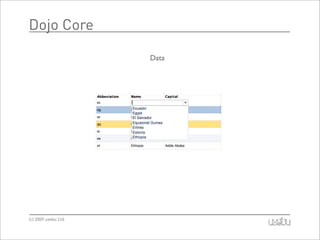
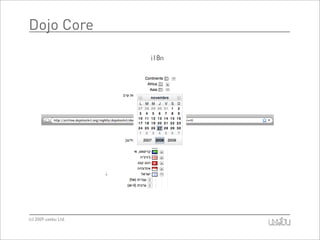
The document provides an overview of the Dojo Toolkit, detailing its history, core functionalities, and various components such as Dijit and DojoX. It emphasizes the toolkit's capabilities in JavaScript development, including content manipulation, event handling, and AJAX communication. The presentation appears to be aimed at developers interested in leveraging Dojo for enhanced web application usability and performance.