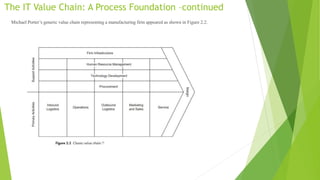
This document discusses IT service management frameworks and the IT value chain. It provides an overview of several frameworks, including COBIT, CMMI, and ITIL. These frameworks take process-centric approaches but do not define the core value-adding process for IT. The document proposes that IT can be viewed as having its own value chain of plan, build, and run activities. It presents a conceptual data model and systems architecture to support the IT value chain. Design patterns are also discussed as general solutions to common problems in areas like the core value chain and IT enablement.





























![Patterns for IT Enablement
In software engineering, a design pattern is a general solution to a common
problem…. A design pattern isn’t a finished design that can be transformed
directly into [program] code; it is a description or template for how to solve a
problem that can be used in many different situations.](https://image.slidesharecdn.com/enterprisearchitecture-230508103616-a23e4ee0/85/Enterprise-Architecture-pptx-31-320.jpg)

