ILSR 2019 12 rural coop policy brief update page 8
•
0 likes•101 views
Institute for Local Self-Reliance rural coop policy brief update
Report
Share
Report
Share
Download to read offline
Recommended
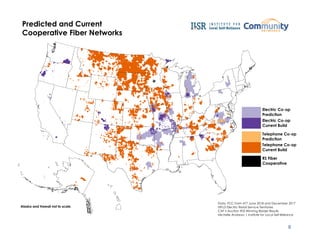
Updated Policy Brief: Cooperatives Bring Fiber Internet Access to Rural America

Originally published in 2017, our report, Cooperatives Fiberize Rural America: A Trusted Model for the Internet Era, focuses on cooperatives as a proven model for deploying fiber optic Internet access across the country. An update in the spring of 2019 included additional information about the rate co-ops are expanding Internet service, and now we’ve updated it again, with a new map and personal stories from areas where co-ops have drastically impacted local life.
Maximizing information and communications technologies for development in fai...

COMMUNICATIONS United Methodist Communications THE UNITED METHODIST CHURCH
UCX: An Open Source Framework for HPC Network APIs and Beyond

Pavel Shamis, research scientist at the Department of Energy’s Oak Ridge National Laboratory
Digital Inclusion and Meaningful Broadband Adoption Initiatives Colin Rhinesm...

This report presents findings from a national study of digital inclusion organizations that help low-income individuals and families adopt high-speed Internet service. The study looked at eight digital inclusion organizations across the United States that are working at the important intersection between making high-speed Internet available and strengthening digital skills—two essential and interrelated components of digital inclusion, which is focused on increasing digital access, skills, and relevant content.
Recommended
Updated Policy Brief: Cooperatives Bring Fiber Internet Access to Rural America

Originally published in 2017, our report, Cooperatives Fiberize Rural America: A Trusted Model for the Internet Era, focuses on cooperatives as a proven model for deploying fiber optic Internet access across the country. An update in the spring of 2019 included additional information about the rate co-ops are expanding Internet service, and now we’ve updated it again, with a new map and personal stories from areas where co-ops have drastically impacted local life.
Maximizing information and communications technologies for development in fai...

COMMUNICATIONS United Methodist Communications THE UNITED METHODIST CHURCH
UCX: An Open Source Framework for HPC Network APIs and Beyond

Pavel Shamis, research scientist at the Department of Energy’s Oak Ridge National Laboratory
Digital Inclusion and Meaningful Broadband Adoption Initiatives Colin Rhinesm...

This report presents findings from a national study of digital inclusion organizations that help low-income individuals and families adopt high-speed Internet service. The study looked at eight digital inclusion organizations across the United States that are working at the important intersection between making high-speed Internet available and strengthening digital skills—two essential and interrelated components of digital inclusion, which is focused on increasing digital access, skills, and relevant content.
Innovation Accelerators Report

Innovation Accelerators:
Defining Characteristics Among Startup Assistance Organizations by C. Scott Dempwolf, Jennifer Auer, and
Michelle D’Ippolito
Optimal Solutions Group, LLC
College Park, MD 20740
contract number SBAHQ -13-M-0197
Release Date: October 2014
This report was developed under a contract with the Small Business Administration, Office of Advocacy, and contains information and analysis that were reviewed by officials of the Office of Advocacy. However, the final conclusions of the report do not necessarily reflect the views of the Office of Advocacy.
Strategy for American Innovation

America has long been a nation of innovators. The United States is the birthplace of the Internet, which today connects three billion people around the world. American scientists and engineers sequenced the human genome, invented the semiconductor, and sent humankind to the moon. And America is not done yet. For an advanced economy such as the United States, innovation is a wellspring of economic growth. While many countries can grow by adopting existing technologies and business practices, America must continually innovate because our workers and firms are often operating at the technological frontier. Innovation is also a powerful tool for addressing our most pressing challenges as a nation, such as enabling more Americans to lead longer, healthier lives, and accelerating the transition to a low-carbon economy.
Report to the President and Congress Ensuring Leadership in Federally Funded ...

