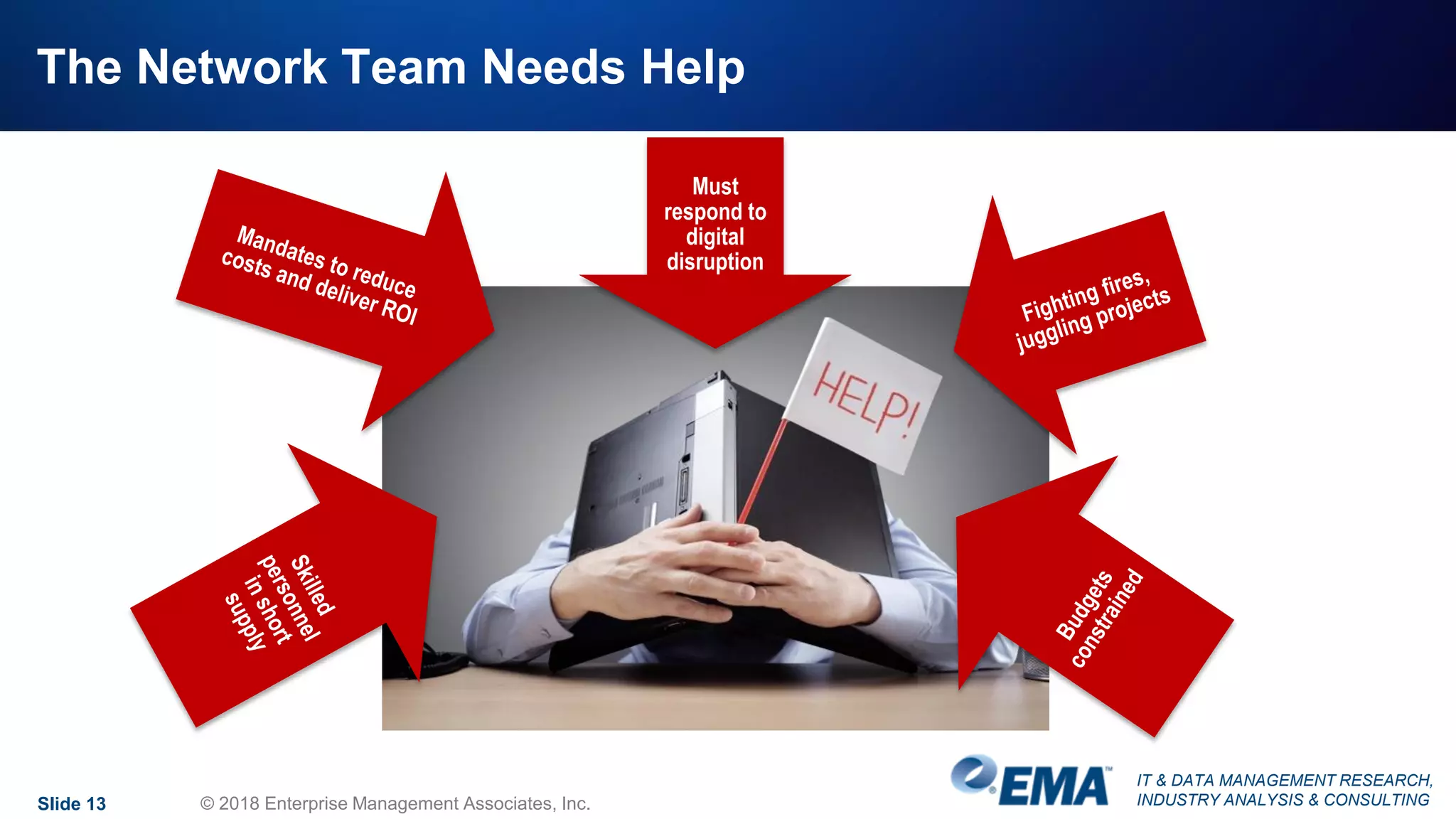
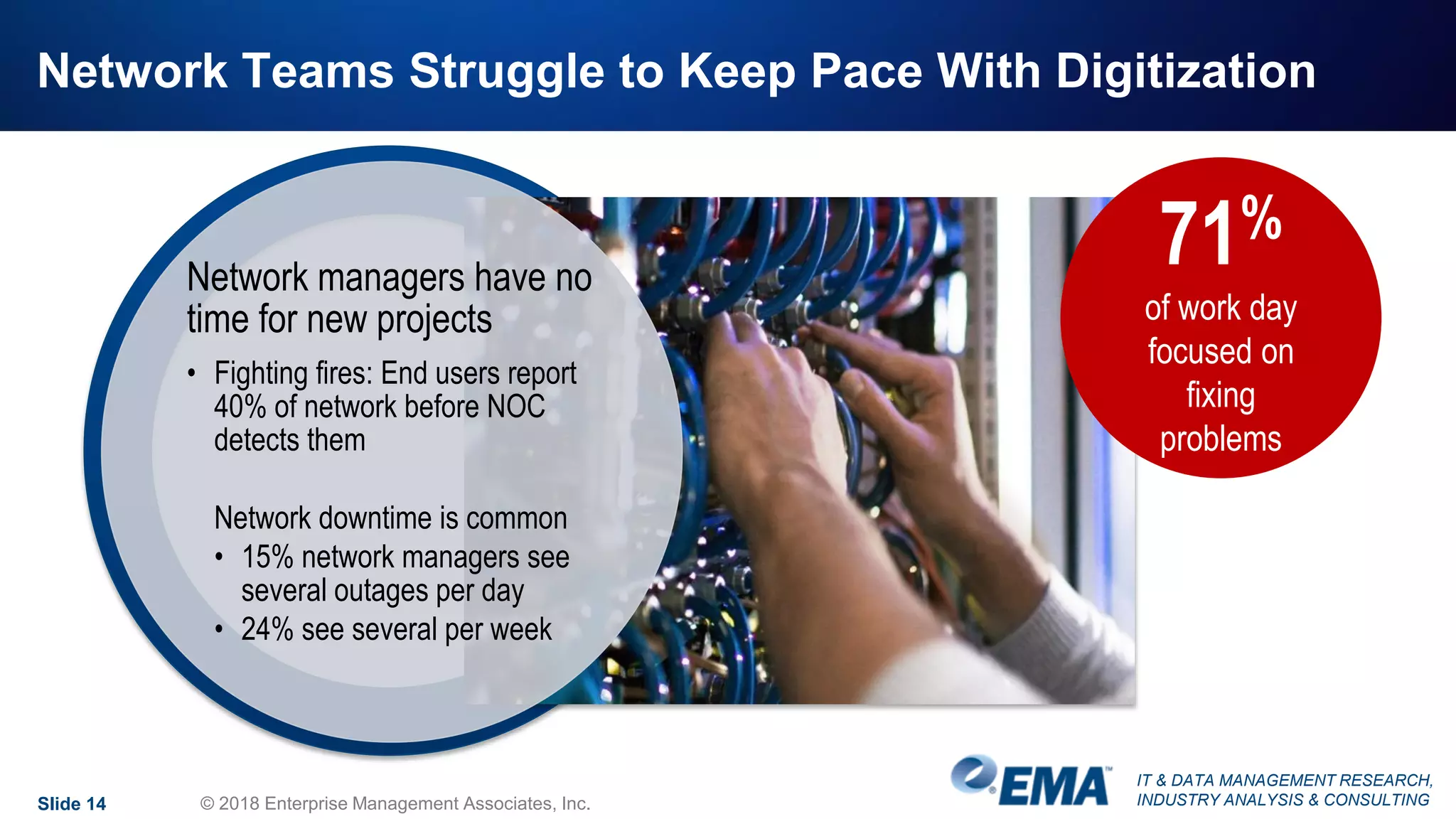
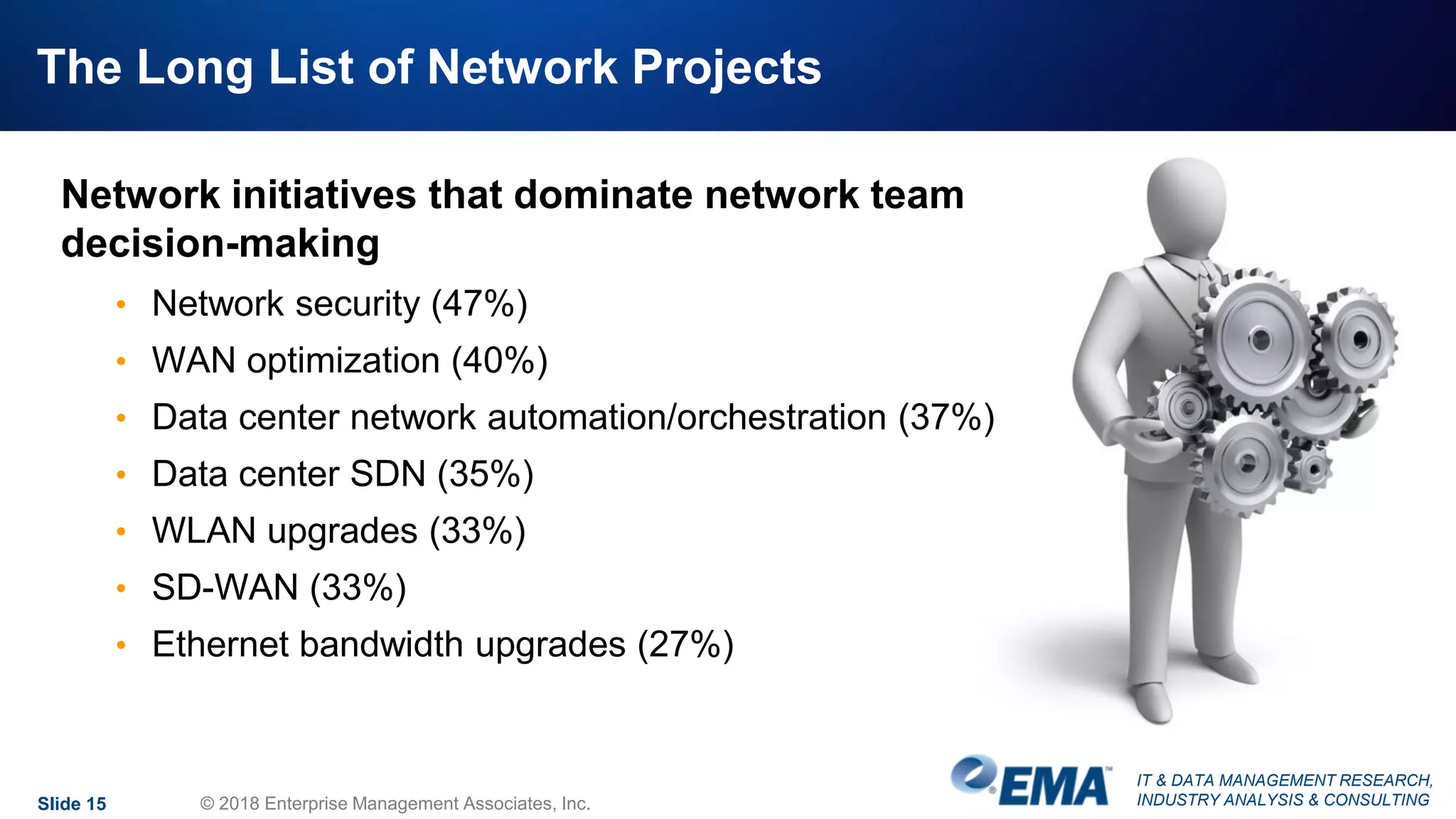
