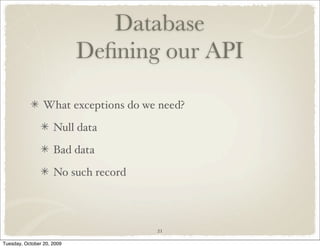
The document is a tutorial about designing and implementing a wiki database and application using Howdah. It discusses designing the database and application, defining API contracts, adding user authentication and authorization features including administrative users, and adding a new feature to the user profile page to list pages edited by each user. Security, permissions, and data confidentiality are important considerations throughout the design process.