In the report, PCAST focuses on eight R&D areas: cybersecurity, IT and health, Big Data and data-intensive computing, IT and the physical world, privacy protection, cyber-human systems, high capability computing, and foundational computing research. All of these areas help to achieve the Nation’s priorities. For example, Big Data, IT and the physical world, and high-capability computing are essential contributors to addressing issues within energy and the environment.
Data Act Federal Register Notice Public Summary of Responses

Summary of Responses to the Treasury Bureau of the Fiscal Service Notice in the Federal Register on 9/26/2014 for “Public Input on the Establishment of Financial Data Standards (Data Exchange)
Supporting high throughput high-biotechnologies in today’s research environme...

St. Jude Children’s Research Hospital, Hartwell Center and Molecular Biotechnology, Clayton W. Naeve, Ph.D.
Common Design Elements for Data Movement Eli Dart

Eli Dart, Network Engineer ESnet Science Engagement Lawrence Berkeley National Laboratory Cosmology CrossConnects Workshop Berkeley, CA February 11, 2015
Strategies for Improving the U.S. Payment System

The Federal Reserve believes that the U.S. payment system is at a critical juncture in its evolution. Technology is rapidly changing many elements that support the payment process. High-speed data networks are becoming ubiquitous, computing devices are becoming more sophisticated and mobile, and information is increasingly processed in real time. These capabilities are changing the nature of commerce and end-user expectations for payment services. Meanwhile, payment security and the protection of sensitive data, which are foundational to public confidence in any payment system, are challenged by dynamic, persistent and rapidly escalating threats. Finally, an increasing number of U.S. citizens and businesses routinely transfer value across borders and demand better payment options to swiftly and efficiently do so.
Experiences In Building Globus Genomics Using Galaxy, Globus Online and AWS

Ravi K Madduri
University of Chicago and ANL
UNDERSTANDING THE DEBATE OVER GOVERNMENT-OWNED BROADBAND NETWORKS

Context, Lessons Learned, and a Way Forward for Policy Makers Cedar Falls Case Study Charles M. Davidson Director, ACLP at New York Law School Michael J. Santorelli Director, ACLP at New York Law School From JUNE 2014
Community based broadband report by Executive Office of the President

THE BENEFITS OF COMPETITION AND CHOICE FOR COMMUNITY DEVELOPMENT AND HIGHSPEED INTERNET ACCESS
REPORT TO THE PRESIDENT ACCELERATING U.S. ADVANCED MANUFACTURING

Executive Office of the President President’s Council of Advisors on Science and Technology
More Related Content
More from Ed Dodds
Innovation Accelerators Report

Innovation Accelerators:
Defining Characteristics Among Startup Assistance Organizations by C. Scott Dempwolf, Jennifer Auer, and
Michelle D’Ippolito
Optimal Solutions Group, LLC
College Park, MD 20740
contract number SBAHQ -13-M-0197
Release Date: October 2014
This report was developed under a contract with the Small Business Administration, Office of Advocacy, and contains information and analysis that were reviewed by officials of the Office of Advocacy. However, the final conclusions of the report do not necessarily reflect the views of the Office of Advocacy.
Strategy for American Innovation

America has long been a nation of innovators. The United States is the birthplace of the Internet, which today connects three billion people around the world. American scientists and engineers sequenced the human genome, invented the semiconductor, and sent humankind to the moon. And America is not done yet. For an advanced economy such as the United States, innovation is a wellspring of economic growth. While many countries can grow by adopting existing technologies and business practices, America must continually innovate because our workers and firms are often operating at the technological frontier. Innovation is also a powerful tool for addressing our most pressing challenges as a nation, such as enabling more Americans to lead longer, healthier lives, and accelerating the transition to a low-carbon economy.
Report to the President and Congress Ensuring Leadership in Federally Funded ...

In the report, PCAST focuses on eight R&D areas: cybersecurity, IT and health, Big Data and data-intensive computing, IT and the physical world, privacy protection, cyber-human systems, high capability computing, and foundational computing research. All of these areas help to achieve the Nation’s priorities. For example, Big Data, IT and the physical world, and high-capability computing are essential contributors to addressing issues within energy and the environment.
Data Act Federal Register Notice Public Summary of Responses

Summary of Responses to the Treasury Bureau of the Fiscal Service Notice in the Federal Register on 9/26/2014 for “Public Input on the Establishment of Financial Data Standards (Data Exchange)
Supporting high throughput high-biotechnologies in today’s research environme...