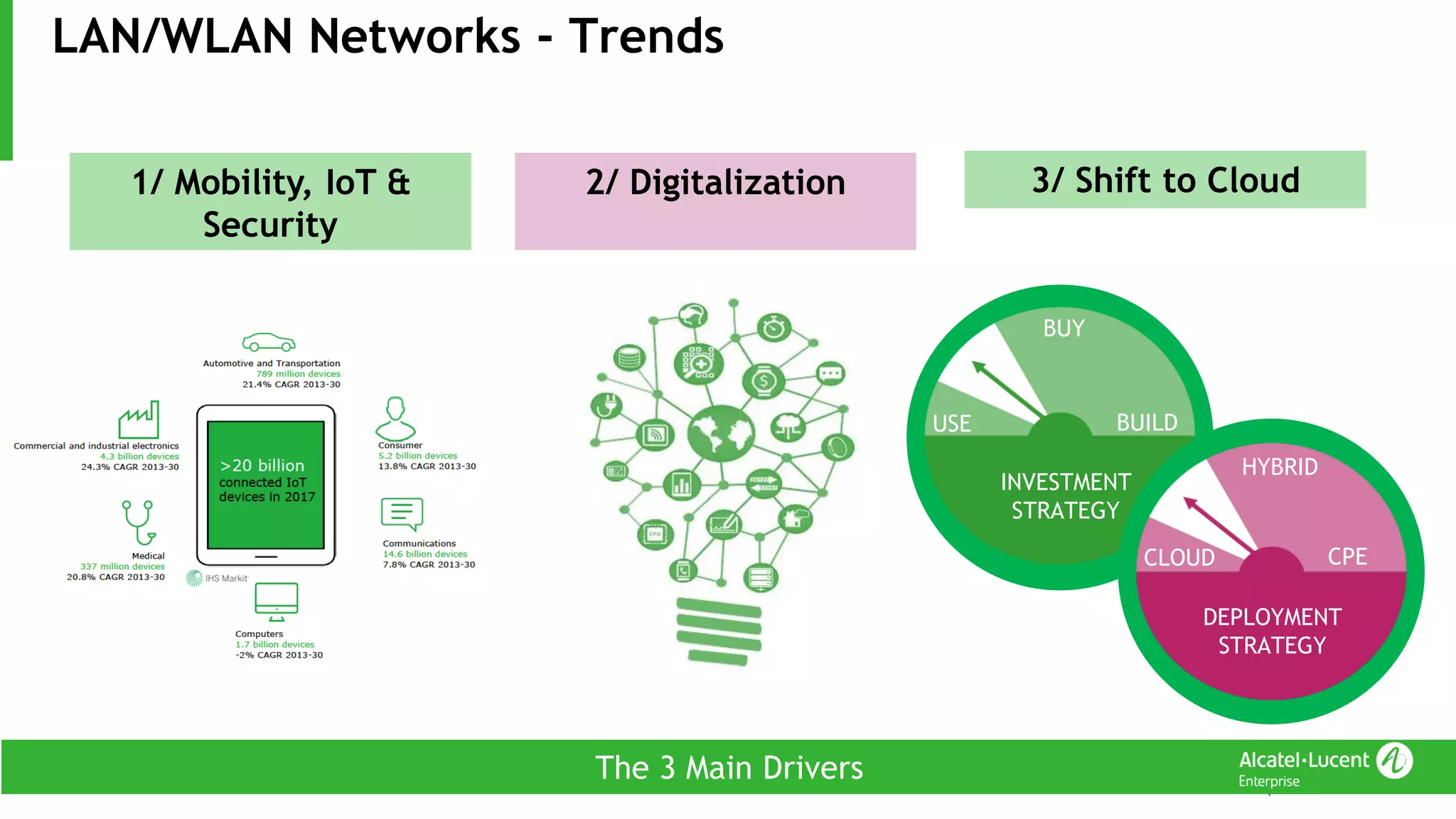
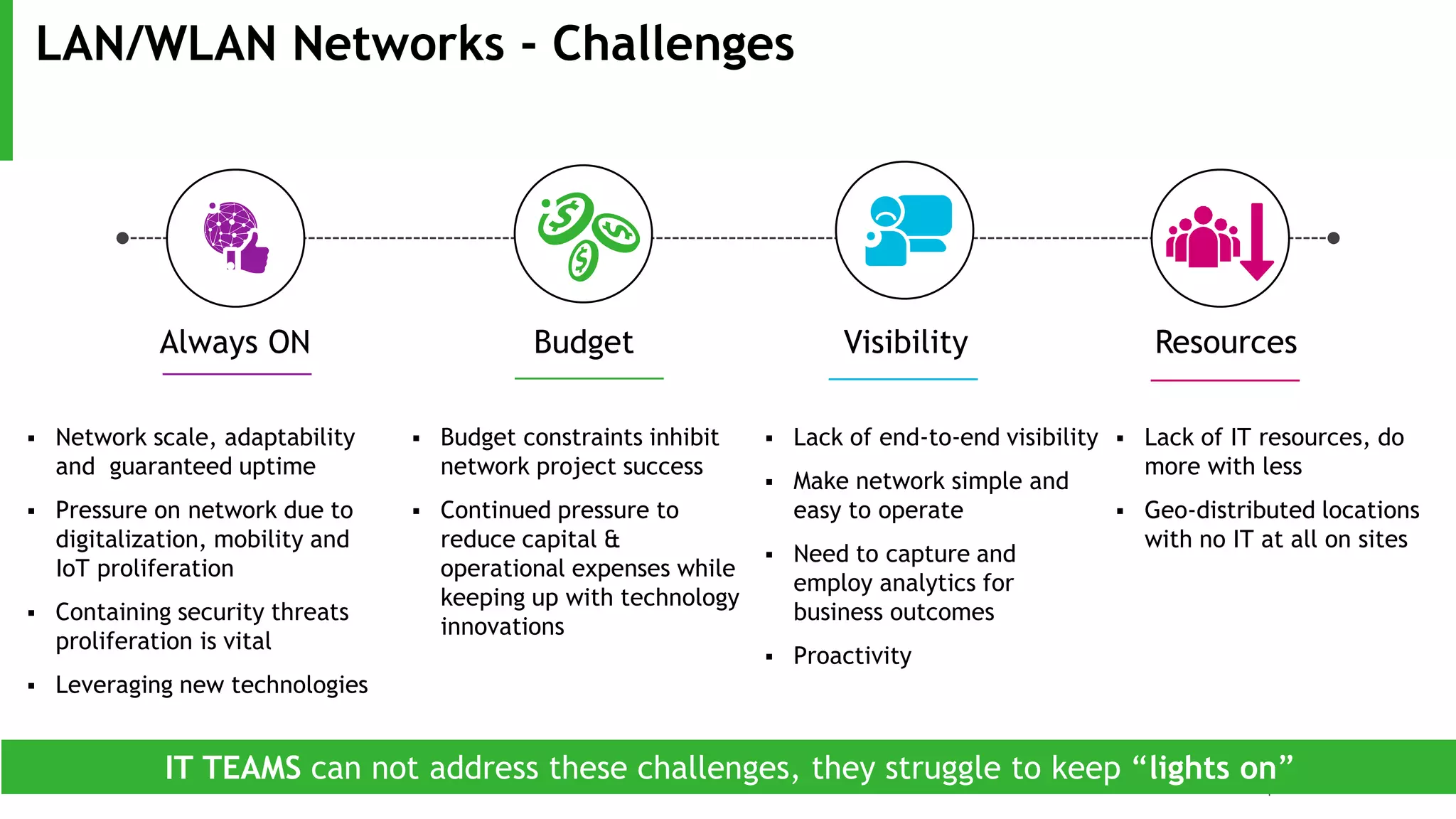
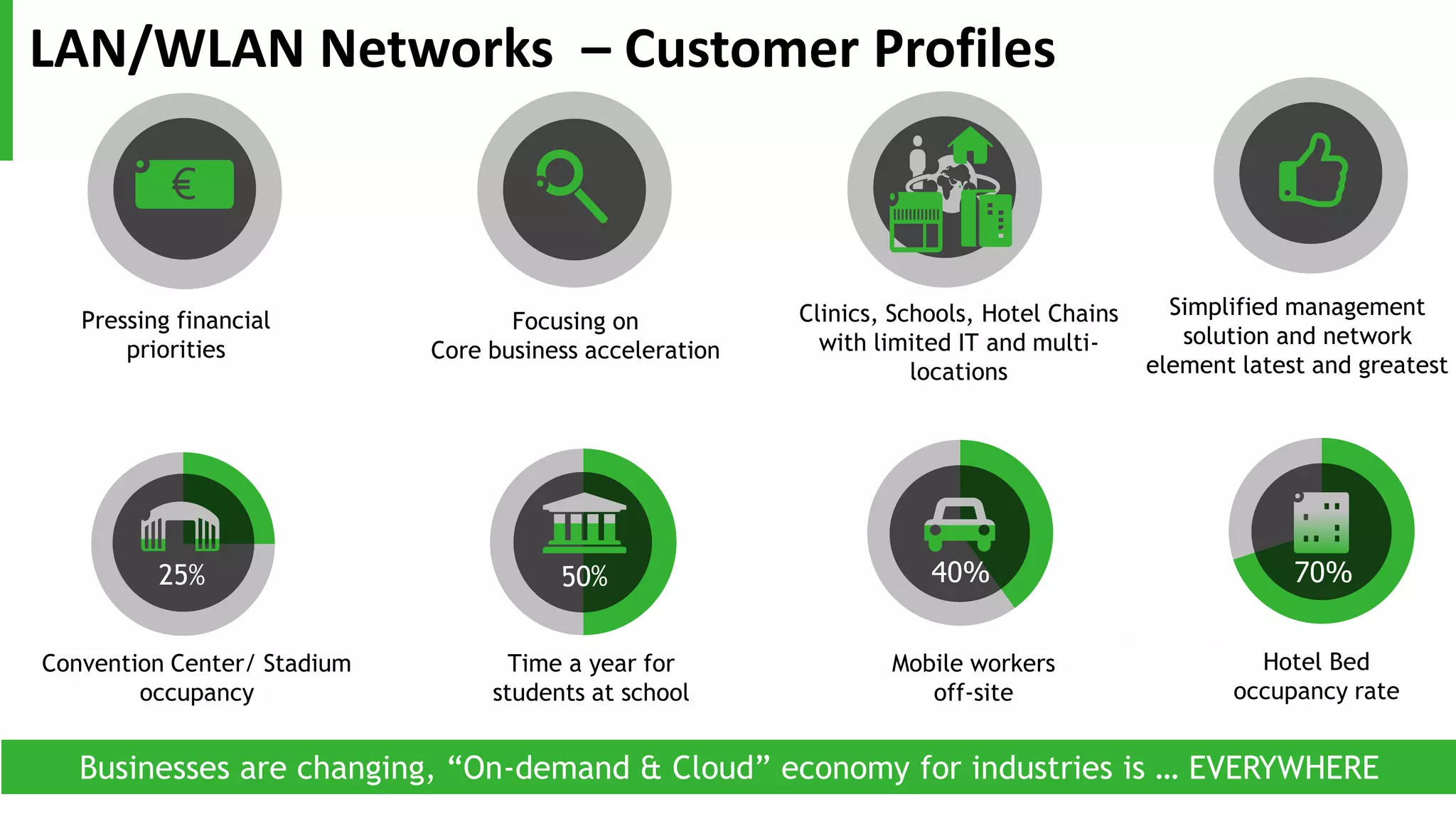
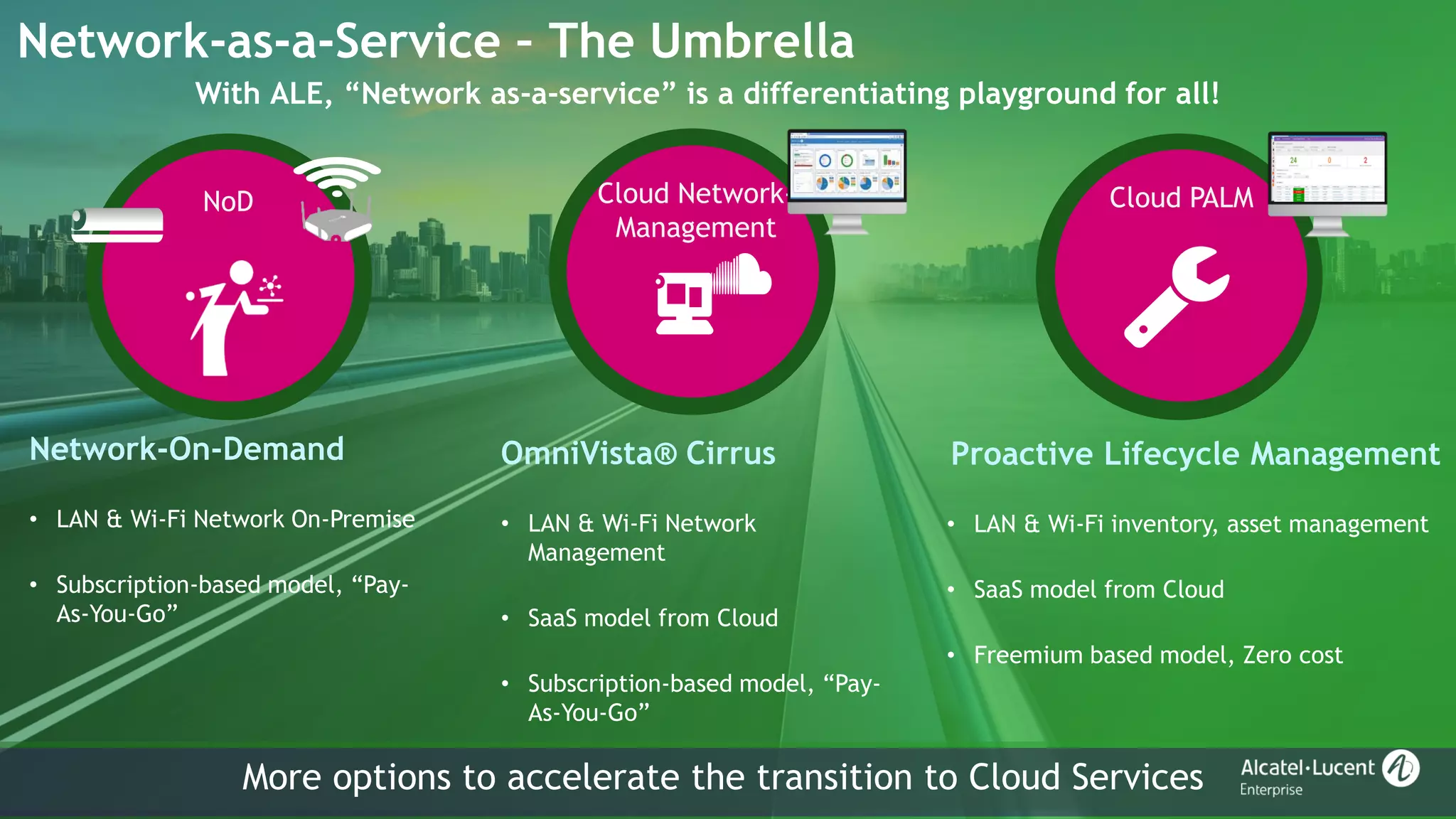
