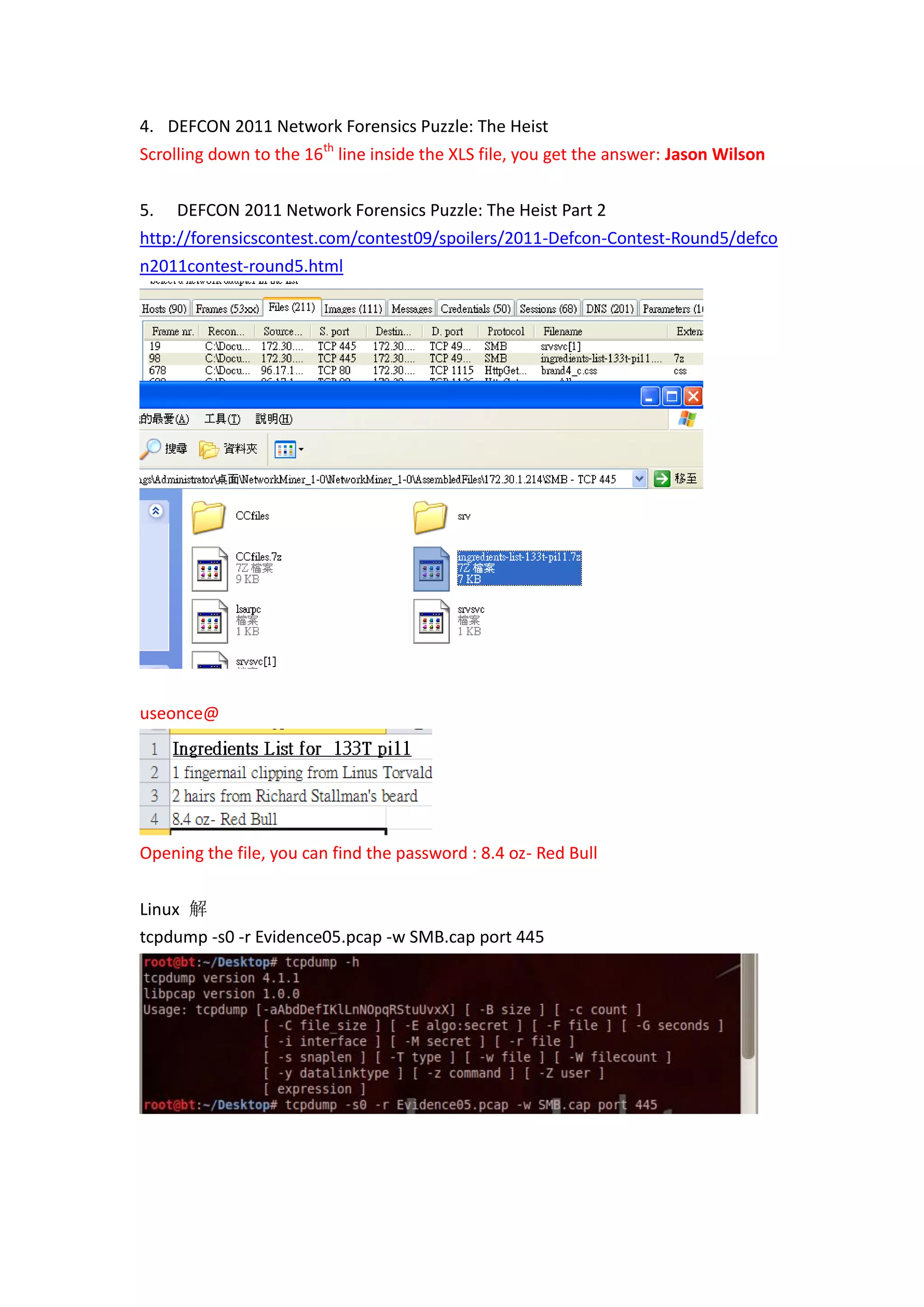
This document discusses network forensics puzzles from DEFCON 2011. It provides instructions and solutions for 5 puzzles involving analyzing packet captures to find hidden clues and passwords. Key steps included using tools like tcpdump, tcpflow, foremost, grep, and NetworkMiner to extract files and identify hosts, protocols, and network activity that revealed the solutions.





![改用 xplico , xplico GUI 不 work
usage: xplico [-v] [-c <config_file>] [-h] [-g] [-l] [-i <prot>] -m <capute_module>
-v version
-c config file
-h this help
-i info of protocol 'prot'
-g display graph-tree of protocols
-l print all log in the screen
-m capture type module
NOTE: parameters MUST respect this order!
./xplico -m pcap -f /root/Desktop/Evidence03.pcap](https://image.slidesharecdn.com/defcon2011networkforensics-111118134244-phpapp01/75/Defcon-2011-network-forensics-6-2048.jpg)
![ip 74.125.127.126 是 google 的 所以可以猜到是用 googlechat voip call
所以可以用 videosnarf 来解看看
videosnarf
http://ucsniff.sourceforge.net/videosnarf.html
root@bt:/usr/local/bin# videosnarf -h
Starting videosnarf 0.63
Usage: videosnarf [-i input pcap file] [-f filter expression]
-i <input pcap file> (Mandatory) input pcap file
-o <output file> (Optional) output base name file
-f <filter expression> (Optional) pcap filter expression
-k <g726 sample size> (Optional) G726 sameple size](https://image.slidesharecdn.com/defcon2011networkforensics-111118134244-phpapp01/75/Defcon-2011-network-forensics-7-2048.jpg)