St. Jude Children’s Research Hospital, Hartwell Center and Molecular Biotechnology, Clayton W. Naeve, Ph.D.
Common Design Elements for Data Movement Eli Dart

Eli Dart, Network Engineer ESnet Science Engagement Lawrence Berkeley National Laboratory Cosmology CrossConnects Workshop Berkeley, CA February 11, 2015
Strategies for Improving the U.S. Payment System

The Federal Reserve believes that the U.S. payment system is at a critical juncture in its evolution. Technology is rapidly changing many elements that support the payment process. High-speed data networks are becoming ubiquitous, computing devices are becoming more sophisticated and mobile, and information is increasingly processed in real time. These capabilities are changing the nature of commerce and end-user expectations for payment services. Meanwhile, payment security and the protection of sensitive data, which are foundational to public confidence in any payment system, are challenged by dynamic, persistent and rapidly escalating threats. Finally, an increasing number of U.S. citizens and businesses routinely transfer value across borders and demand better payment options to swiftly and efficiently do so.
Experiences In Building Globus Genomics Using Galaxy, Globus Online and AWS

Ravi K Madduri
University of Chicago and ANL
UNDERSTANDING THE DEBATE OVER GOVERNMENT-OWNED BROADBAND NETWORKS

Context, Lessons Learned, and a Way Forward for Policy Makers Cedar Falls Case Study Charles M. Davidson Director, ACLP at New York Law School Michael J. Santorelli Director, ACLP at New York Law School From JUNE 2014
Community based broadband report by Executive Office of the President

THE BENEFITS OF COMPETITION AND CHOICE FOR COMMUNITY DEVELOPMENT AND HIGHSPEED INTERNET ACCESS
REPORT TO THE PRESIDENT ACCELERATING U.S. ADVANCED MANUFACTURING

Executive Office of the President President’s Council of Advisors on Science and Technology
More from Ed Dodds (20)
AppImpact: A Framework for Mobile Technology in Behavioral Healthcare

AppImpact: A Framework for Mobile Technology in Behavioral Healthcare
Report to the President and Congress Ensuring Leadership in Federally Funded ...

Report to the President and Congress Ensuring Leadership in Federally Funded ...
Data Act Federal Register Notice Public Summary of Responses

Data Act Federal Register Notice Public Summary of Responses
2014 COMPENDIUM Edition of National Research and Education Networks in Europe

2014 COMPENDIUM Edition of National Research and Education Networks in Europe
Supporting high throughput high-biotechnologies in today’s research environme...

Supporting high throughput high-biotechnologies in today’s research environme...
Nationwide Interoperability Roadmap draft version 1.0

Nationwide Interoperability Roadmap draft version 1.0
Experiences In Building Globus Genomics Using Galaxy, Globus Online and AWS

Experiences In Building Globus Genomics Using Galaxy, Globus Online and AWS
UNDERSTANDING THE DEBATE OVER GOVERNMENT-OWNED BROADBAND NETWORKS

UNDERSTANDING THE DEBATE OVER GOVERNMENT-OWNED BROADBAND NETWORKS
Community based broadband report by Executive Office of the President

Community based broadband report by Executive Office of the President
REPORT TO THE PRESIDENT ACCELERATING U.S. ADVANCED MANUFACTURING

REPORT TO THE PRESIDENT ACCELERATING U.S. ADVANCED MANUFACTURING
Recently uploaded
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

