Embed presentation
Downloaded 23 times
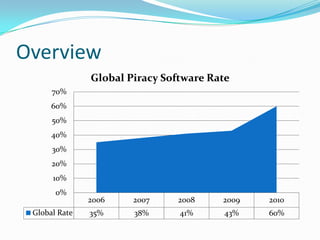

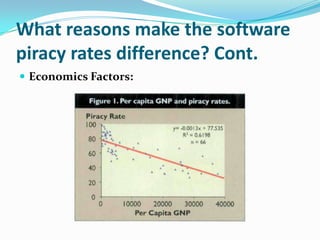
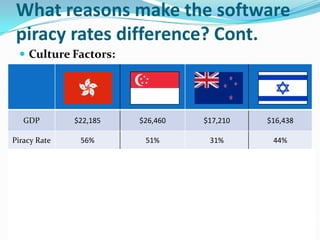
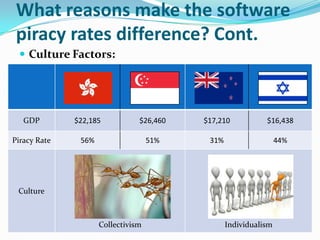

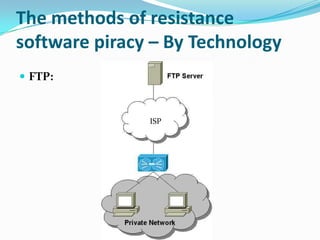
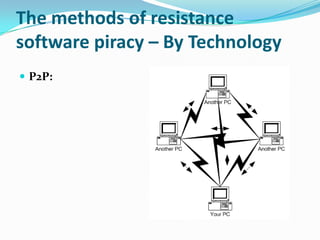
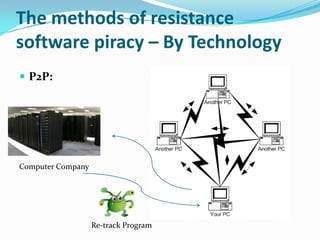

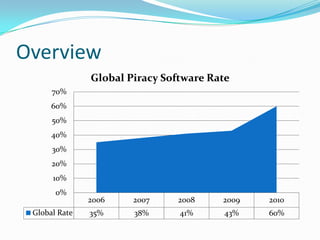
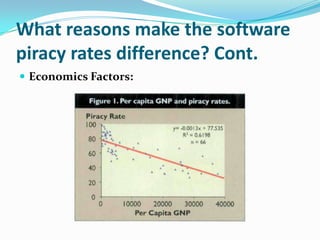
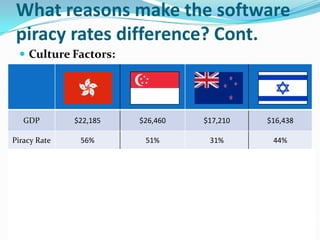
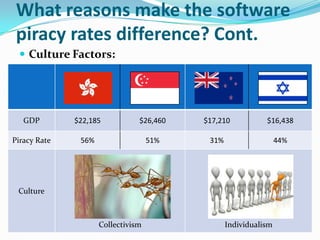
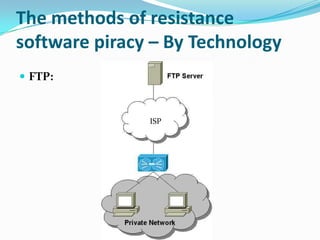
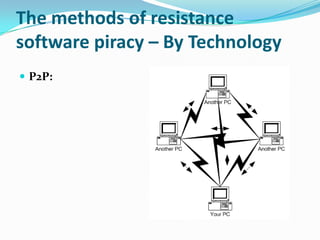
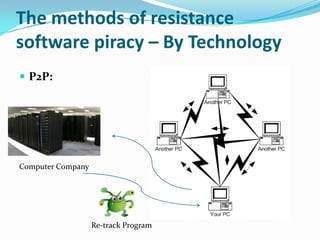
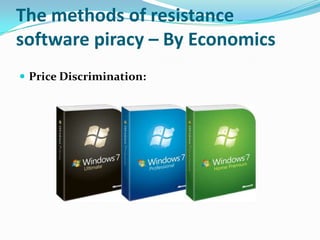
This document discusses factors that influence software piracy rates and methods to reduce piracy. It examines economic, cultural, technical, and regulatory reasons for differences in piracy rates. It also outlines technological approaches like online monitoring of auctions and peer-to-peer networks and economic strategies such as price discrimination and increased user support that can help combat software piracy.