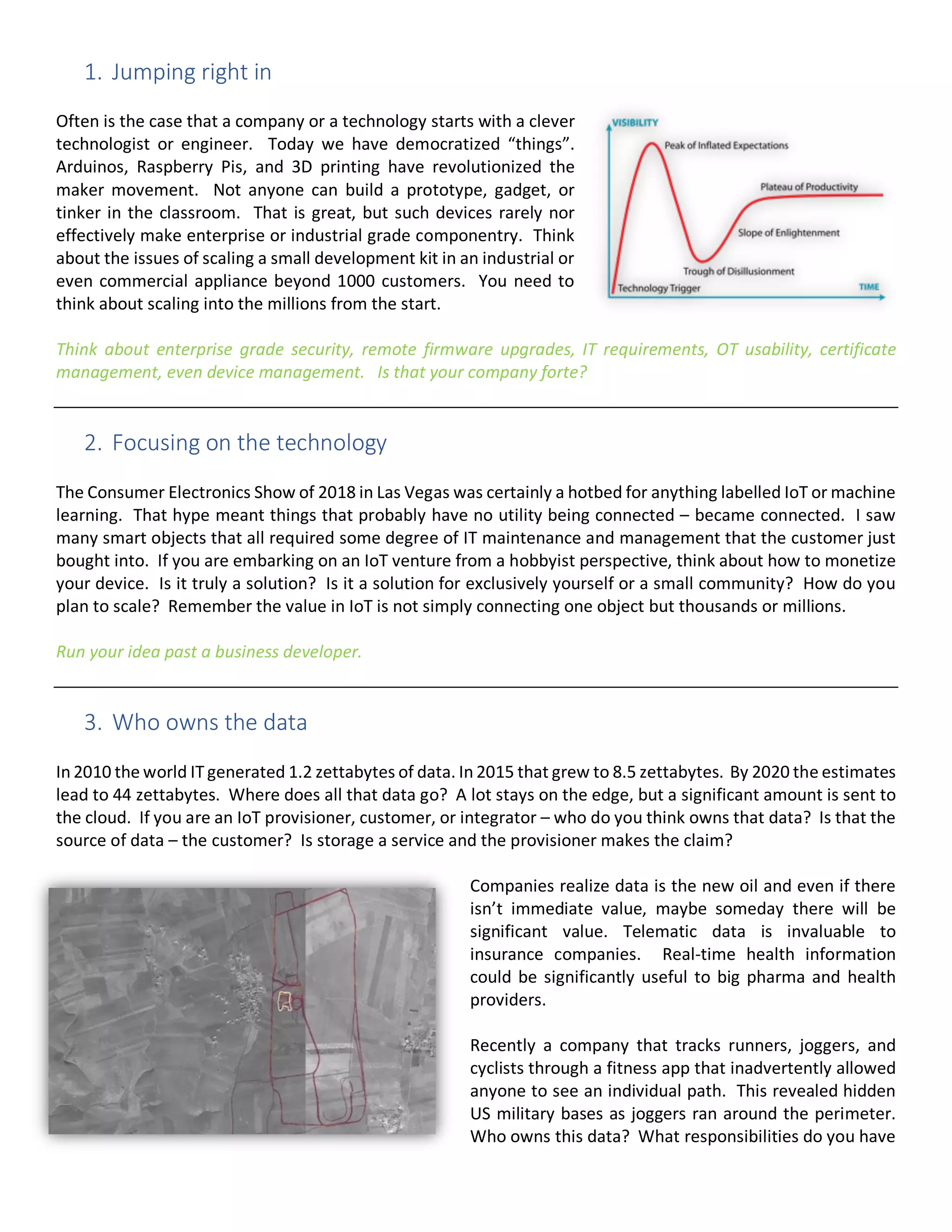
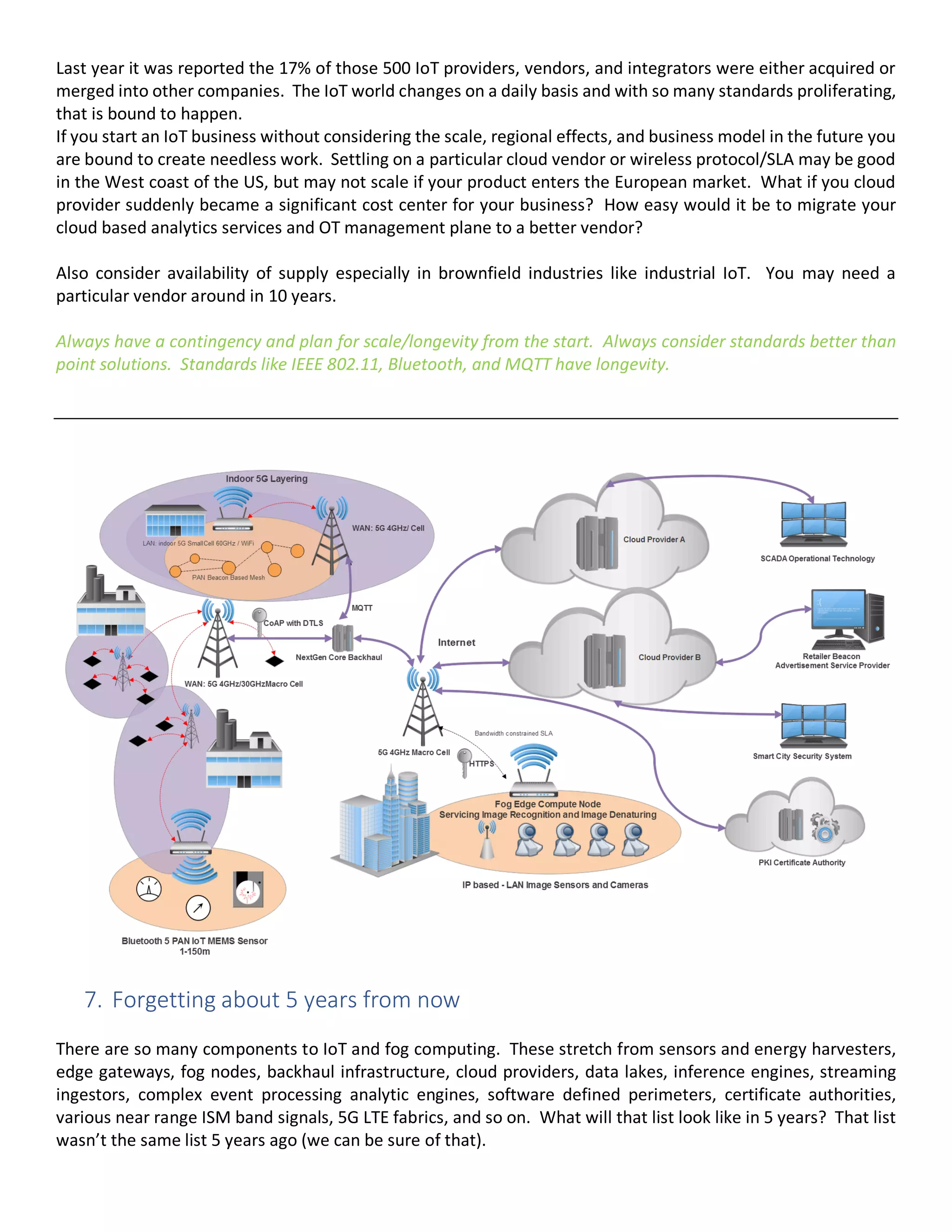
The document discusses the burgeoning landscape of IoT, highlighting both the vast opportunities and significant pitfalls entrepreneurs may face. It outlines eight key ways to fail in the IoT business, including poor security measures, data ownership issues, and focusing too much on technology rather than practical solutions. The author emphasizes the importance of planning for scalability, security, and understanding the hidden costs associated with IoT implementations.