# Internet Security: Safeguarding Your Digital World
In the contemporary digital age, the internet is a cornerstone of our daily lives. It connects us to vast amounts of information, provides platforms for communication, enables commerce, and offers endless entertainment. However, with these conveniences come significant security challenges. Internet security is essential to protect our digital identities, sensitive data, and overall online experience. This comprehensive guide explores the multifaceted world of internet security, providing insights into its importance, common threats, and effective strategies to safeguard your digital world.
## Understanding Internet Security
Internet security encompasses the measures and protocols used to protect information, devices, and networks from unauthorized access, attacks, and damage. It involves a wide range of practices designed to safeguard data confidentiality, integrity, and availability. Effective internet security is crucial for individuals, businesses, and governments alike, as cyber threats continue to evolve in complexity and scale.
### Key Components of Internet Security
1. **Confidentiality**: Ensuring that information is accessible only to those authorized to access it.
2. **Integrity**: Protecting information from being altered or tampered with by unauthorized parties.
3. **Availability**: Ensuring that authorized users have reliable access to information and resources when needed.
## Common Internet Security Threats
Cyber threats are numerous and constantly evolving. Understanding these threats is the first step in protecting against them. Some of the most common internet security threats include:
### Malware
Malware, or malicious software, is designed to harm, exploit, or otherwise compromise a device, network, or service. Common types of malware include:
- **Viruses**: Programs that attach themselves to legitimate software and replicate, spreading to other programs and files.
- **Worms**: Standalone malware that replicates itself to spread to other computers.
- **Trojan Horses**: Malicious software disguised as legitimate software.
- **Ransomware**: Malware that encrypts a user's files and demands a ransom for the decryption key.
- **Spyware**: Software that secretly monitors and collects user information.
### Phishing
Phishing is a social engineering attack that aims to steal sensitive information such as usernames, passwords, and credit card details. Attackers often masquerade as trusted entities in email or other communication channels, tricking victims into providing their information.
### Man-in-the-Middle (MitM) Attacks
MitM attacks occur when an attacker intercepts and potentially alters communication between two parties without their knowledge. This can lead to the unauthorized acquisition of sensitive information.
### Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Talk presented at Kubernetes Community Day, New York, May 2024.
Technical summary of Multi-Cluster Kubernetes Networking architectures with focus on 4 key topics.
1) Key patterns for Multi-cluster architectures
2) Architectural comparison of several OSS/ CNCF projects to address these patterns
3) Evolution trends for the APIs of these projects
4) Some design recommendations & guidelines for adopting/ deploying these solutions.
This 7-second Brain Wave Ritual Attracts Money To You.!

Discover the power of a simple 7-second brain wave ritual that can attract wealth and abundance into your life. By tapping into specific brain frequencies, this technique helps you manifest financial success effortlessly. Ready to transform your financial future? Try this powerful ritual and start attracting money today!
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Brad Spiegel Macon GA’s journey exemplifies the profound impact that one individual can have on their community. Through his unwavering dedication to digital inclusion, he’s not only bridging the gap in Macon but also setting an example for others to follow.
一比一原版(CSU毕业证)加利福尼亚州立大学毕业证成绩单专业办理

CSU毕业证原版定制【微信:176555708】【加利福尼亚州立大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
The+Prospects+of+E-Commerce+in+China.pptx

The Prospects of E-commerce in China,www.cfye-commerce.shop
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

Ellisha Heppner, Grant Management Lead, presented an update on APNIC Foundation to the PNG DNS Forum held from 6 to 10 May, 2024 in Port Moresby, Papua New Guinea.
一比一原版(LBS毕业证)伦敦商学院毕业证成绩单专业办理

LBS毕业证原版定制【微信:176555708】【伦敦商学院毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
一比一原版(SLU毕业证)圣路易斯大学毕业证成绩单专业办理

SLU毕业证原版定制【微信:176555708】【圣路易斯大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
1.Wireless Communication System_Wireless communication is a broad term that i...

Wireless communication involves the transmission of information over a distance without the help of wires, cables or any other forms of electrical conductors.
Wireless communication is a broad term that incorporates all procedures and forms of connecting and communicating between two or more devices using a wireless signal through wireless communication technologies and devices.
Features of Wireless Communication
The evolution of wireless technology has brought many advancements with its effective features.
The transmitted distance can be anywhere between a few meters (for example, a television's remote control) and thousands of kilometers (for example, radio communication).
Wireless communication can be used for cellular telephony, wireless access to the internet, wireless home networking, and so on.
Recently uploaded (20)
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
Internet-Security-Safeguarding-Your-Digital-World (1).pptx

Internet-Security-Safeguarding-Your-Digital-World (1).pptx
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines
This 7-second Brain Wave Ritual Attracts Money To You.!

This 7-second Brain Wave Ritual Attracts Money To You.!
test test test test testtest test testtest test testtest test testtest test ...

test test test test testtest test testtest test testtest test testtest test ...
Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx

Bridging the Digital Gap Brad Spiegel Macon, GA Initiative.pptx
APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024

APNIC Foundation, presented by Ellisha Heppner at the PNG DNS Forum 2024
1.Wireless Communication System_Wireless communication is a broad term that i...

1.Wireless Communication System_Wireless communication is a broad term that i...
ILSR 2019 12 rural coop policy brief update page 8
- 1. 8
