Embed presentation
Download to read offline



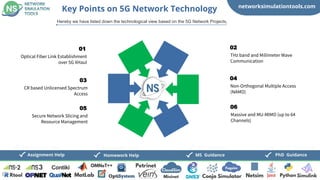
The document outlines various 5G network simulation tools and projects, highlighting key technologies and applications such as real-time video streaming and disaster management. It also details significant 5G simulation tools, including MATLAB and NS-3 based tools. Additionally, the document offers guidance for PhD and MS students regarding 5G projects and applications.