Embed presentation
Download to read offline


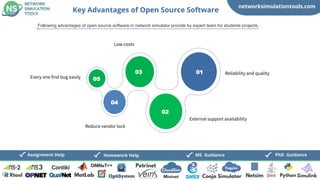



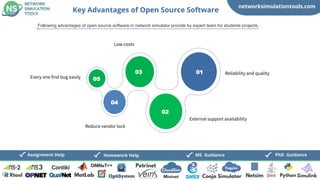
The document discusses network simulation tools, specifically highlighting CloudSim and FogSim, and offers guidance for PhD and MS students in their projects. It outlines the advantages of discrete event simulators and open source software, such as reliability, cost-effectiveness, and decision-making capabilities. Additionally, it provides contact information for further assistance with assignments and project help.