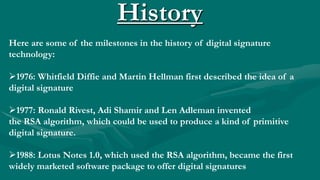
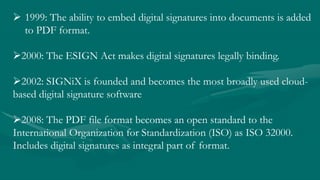
Digital signatures provide authentication, integrity, and non-repudiation for electronic documents. They work by using public key cryptography - a signer encrypts a hash of a message with their private key, which can be verified by anyone using the signer's public key. Major milestones in digital signatures include the invention of the RSA algorithm in 1977 and laws passed in 2000 and 2008 that gave digital signatures legal standing. While they provide security, key security and processing times are challenges.