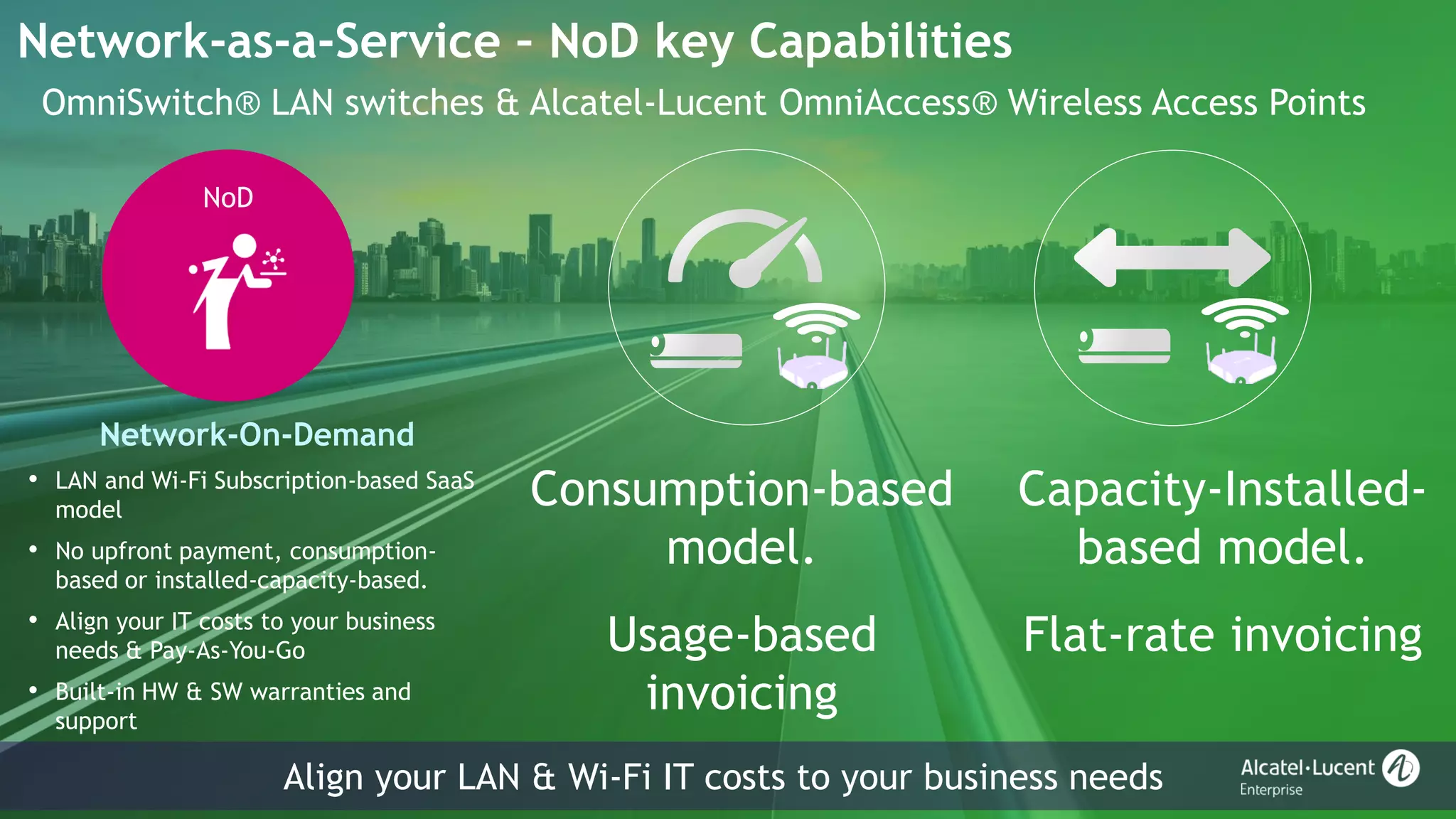
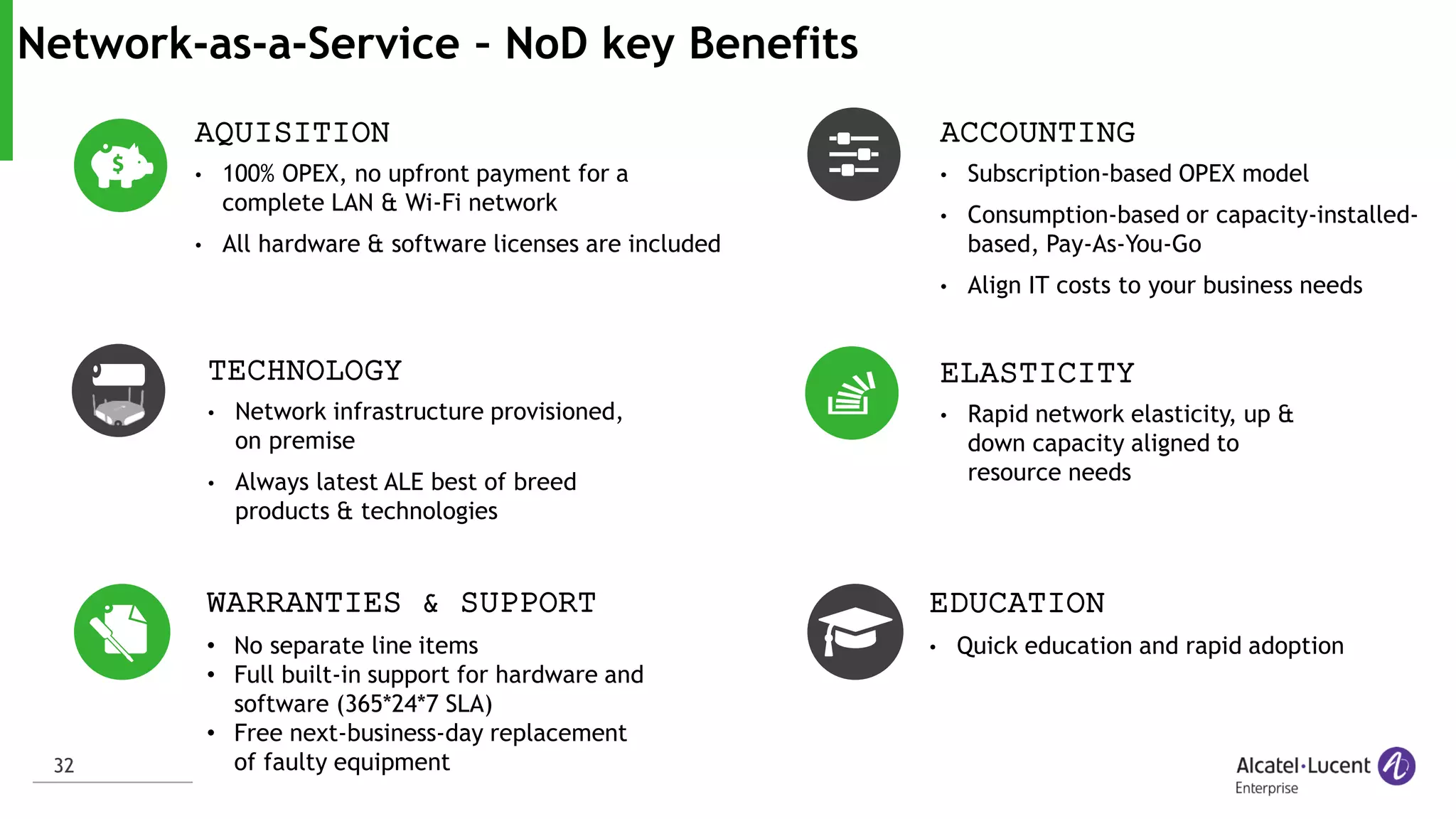
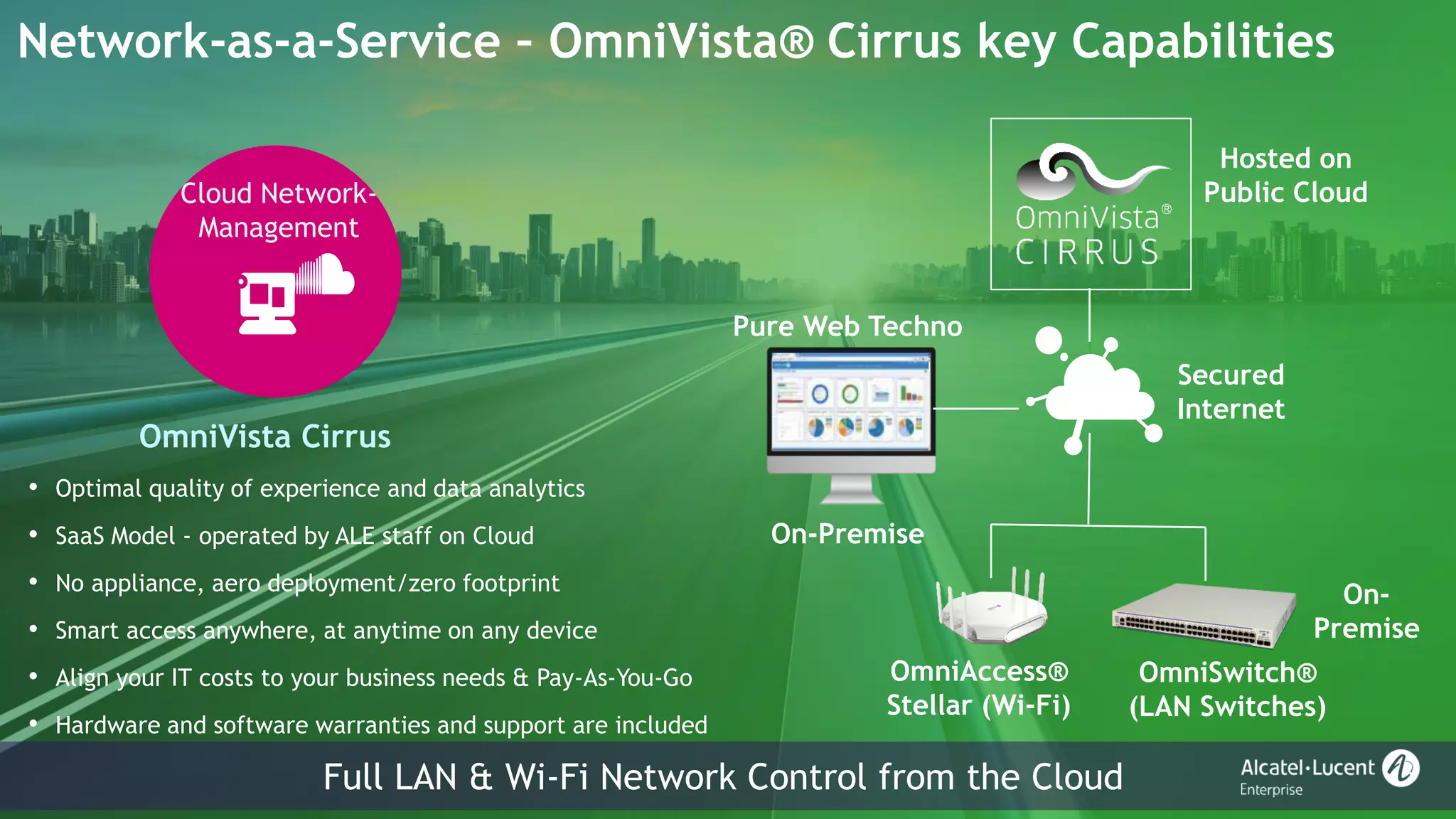
