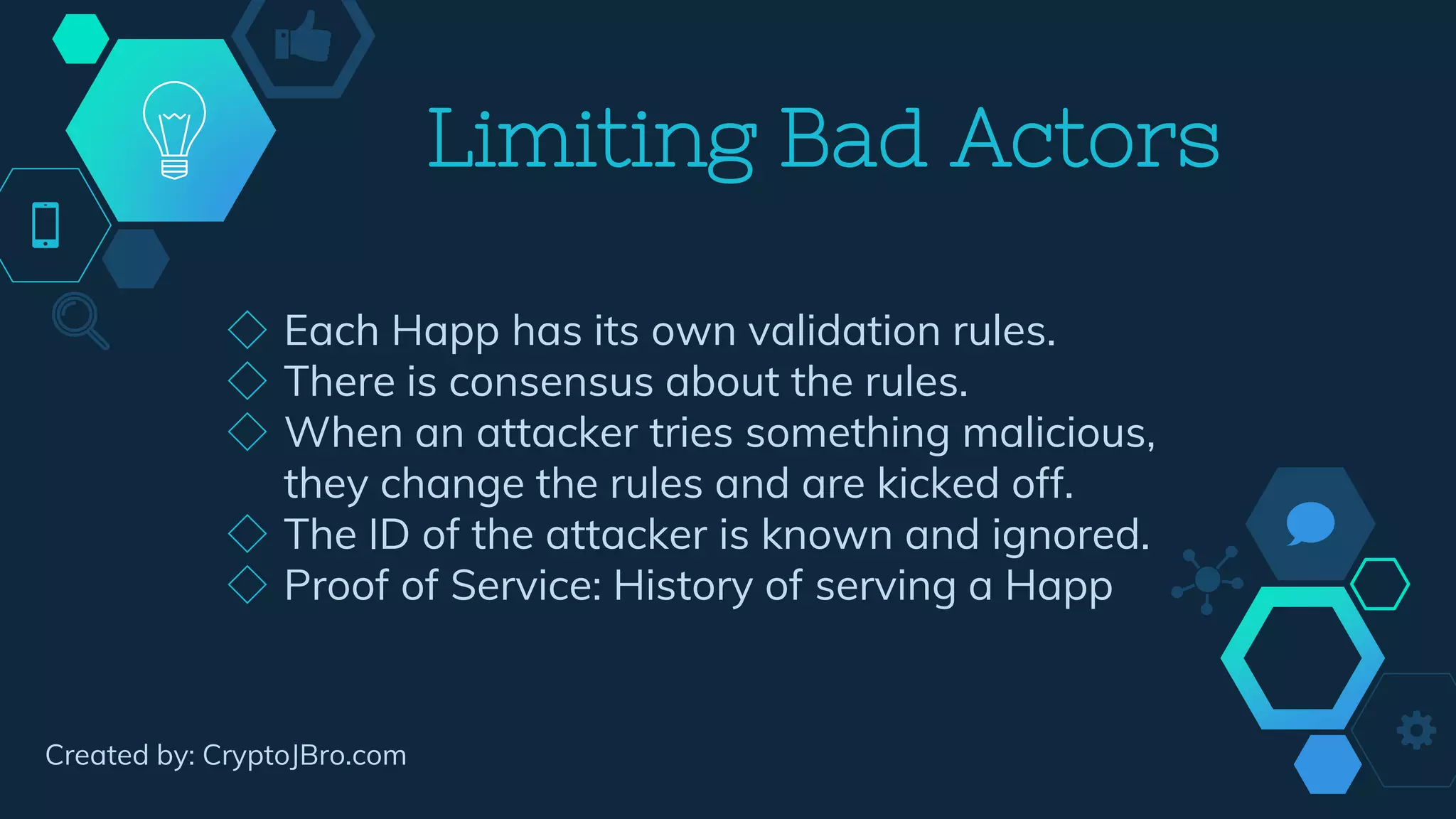
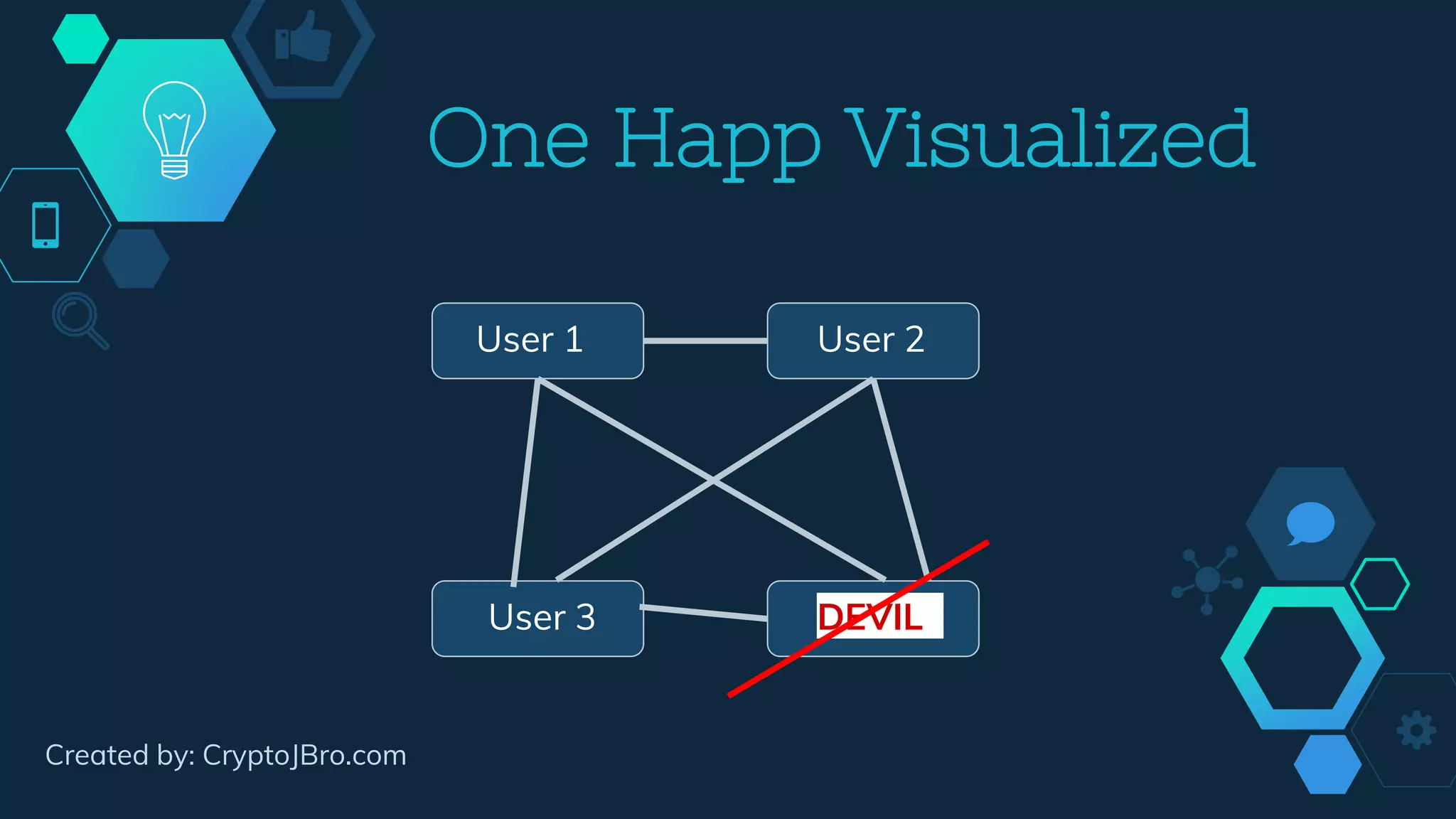
Holochain is a decentralized application framework that utilizes a peer-to-peer network where each app (happ) operates on its own unique DNA. Users maintain individual, tamper-proof histories and validate data without requiring the entire network's consensus, making it scalable and secure. Key features include user data ownership, identity security, and mechanisms to limit bad actors through consensus rules and an immune system of random validations.