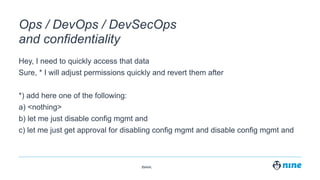
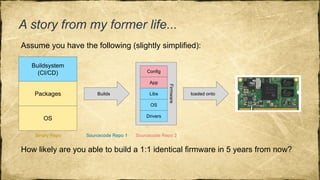
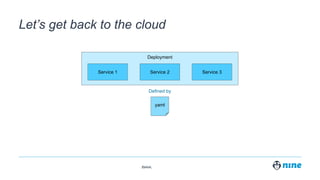
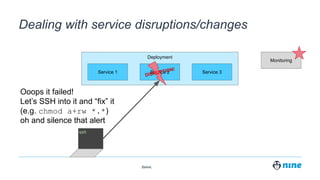
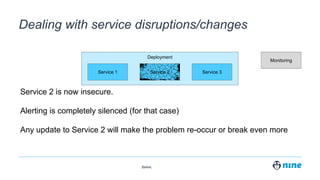
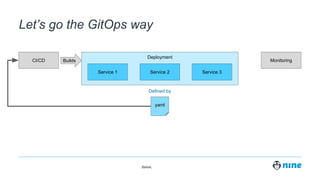
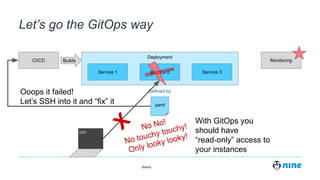
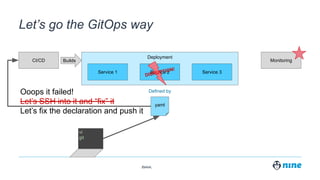
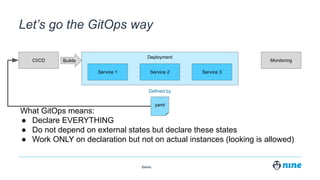
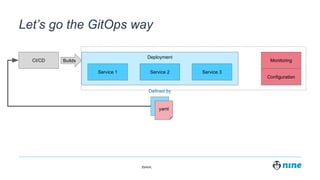
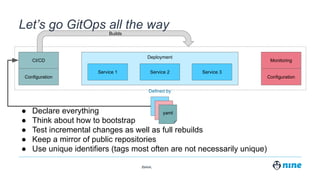
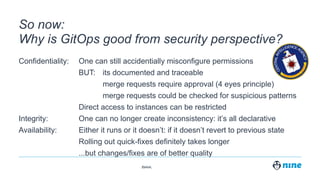
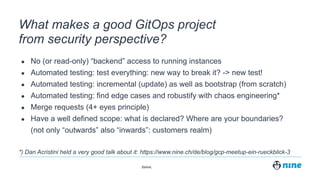
The document discusses the integration of GitOps in enhancing security within DevOps practices, emphasizing the principles of confidentiality, integrity, and availability. It highlights best practices such as the necessity of declaring all states, restricting direct instance access, and employing automated testing to improve the resilience and traceability of changes. The effectiveness of GitOps is framed through its ability to document changes and implement approval processes to prevent misconfigurations and inconsistencies.