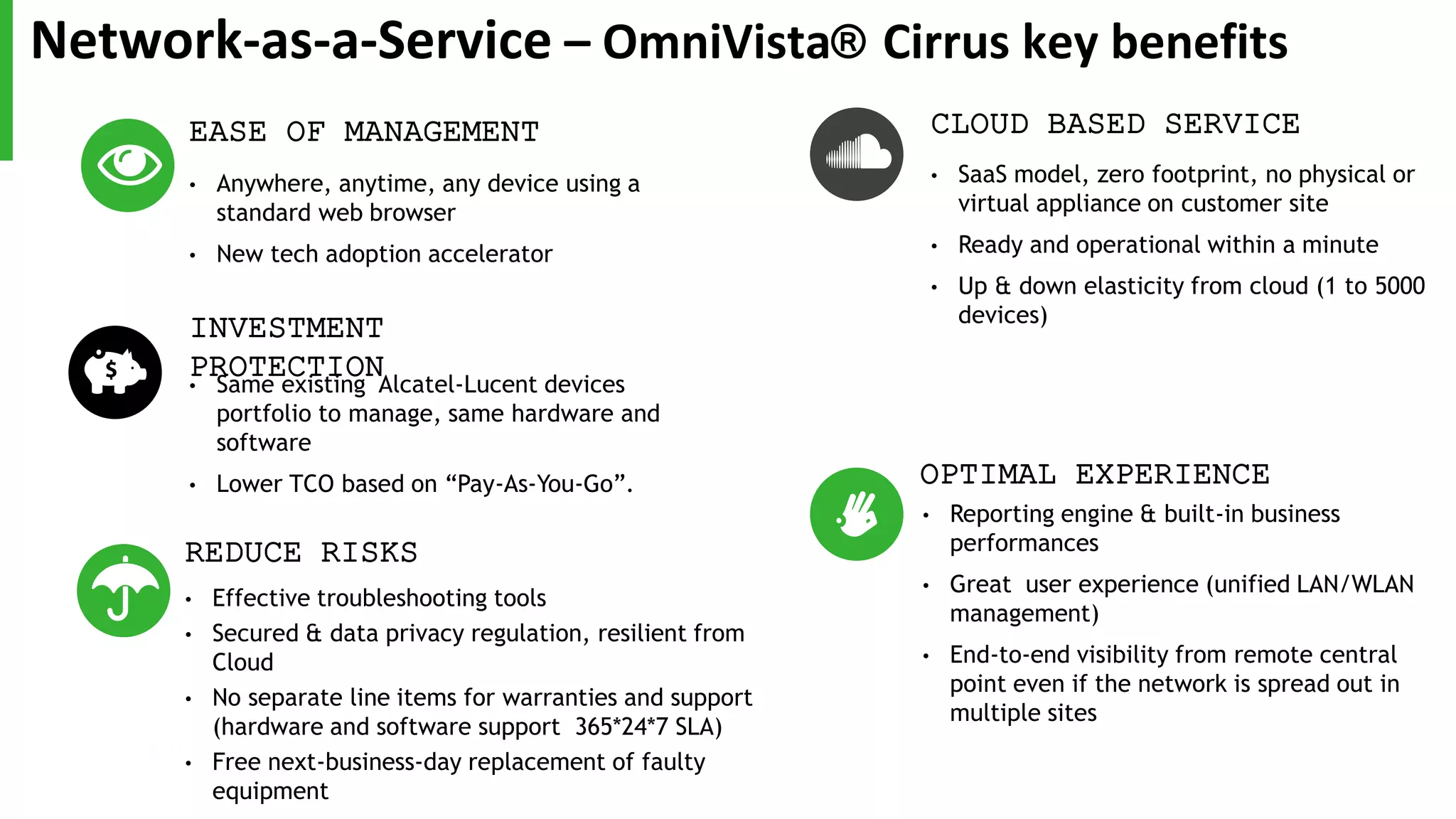
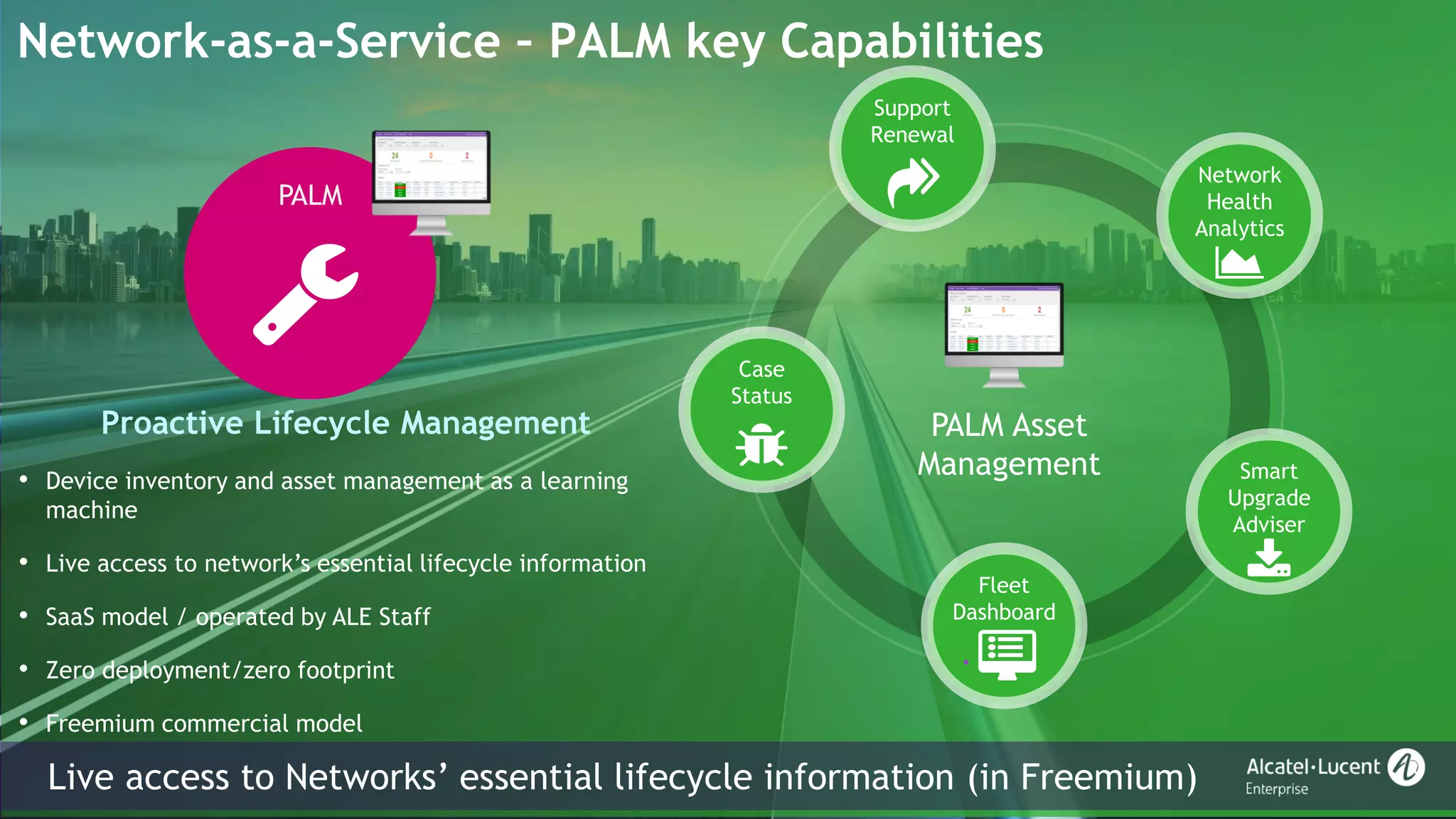
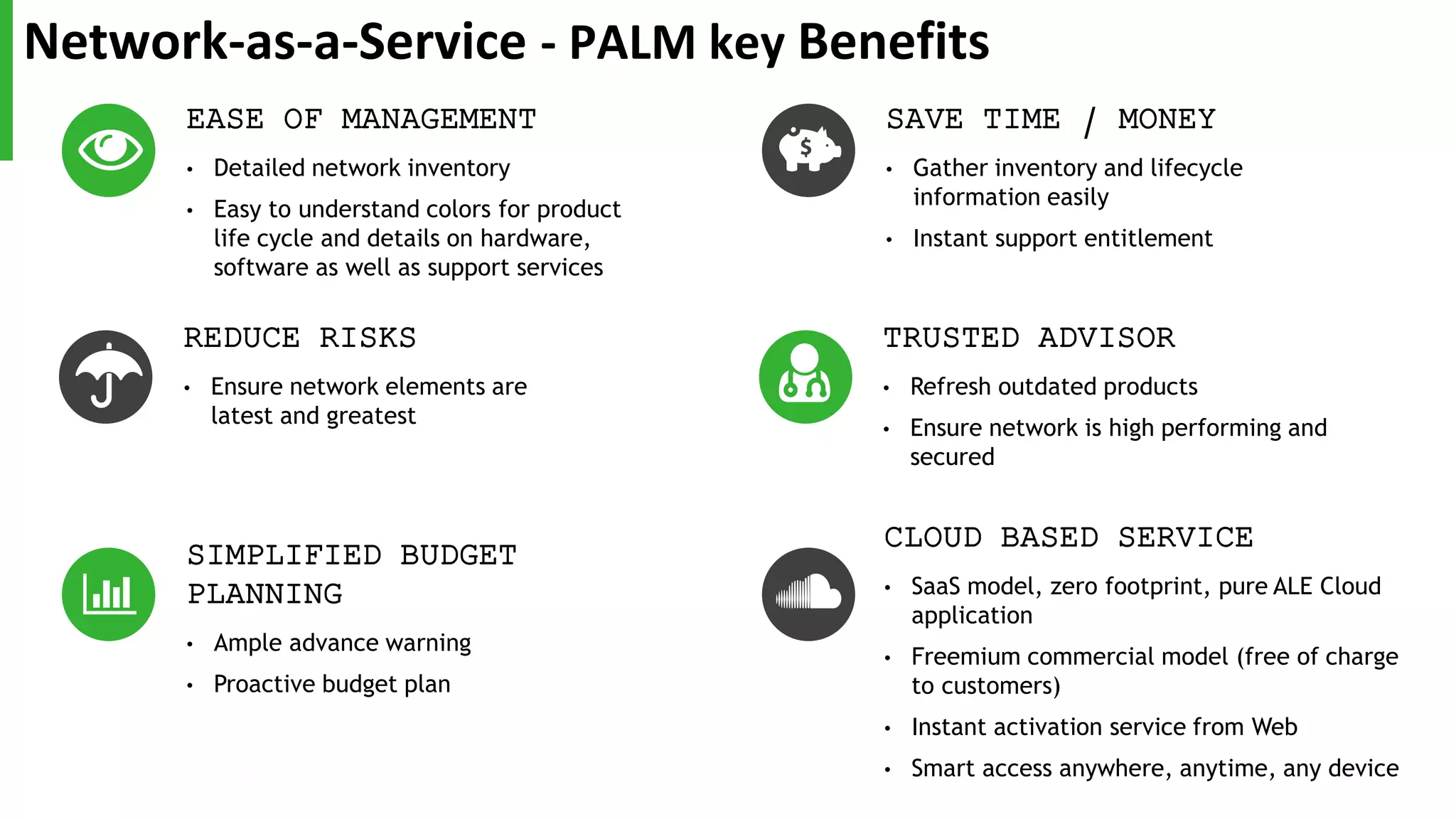
The document discusses Alcatel-Lucent Enterprise's Network-as-a-Service (NaaS) solution which aims to enable digital transformation by offering a flexible, subscription-based model for network infrastructure. It highlights the challenges faced by network teams due to the rapid adoption of digital technologies like IoT, mobility, and cloud, leading to increased demands on network management. NaaS is presented as a solution to ease these challenges by shifting costs from capital expenditure (CapEx) to operational expenditure (OpEx), streamlining management, and allowing for faster adoption of new technologies.