scores on a digital electronics exam from June 2011. It lists students' names, scores on two parts of the exam, total scores, performance levels, and letter grades.
4. The fourth section summarizes scores on an exam about installing computer networks using text and GUI