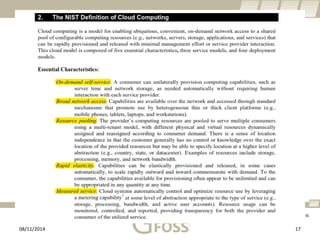
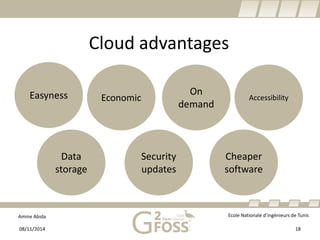
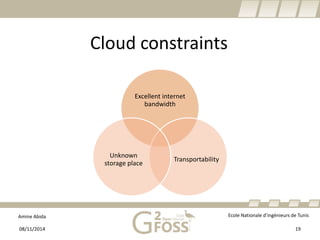
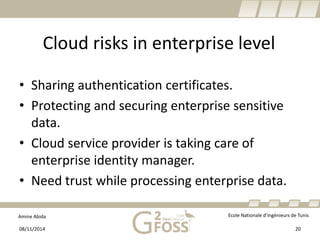
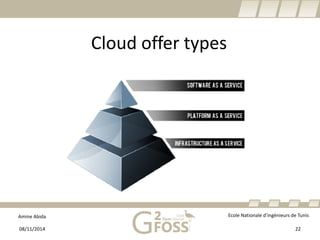
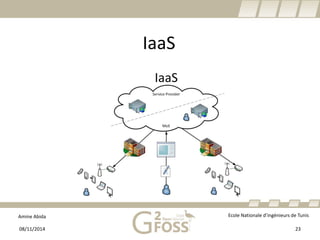
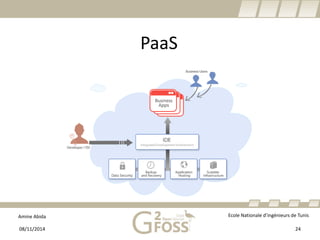
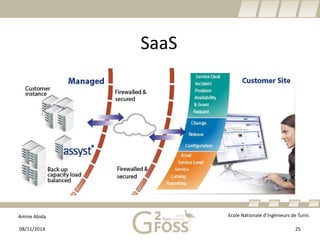
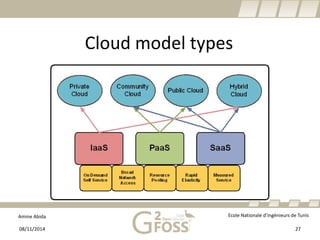
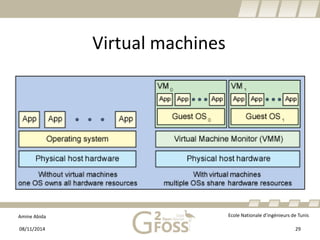
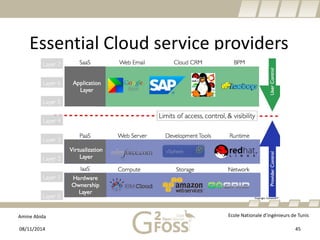
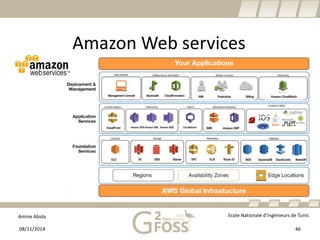
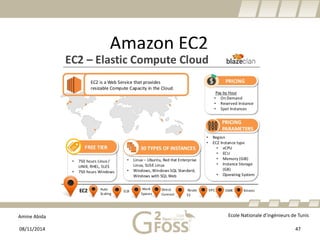
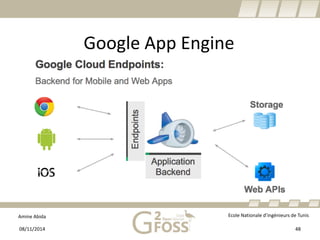
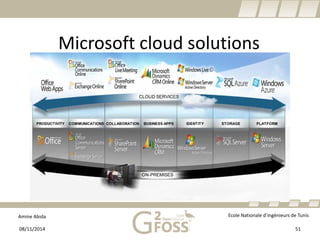
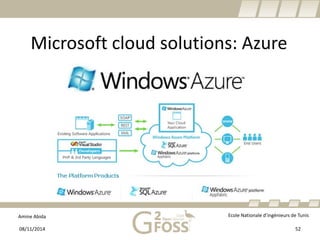
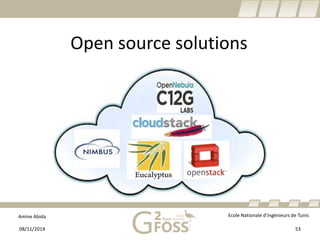
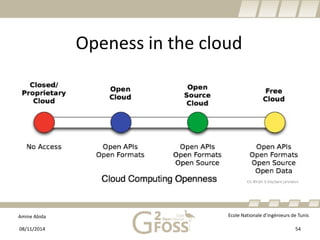
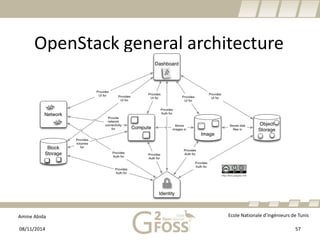
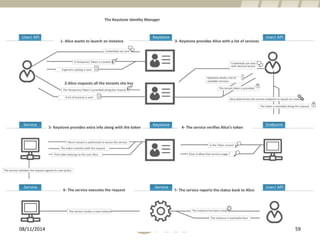
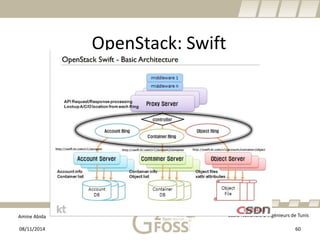
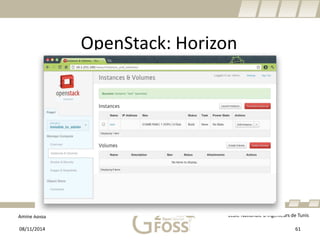
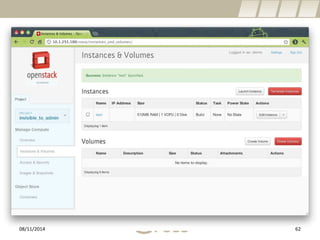
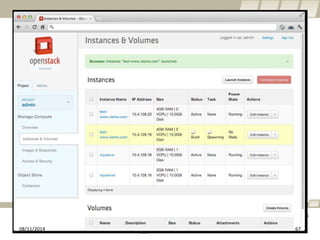
The document discusses cloud computing and open source solutions. It begins with introductions and definitions of distributed systems, cloud computing, and cloud service models. It then describes common cloud infrastructure providers like Amazon Web Services, Google, and Microsoft Azure. Finally, it introduces the open source cloud solution OpenStack, describing some of its core components and functions.